Project Relic Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is Project Relic Ransomware?
Project Relic is a multi-pronged extortion group operating as a semi-private Ransomware-as-a-Service (RaaS). The group emerged in mid-2022 with payloads written in Golang, targeting Windows hosts. Project Relic hosts a TOR-based data leak site (DLS) for distribution of non-compliant victim data. Victim communications are also handled over TOR via customized web-based chat portals. Affiliates are known to request ransom fees around and above the $2 million USD mark.
What Does Project Relic Ransomware Target?
Operating as a semi-private RaaS, victimology of affiliate operators will vary. That said, Project Relic operators have been observed targeting multiple critical industries, including medical, educational, and manufacturing entities.
How Does Project Relic Ransomware Work?
When launched, payloads will attempt to determine if specific security products are installed on the target host. This is done via querying of the %ProgramData%. The malware will also make attempts to determine if execution is being attempted in a sandbox or analysis environment via local WMIC queries.
Similar checks are also carried out to determine network connectivity. Presumably, if the malware determines it is running in an analysis environment, or certain network configuration requirements are not met, the payload will exit and not fully execute. File encryption will occur across accessible files in available and mapped drive volumes. This includes mapped network volumes already connected at the time of infection.
Additional WMIC queries are performed to obtain environment and contextual network data. For example:
SELECT Name, Workgroup FROM Win32_ComputerSystem
SELECT Caption, DomainName FROM Win32_NTDomain
Upon execution, Project Relic payloads will attempt to clear Windows event logs via the wevtutil.exe command. Payloads may contain over 1000 unique “wevtutil.exe cl” commands (clear log) tailored to specific applications or processes. These wevtutil.exe commands are launched in a hidden manner (hidden command.exe window). Examples include:
wevtutil cl Application
wevtutil cl Analytic
wevtutil cl AirSpaceChannel
wevtutil cl AMSI/Debug
wevtutil cl Microsoft-AppV-SharedPerformance/Analytic
wevtutil cl Microsoft-AppV-Client/Virtual Applications
wevtutil cl Microsoft-AppV-Client/Operational
wevtutil cl Microsoft-AppV-Client/Debug
wevtutil cl Microsoft-AppV-Client/Admin
wevtutil cl Microsoft-AppV-Client-Streamingux/Debug
wevtutil cl MF_MediaFoundationFrameServer
wevtutil cl Key Management Service
wevtutil cl Internet Explorer
wevtutil cl Intel-iaLPSS2-I2C/Performance
wevtutil cl Intel-iaLPSS2-I2C/Debug
wevtutil cl Intel-iaLPSS2-GPIO2/Performance
wevtutil cl Intel-iaLPSS2-GPIO2/Debug
wevtutil cl Intel-iaLPSS-I2C/Analytic
wevtutil cl Intel-iaLPSS-GPIO/Analytic
wevtutil cl IHM_DebugChannel
wevtutil cl HardwareEvents
wevtutil cl General Logging
wevtutil cl Microsoft-User Experience Virt
Individual file encryption is achieved via ChaCha20, a stand-alone stream cipher. The standard chacha20 Golang package is utilized in observed Project Relic payload samples. Each file is encrypted via keystream in accordance with machine architecture and using a unique keysteam for each file.
Project Relic ransom notes are written in HTML format to folders containing encrypted items. The ransom note follows a hard coded format which begins with “UNLOCK_FILES” followed by a unique string, specific to the campaign ID associated with the payload sample. An example of this is “UNLOCK_FILES.306624E70F2C279F.HTML”.
