Kasseika Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is Kasseika Ransomware?
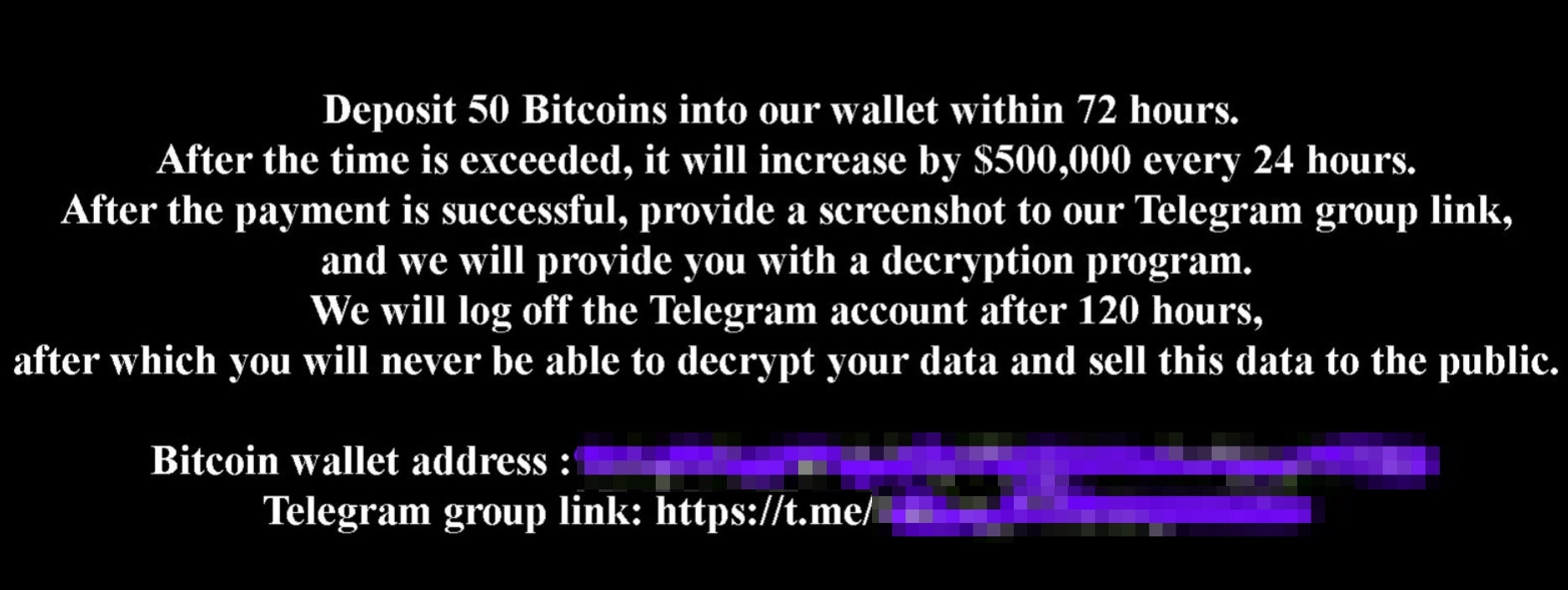
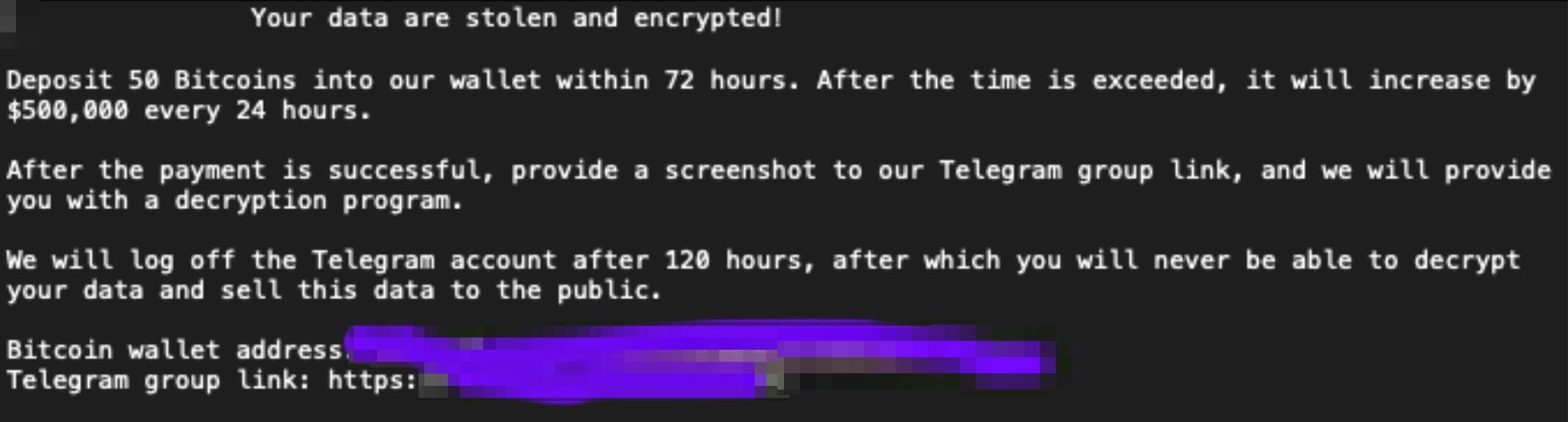
Kasseika Ransomare emerged in late 2023 with threat actors operating a shared Telegram channel for victim and campaign interactions. Some code-reuse and TTP overlaps indicate an affiliation of some degree between Kasseika and BlackMatter ransomware operations. Victims are instructed to pay via Bitcoin, with all communications being directed at the aforementioned Telegram account. The group does not currently host a DLS (Data Leak Site).
What Does Kasseika Ransomware Target?
Kasseika Ransomware is sold openly as a full service, inclusive of payloads and tooling. Victimology will vary depending on the specific operator or affiliate. In the past, Kasseika ransomware has targeted small to medium-sized businesses (SMBs) as well as large enterprise targets.
How Does Kasseika Ransomware Work?
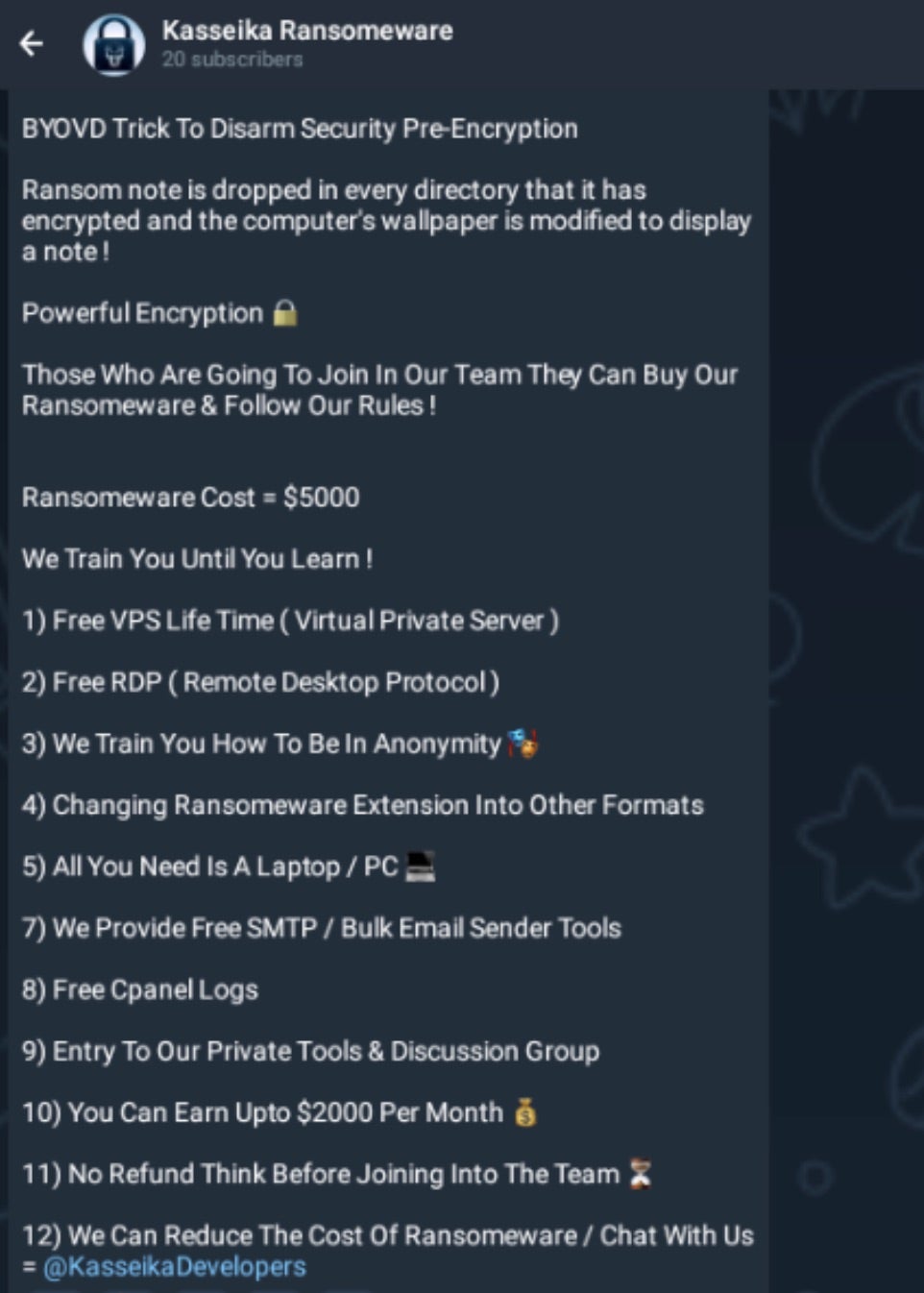
