The Good | Two Cybercrime Leaders Face Justice for Fraud, Identity Theft & Extortion
Tyler Robert Buchanan, a 24-year-old British national believed to be a leader of the UNC3944 cybercrime group, has pleaded guilty in the U.S. to wire fraud and aggravated identity theft. Prosecutors say Buchanan and four accomplices stole at least $8 million in cryptocurrency by targeting employees at multiple organizations with SMS phishing attacks between 2021 and 2023. Victims were tricked into entering credentials on fake company login pages, allowing attackers to hijack email accounts, conduct SIM swaps, and drain cryptocurrency wallets.

Arrested in Spain in 2024 and extradited to the U.S. in last year, Buchanan now faces up to 22 years in prison at his sentencing this August. UNC3944 (aka 0ktapus, Scattered Spider) has historically been linked to major breaches at MGM Resorts International, Twilio, and Caesars Entertainment.
In a second guilty plea this week, Angelo Martino, a former ransomware negotiator at DigitalMint, has formally admitted to helping the BlackCat ransomware gang extort U.S. companies. Martino secretly shared clients’ confidential negotiation strategies and insurance policy limits with BlackCat operators, enabling them to demand larger ransoms. He also worked directly with other DigitalMint and Sygnia accomplices to launch ransomware attacks against multiple victims in 2023, targeting law firms, school districts, medical facilities, and financial firms. In one case, a victim paid over $25 million to settle the ransom.
Authorities have since seized $10 million in Martino’s assets, including cryptocurrency and luxury vehicles. He will also receive up to 20 years in prison when sentenced in July under the charge of conspiracy to and interference with interstate commerce by extortion as well as intentional damage to protected computers.
The Bad | Chinese-Linked Threat Actors Expand Botnets to Disguise Cyberattacks
The U.K.’s National Cyber Security Centre (NCSC-UK) and allied cyber agencies are warning that China-linked actors are increasingly relying on vast proxy networks of hijacked consumer devices to conceal cyberattacks and evade detection. A new joint statement details how the threat actors now route malicious traffic through compromised routers, cameras, recorders, and network-attached storage (NAS) devices instead of using rented infrastructure. This method means attacks are harder to trace since their geographic origins are masked.
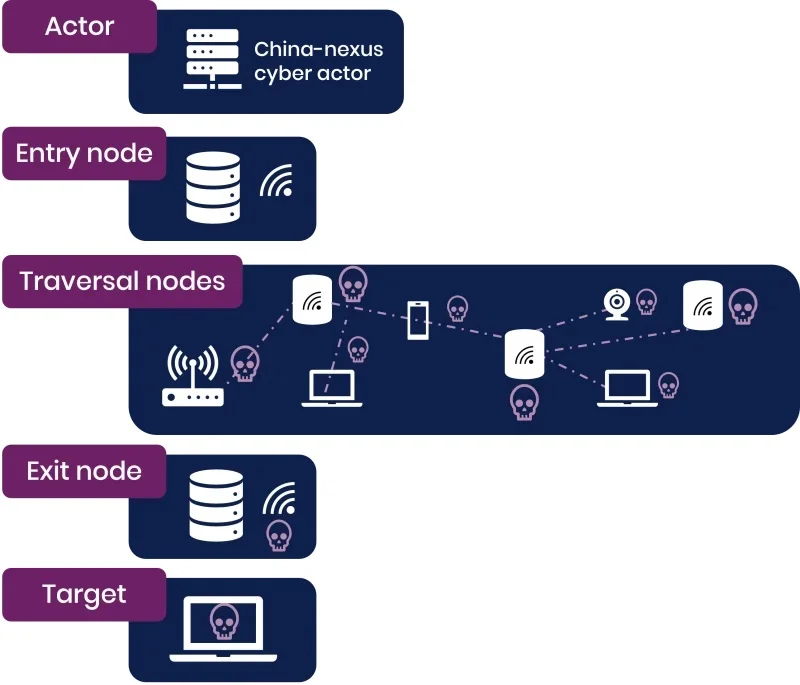
Officials say most China-nexus groups are now leveraging constantly shifting covert proxy networks, sometimes shared across multiple threat actors. These networks are mostly made up of Small Office Home Office (SOHO) routers, smart devices, and Internet of Things (IoT) devices. One example is a massive botnet called Raptor Train, which infected more than 260,000 devices in 2024 and was linked by the FBI to the state-backed Flax Typhoon and Integrity Technology Group, sanctioned back in January 2025. Another network, KV Botnet, has been tied to the PRC-backed Volt Typhoon group and targets vulnerable routers that no longer receive security updates. Though KV Botnet was disrupted by authorities in January 2024, Volt Typhoon actors began reviving it as of November that same year.
Authorities warn these botnets undermine traditional IP-blocking defenses because their infrastructure constantly changes. To reduce exposure, organizations are being urged to strengthen edge security by enforcing multi-factor authentication, maintaining updated inventories of internet-facing devices, using dynamic threat intelligence feeds, and adopting zero-trust controls. The advisory outlines the growing concern that everyday internet-connected devices are being weaponized at scale to support stealthy cyber operations targeting governments, telecom providers, defense contractors, and critical infrastructure worldwide.