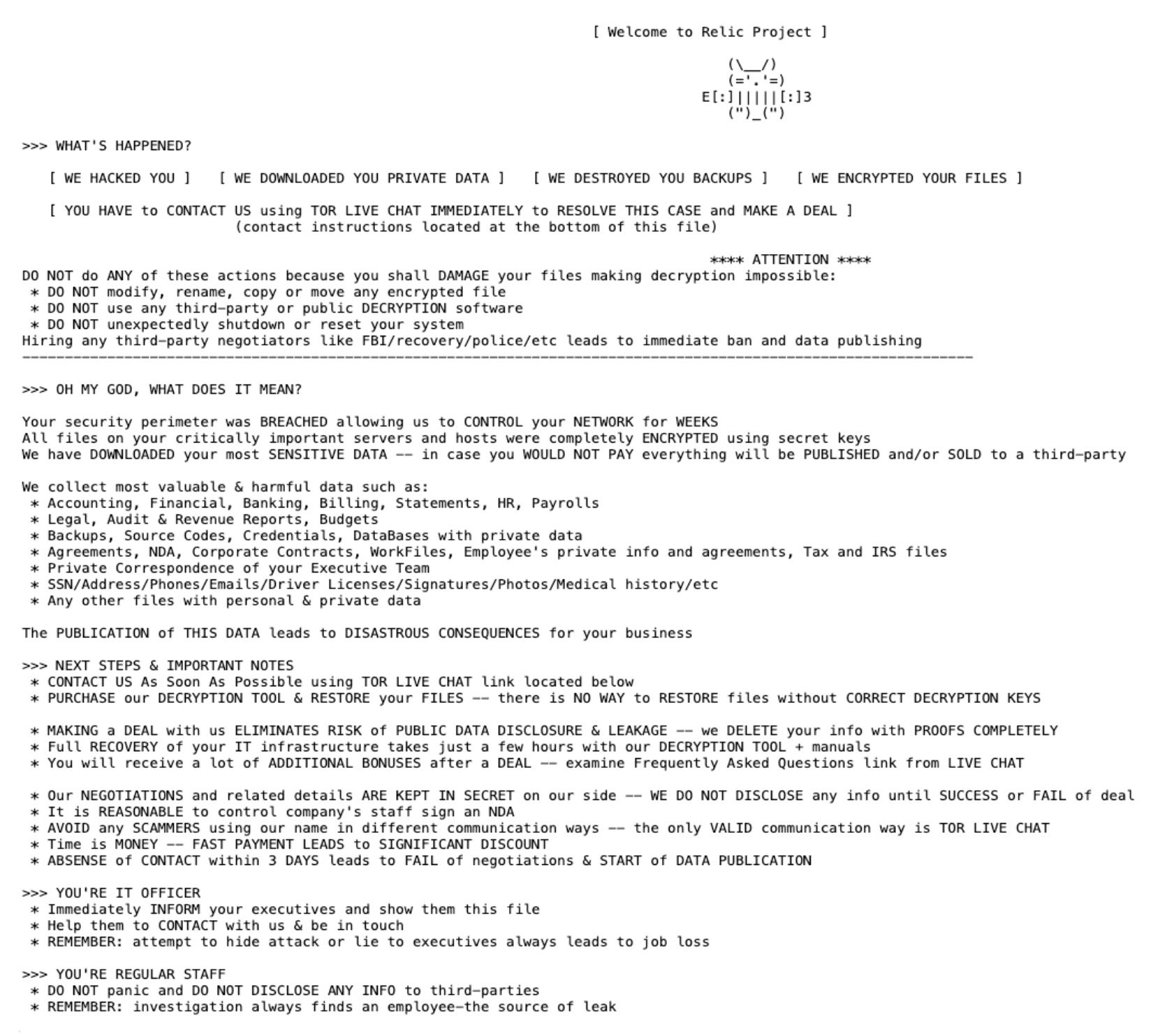
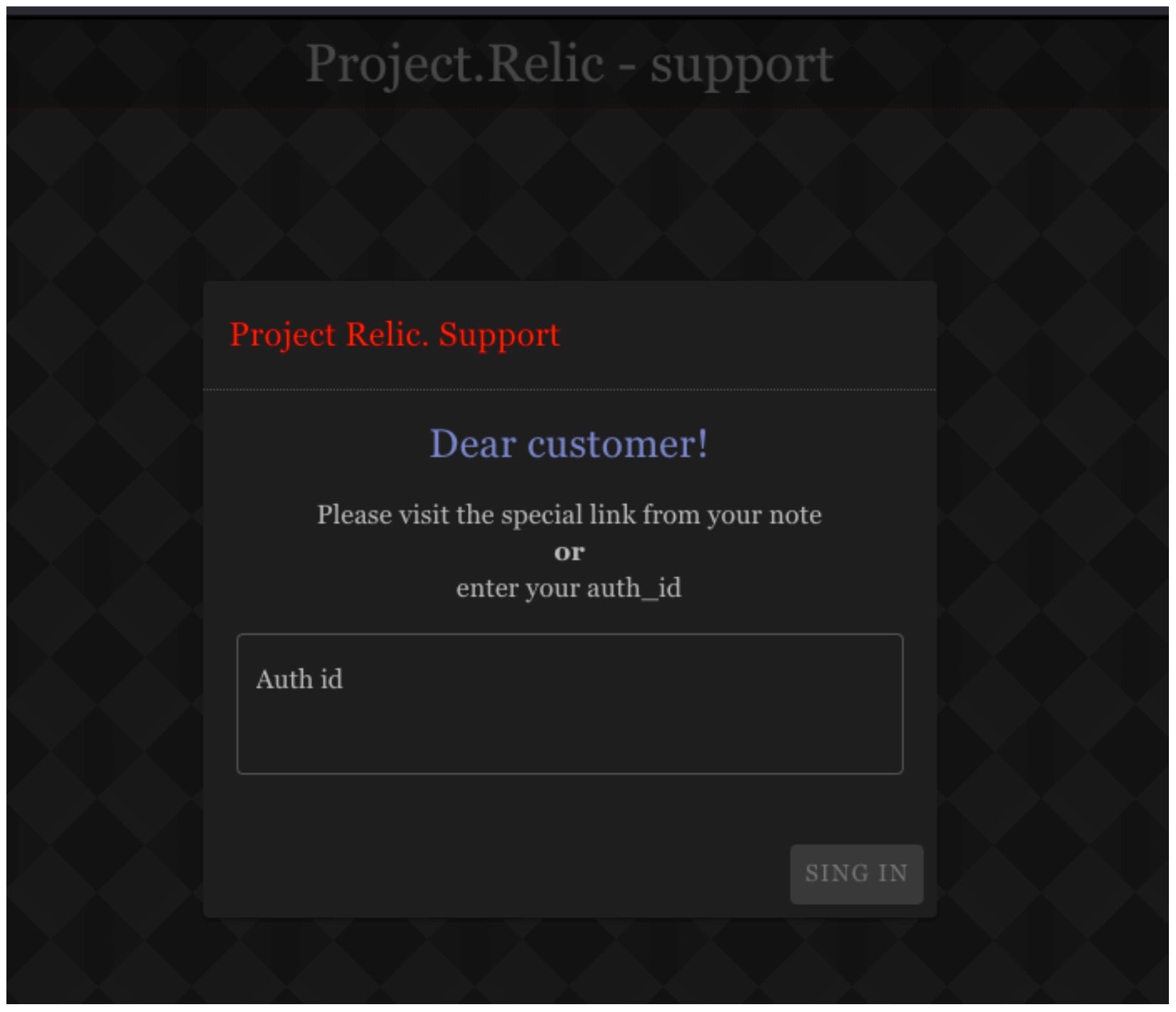
Victims are instructed to contact their attacker via customized or dynamically generated TOR-based websites.
How to Detect Project Relic Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to Project Relic Ransomware.
In case you do not have SentinelOne deployed, detecting Project Relic Ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect Project Relic Ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate Project Relic Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Quarantine or Repair.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of Project Relic Ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
- Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
Project Relic Ransomware FAQs
What is Project Relic ransomware?
Project Relic is a ransomware strain that showed up in late 2022. It attacks both Windows and Linux systems and uses advanced evasion methods. If you’re targeted, they will encrypt your data and demand payment through their dark web portal. Project Relic operates as Ransomware-as-a-Service where developers work with affiliates to launch attacks.
What is unique about Project Relic's ransom notes?
Project Relic’s ransom notes contain unique victim IDs and are customized for each target. You’ll find detailed instructions on how to contact them through a Tor portal, with specific deadlines before they publish your data. They will often include your organization’s name in the note to make it more threatening.
How does Project Relic operate?
Project Relic operators first break into your network using various methods. They will move through your systems, steal valuable data, and disable security tools. They typically spend days or weeks inside your network before launching encryption. If you don’t notice them during this phase, you’ll lose both data and money.