Kasseika is currently sold via Telegram channels. The vendors offer the whole service, including training and infrastructure for $5000 USD.
The sellers attempt to differentiate themselves by offering training and turnkey infrastructure along with the tools themselves. The VirIT Agent System-based BYOD tactic is part of the service they offer, referred to as a “BYOVD Trick” in the groups advertisements.
Kasseika Ransomware advertisements offer the following services as shown:
Kasseika ransomware is delivered via phishing email. Its payloads have been observed being attacked directly to phishing email messages. However, we have also observed more ‘tired’ attacks, where remote access trojans (RATs) and specialized tools, such as PsExec, have been deployed prior to the delivery and execution of the final Kasseika payloads.
Kasseika threat actors are known to utilize PsExec for remote execution of the ransomware payouts. Attackers have also leveraged components of VirIT Agent System (developed by TG Soft) to disable specific security tools. This is a BYOD style attack meant to disable processes which may inhibit the attackers from their final goal, namely encryption or exfiltration.
Kasseika will attempt to terminate and/or disable multiple applications that may interfere with the encryption process. Via the BYOD attack (Martini.sys driver from the VirIT Agent System software), the ransomware will create a service capable of terminating a large set of processes known to be associated with legacy antivirus or other security tools.
Further analysis and detection evasion is achieved via detection of specific processes, and if found, the ransomware will self-terminate. These processes include tools like RegMon, FileMon, OLLYDBG, ProcMon, Kernel Detective, and similar. This is done by both checking for open windows (FindWindowA) with associated titles, as well as via string matching in the Windows registry. Kasseika will also attempt to detect when being executed in a sandbox/analysis environment and also subsequently self-terminate. This includes the detection of Comodo Sandbox, Sandboxie, and VirtualBox in general.
