RA Group Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is RA Group Ransomware?
RA Group emerged in April 2023. The RA Group ransomware payloads are derived and based off of Babuk and appear to be generated by the leaked Babuk builder toolset. The generated malware payloads are functionally similar to Babuk and contain commodity features such as VSS deletion.
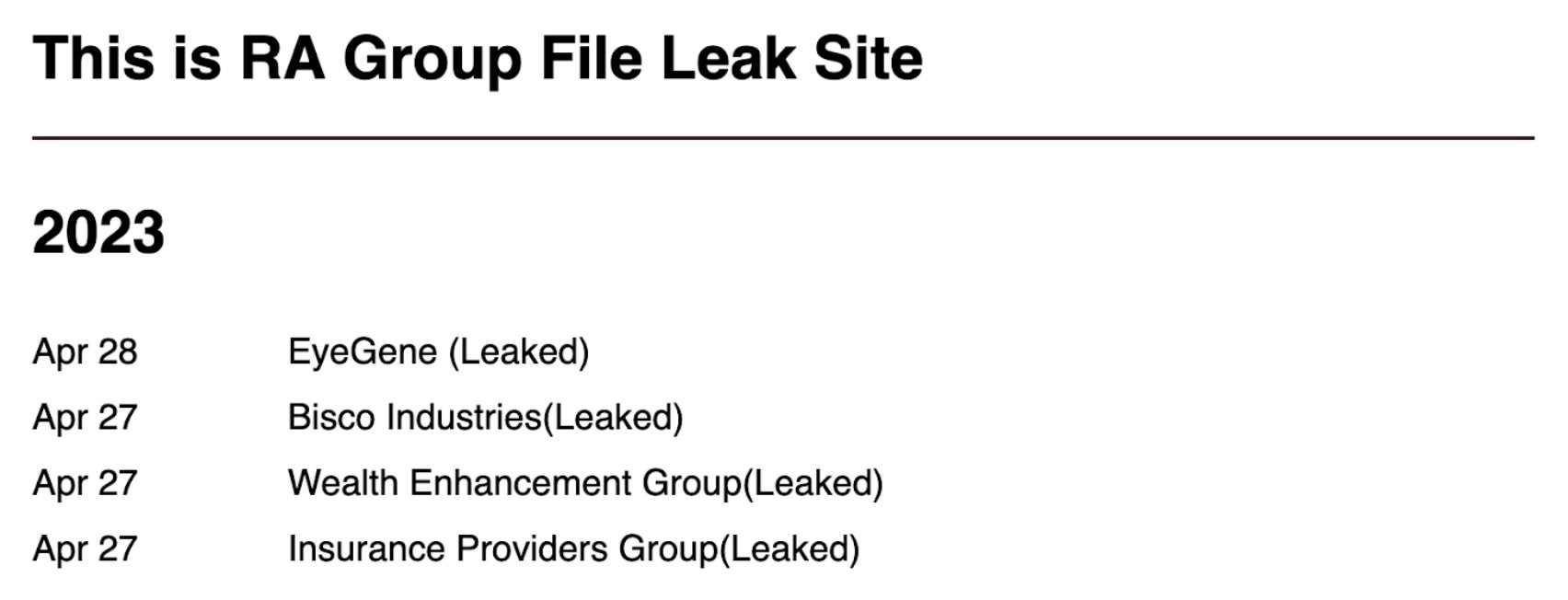
RA Group is a multi-extortion group. They threaten victims by publicly leaking data if they fail to pay the demanded ransom. The group has also been known to include strings in their malware which taunt or shame well-known security researchers. RA Group has a TOR (.onion) based website where they list victims and host exfiltrated data should they fail to comply with the ransom demands.
What Does RA Group Ransomware Target?
RA Group does not exclude specific industries or locations from their targeting. Current target industries include medical, insurance, and financial services.
How Does RA Group Ransomware Work?
Initial delivery of RA Group ransomware is handled via phishing email. The ransomware payloads have also been deployed via attack frameworks (e.g., BRc4, Cobalt Strike). RA Group ransomware payloads are derived from Babuk and appear to be generated by the leaked Babuk builder toolset. The code is similar to the 2021 “Multi.Babuk.c” source leaks. Further, the generated malware payloads are functionally similar to Babuk and contain commodity features such as VSS deletion. Along with VSS removal, RA Group payloads contain a hard-coded list of folders and processes to exclude. This is to prevent them from interfering with the encryption process.
RA Group ransom notes are target specific victims and can contain references to specific data or entities within that target. Firm timelines are provided for victims to contact the attackers. The group threatens to start leaking data after 3 days if there is no contact from the victim. After 7 days, the rest of the exfiltrated data is posted to the group data leak site (DLS).
The RA Group provides victims a sample file as proof of compromise, hosting said samples on gofile[.]io links – a free file sharing service.
How to Detect RA Group Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to RA Group Ransomware.
In case you do not have SentinelOne deployed, detecting RA Group ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect DarkBit ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate RA Group Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Repair or Rollback feature.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of RA Group ransomware attacks:
1. Educate Employees
Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
2. Implement Strong Passwords
Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
3. Enable Multi-factor Authentication
Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
4. Update and Patch Systems
Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
5. Implement Backup and Disaster Recovery
Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location.
The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
RA Group Ransomware FAQs
What is RA Group ransomware?
RA Group is a business network ransomware. After infecting your systems, it will encrypt and demand payment. Attackers steal data before encryption to allow for double extortion. RA Group attacks are planned and targeted, not arbitrary. When you are infected, you will be given a ransom note with contact and payment details.
Which industries and regions have been targeted by RA Group?
RA Group mainly attacks healthcare, manufacturing, finance, and technology companies. The attacks mainly occur in Western Europe and North America, but also increasingly in Asia and Australia. The group will attack companies with more than $100 million in revenues. They attack companies with important information that can’t afford downtime.
What encryption algorithms does RA Group ransomware utilise?
RA Group uses RSA-2048 to exchange keys and AES-256 to encrypt files. Each victim will be attacked using a different key. Your files will have the .ragroup file name extension. RA Group has partially encrypted large files so it can operate more effectively. The encryption is aimed at business-critical data like databases and financial reports.
How does RA Group ransomware propagate within networks?
RA Group spreads through hacked RDP connections and stolen VPN credentials. The attackers run PowerShell scripts and system tools to move sideways. They turn off Windows Defender and other security tools to avoid detection. They exploit network device vulnerabilities and plant backdoors for persistent access.
What programming language is the RA Group ransomware written in?
RA Group is coded in C# for Windows, based on the .NET Framework. It uses anti-analysis methods and virtual machine detection. The C# programming language provides ransomware with Windows API access to act on files. You will notice some parts coded in PowerShell to perform reconnaissance and lateral movement.
How can organisations detect an ongoing RA Group ransomware attack?
You can spot RA Group by monitoring for unusual admin tool usage like PsExec. Look for disabled security services or new admin accounts. The ransomware will cause high disk activity during encryption. There are network indicators when it contacts the command servers. Security tools can detect attempts to delete shadow copies and modify the registry.
What steps should be taken immediately after an RA Group ransomware infection?
If you suspect an RA Group infection, isolate affected systems at once. Activate your incident response process and reach out to authorities. Log ransom messages without negotiating. Some forensics specialists can assist you in determining the attack scope. You must reset all passwords from clean systems and look for backdoors left behind by attackers.