How does Project Relic encrypt files?
Project Relic uses AES-256 to encrypt your files and RSA-2048 to protect the encryption key. It targets specific file types and avoids system files so your computer stays running. It will encrypt files on local drives, network shares, and even cloud storage if you have it mounted as a drive on infected systems.
What methods does Project Relic use to evade detection?
Project Relic hides using code obfuscation and can detect virtual machines or sandboxes. It will disable your security software, delete shadow copies, and use legitimate Windows tools for its dirty work. If you’re not watching closely, it can inject into trusted processes to hide its activities from security monitoring.
What are indicators of compromise (IOCs) for Project Relic?
You can identify Project Relic by finding ransom notes named “README_RECOVER.txt” in encrypted folders. Your files will have the .relic extension added. Look for PowerShell scripts disabling security tools and network connections to Tor. If you see new admin accounts or unusual credential use, you might be infected.
How can organizations detect Project Relic ransomware?
You can detect Project Relic by setting up network monitoring for unusual data transfers. Use SentinelOne Singularity XDR Platform to spot suspicious behaviors and configure alerts for mass file modifications. You should watch for security tools being disabled and track administrative credential use across your network to catch attackers early.
What preventive measures can organizations implement?
You should segment your network, use multi-factor authentication, and limit access permissions. Make regular offline backups that attackers can’t reach. Train your employees to spot phishing attempts. If you have RDP, you need to secure it or disable it when not needed. Keep all your systems updated with security patches.