Kesseika payloads are delivered as 32-bit, Themida-packed Windows executables. The ransomware is able to encrypt files without local administrator privilege. However, some of the more invasive behaviors, Volume Shadow Copy removal for example, do require administrative context.
File encryption is achieved via a combination of RSA and a modified ChaCha20 matrix. Volume Shadow Copy manipulation is achieved via WMIC (SELECT * Win32_ShadowCopies). The ransomware will also attempt to clear portions of the Windows event log. This is done via WEVTUTIL.EXE, targeting the System, Security, and Application logs. It should be noted that the Event Log removal and VSS manipulation are not reliably reproducible in the analyzed samples of Kasseika.
Following encryption, the victim’s desktop wallpaper will be modified to display the attacker’s ransom note. The ransom note contains contact information (i.e., BTC payment address) along with the Telegram group link. Text copies of the ransom note are also written to each directory continuing affected items.
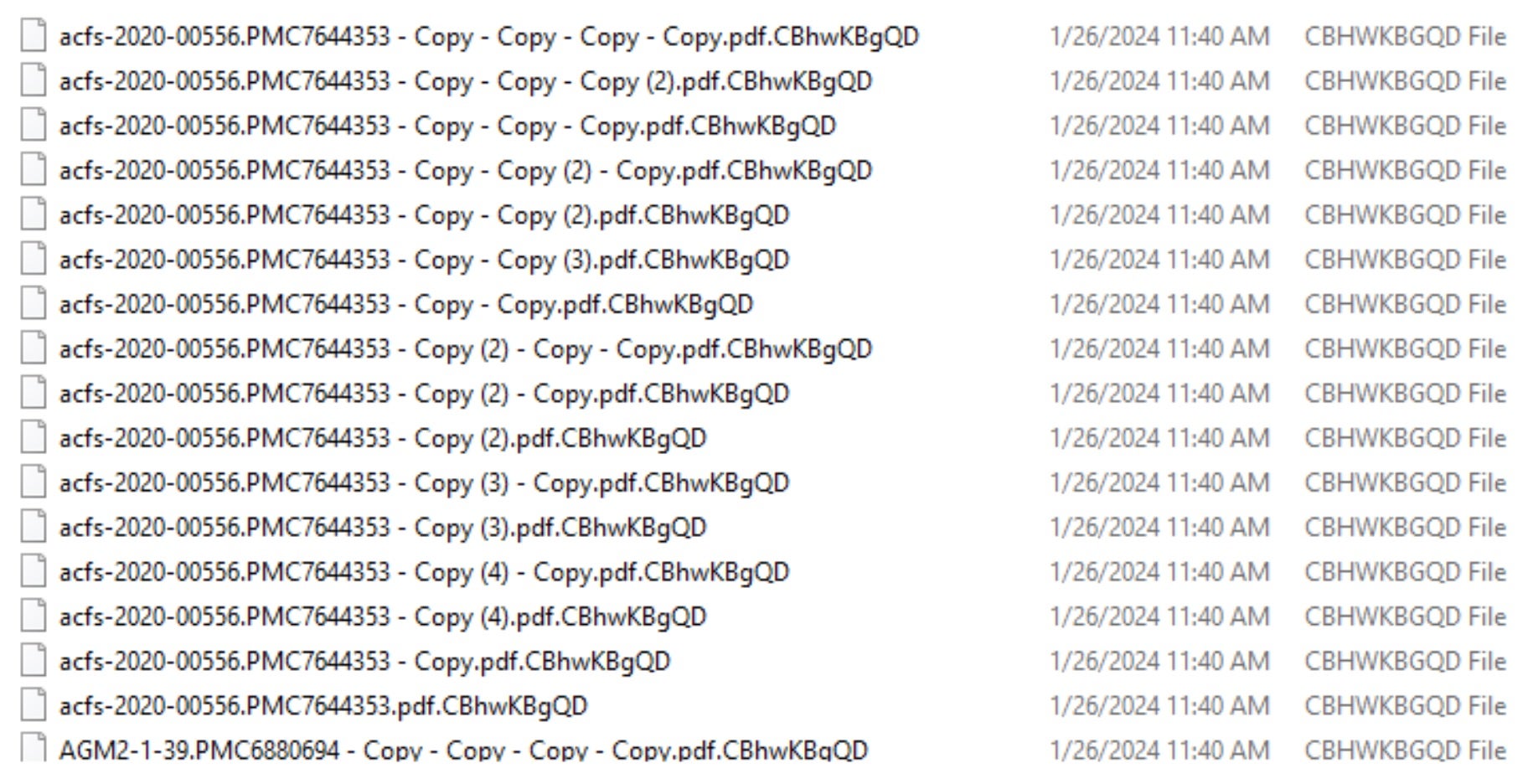
Encrypted files will have the payload-specific extension appended to them.