The Ugly | ShadowBrokers Leak Links to Pre-Stuxnet Sabotage Framework
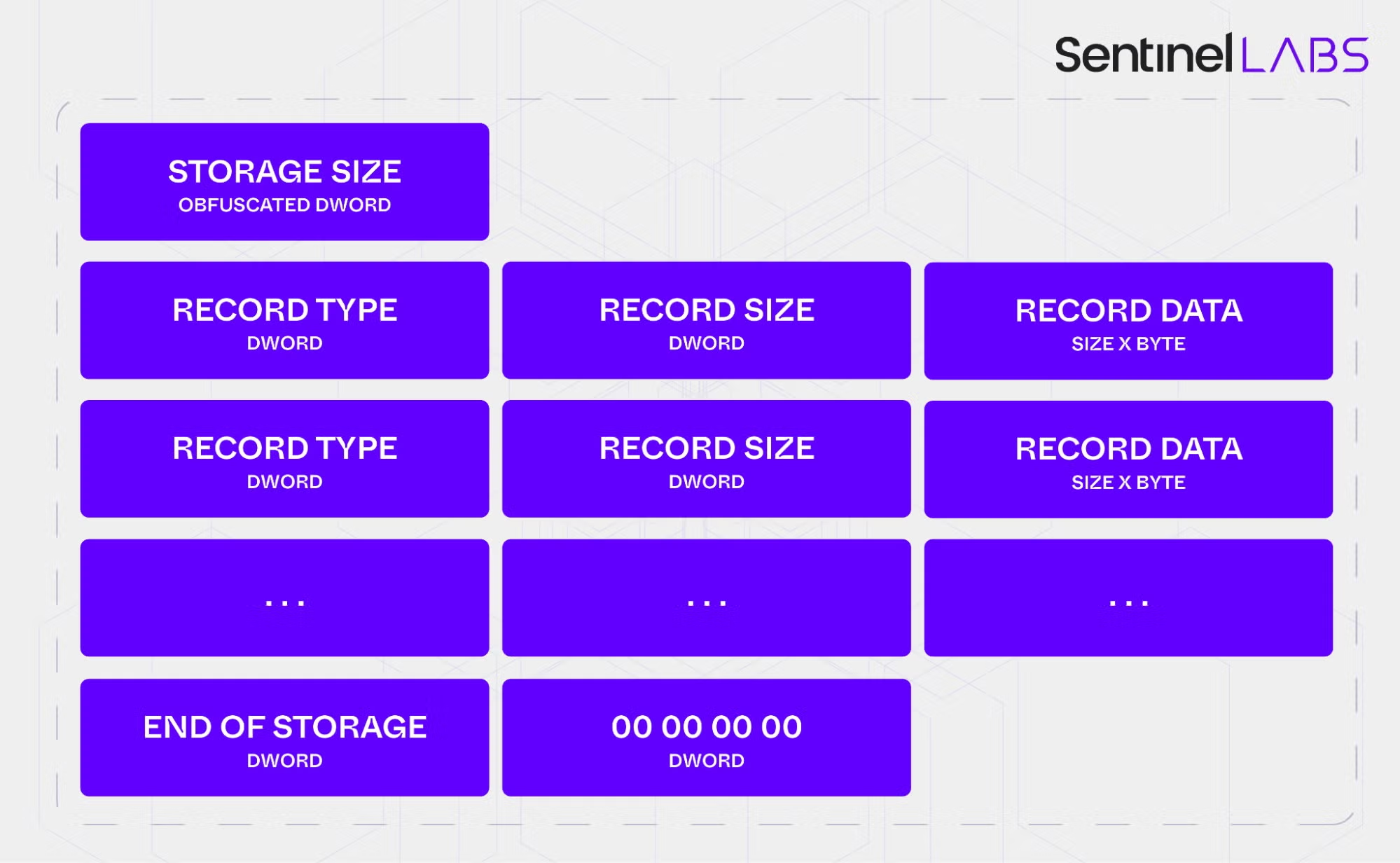
SentinelLABS has identified a previously undocumented cyber sabotage framework, tracked as “fast16”, with core components dating back to 2005. The operation centers on a kernel driver, fast16.sys, designed to intercept executable files in memory and subtly alter high-precision calculations to corrupt scientific and engineering outputs at scale.
The framework predates Stuxnet by at least five years and even early Flame-era tooling, making it one of the earliest known examples of a modular, Lua-based malware architecture. It was discovered alongside a companion service binary, svcmgmt.exe, which embeds a Lua virtual machine, encrypted bytecode, and system-level modules for propagation, persistence, and coordination across infected systems.
Unlike typical worms of its era, fast16 was engineered for targeted sabotage rather than indiscriminate spread. It selectively identifies compiled executables, particularly those using Intel toolchains, and injects rule-based modifications into floating-point computation routines.
SentinelLABS believes this could have introduced systematic errors into domains such as physics simulations, cryptographic research, and structural engineering models, effectively undermining high-value scientific workloads without obvious system failure. The carrier component also functions as a self-propagating wormlet (wormable payloads) platform, capable of deploying across networks using native Windows2000/XP services and weak administrative credentials.
SentinelLABS linked fast16.sys to the infamous ShadowBrokers leak from 2017 via deconfliction signatures used within advanced state-level tooling ecosystems by the NSA. Although full target attribution remains incomplete, analysis of matching code patterns suggests potential alignment with high-precision simulation software used in engineering and defense research.
The fast16 framework offers a rare early glimpse into real-world operations where kernel-level tampering, modular scripting, and precision sabotage logic were already converging. Although fast16 itself was built to run on now-obsolete operating systems, SentinelLABS discovery pushes back the accepted timeline on modern tradecraft, showing how well-resourced actors had been building long-lived implants that prefigured today’s state-backed cyber programs years earlier than previously thought.