How to Detect Kasseika Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to Kasseika Ransomware.
In case you do not have SentinelOne deployed, detecting Kasseika Ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect Kasseika Ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate Kasseika Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Quarantine or Repair.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of Kasseika Ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
- Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
Kasseika Ransomware FAQs
What is Kasseika ransomware?
Kasseika is a recently uncovered ransomware operation first discovered in December 2023. It turns off antivirus software before encrypting files using Bring Your Vulnerable Driver tactics. They will abuse the Martini driver from TG Soft’s VirtIT Agent System to shut down security products on your system. You can see it as a sophisticated threat requiring immediate attention.
What encryption methods are used by Kasseika ransomware?
The search results don’t provide specific details about Kasseika’s encryption methods. However, before encryption begins, you’ll see Kasseika disable antivirus products using the vulnerable Martini driver. They will first focus on removing security obstacles through BYOVD tactics, then proceed with file encryption. If you’re investigating, look for signs of driver exploitation.
Is Kasseika ransomware targeting Windows, Linux, or both?
Kasseika ransomware is predominantly Windows-based. The Windows-specific attack chain consists of Windows features like PsExec and utilises the Martini driver specific to Windows. We do not have any details of Linux targeting. If you are concerned about Kasseika attacks, you must highlight Windows security measures.
What are Kasseika's strategies and mechanisms for escalating privilege or surviving?
Kasseika employs the compromised driver Martini (Martini.sys/viragt64. sys) to escalate privileges. They will leverage vulnerabilities in this loaded driver to get privileges to terminate security processes. Windows PsExec is employed to run malicious .bat files, as seen. If you are vigilant and look out for these tools, you could intercept Kasseika before it is fully rolled out.
What are the indicators of compromise (IOCs) of Kasseika ransomware?
IOCs for Kasseika are the existence of Martini.sys or viragt64.sys drivers, running malicious .bat scripts and killing security-related processes. You need to search for suspicious use of PsExec and Martini service creations. If you notice these signs, they will indicate a likely Kasseika infection in action.
How do organisations detect an initial Kasseika ransomware infection?
You can detect Kasseika early by checking for installing and downloading of the Martini driver, using PsExec, and the abnormal termination of security processes. Check for the activity of trying to kill nearly 991 different processes from Kasseika’s hardcoded list. With good logging and monitoring, these processes will be suspicious.
What are the best prevention strategies against Kasseika ransomware?
You must filter emails to avoid phishing attacks, restrict administrative rights, and monitor unauthorised driver installs. Update systems with patches and implement an application that allows listing. Where your employees have been trained on how phishing works, they are not likely to supply the initial access Kasseika operators demand.
Can endpoint detection and response (EDR) products identify Kasseika activity?
EDR products can potentially detect Kasseika activity if configured to monitor for driver exploitation and kill activity. Remember, though, that Kasseika is explicitly designed to target security products for termination. If you’re only using EDR, they’ll attempt to turn it off via the Martini driver before encrypting.
What can victims do when they first learn about Kasseika ransomware?
You need to quarantine the affected systems from the network immediately to prevent lateral movement. Document all indicators of compromise and engage your incident response team. If recent backups are available, have them ready for restoration. You must also report the incident to the police and consult ransomware specialists.