Sugar RaaS (Ransomware): In-Depth Analysis, Detection, and Mitigation
Summary of Sugar RaaS (Ransomware)
Sugar Ransomware is a Ransomware-as-a-Service (RaaS) operation first detected by the Walmart Security Team in November 2021, has since gained momentum in its attacks. The ransomware gets its name from the affiliate site ‘sugarpanel[.]space’.
Sugar (aka SugarLocker) is considered to be a low-sophistication ransomware and it is distributed through various methods such as phishing emails and watering-hole-style attacks, which lure victims into downloading trojanized payloads. The samples of this ransomware are written in Delphi and are designed to masquerade as the artifacts of more prominent ransomware families. The Sugar RaaS campaigns are focused on individuals or small to medium-sized businesses.
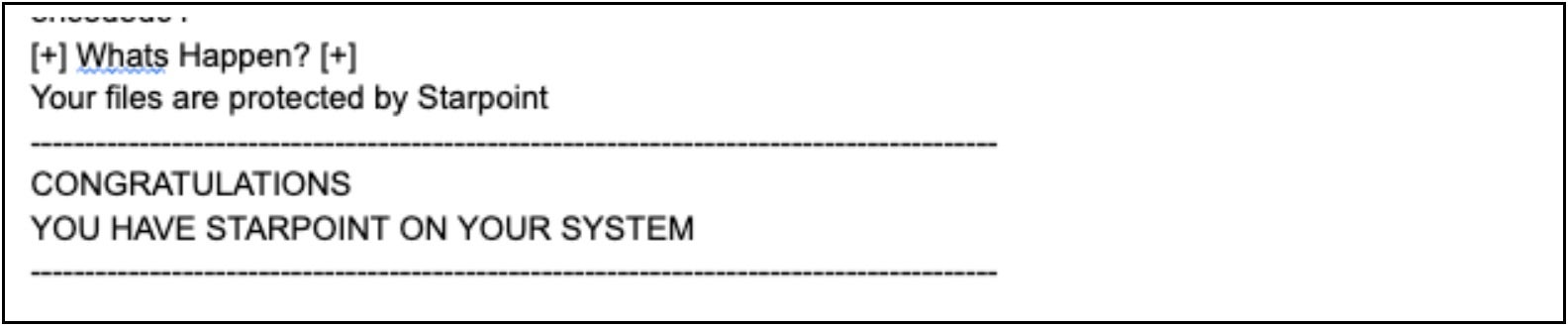
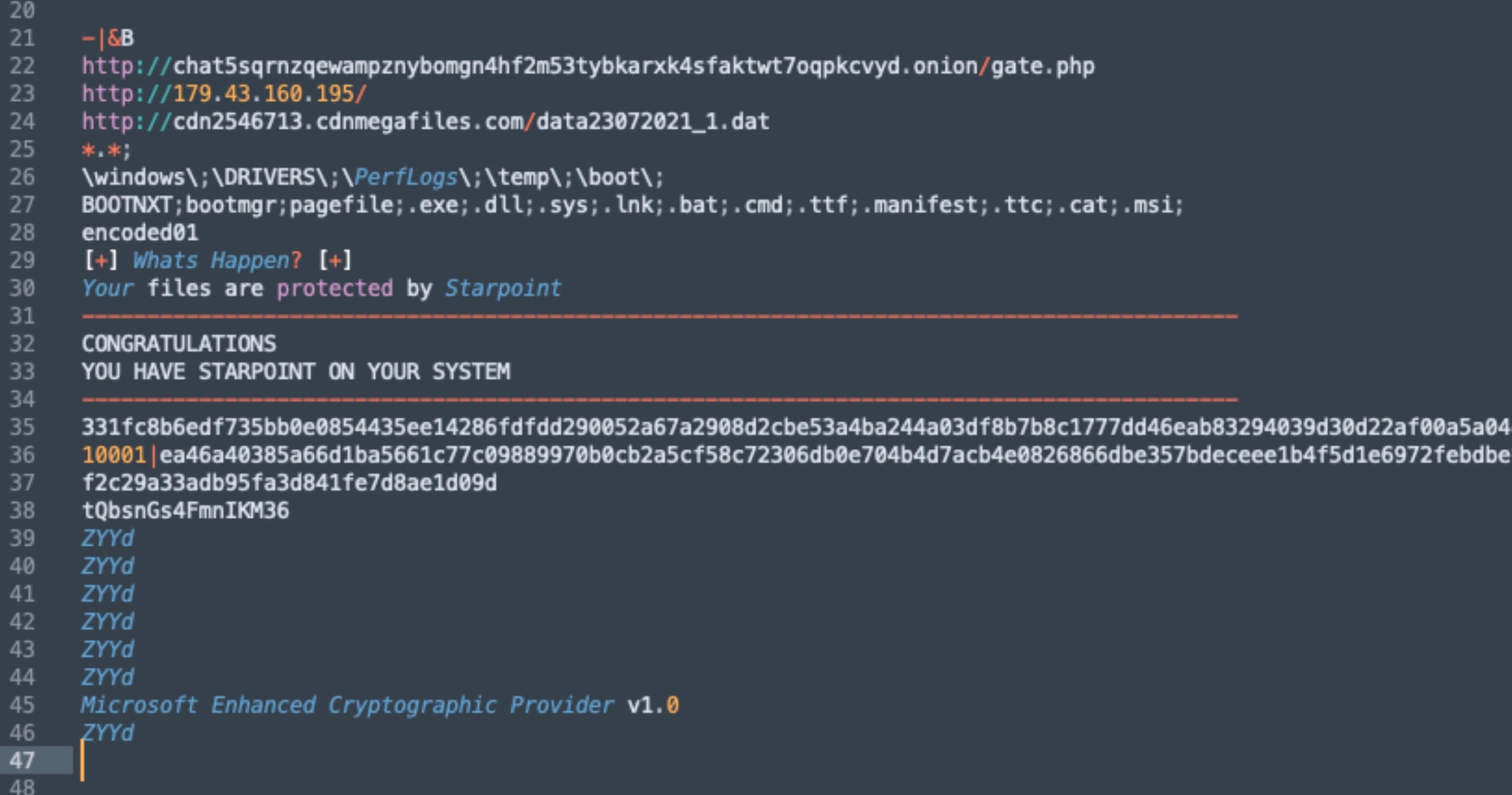
Update: Between December 2024 and January 2025, Sugar RaaS operators/affiliates were observed deploying a new variation (re-brand) of ransomware payloads. This new version of the group’s ransomware is dubbed “Starpoint”. Ransom notes and associated artifacts were also updated to reflect this new name/branding.
Starpoint payloads are functionally identical to previous Sugar RaaS ransomware payloads. Starpoint ransomware payloads will attempt to locate and encrypt all available data files whilst excluding .exe, .dll, .sys, .lnk, .bat, .cmd, .ttf, .manifest, .ttc, .cat, and .msi files from encryption. The pagefile and BOOTMGR files are excluded as well. Ransom notes and dropped artifacts are updated to reflect the Starpoint name.
What Does Sugar Ransomware Target?
Sugar RaaS campaigns target individuals and SMBs (small or medium-sized businesses).
How Does Sugar Ransomware Spread?
Sugar RaaS payloads are delivered via email and phishing attempts.
Malicious attachments such as Word documents or JavaScript files are sent to the target, typically in the form of a business invoice or a payment reminder. The attachment contains a malicious macro or JavaScript code which, when opened, downloads and installs the ransomware onto the victim’s system.
Sugar Ransomware can also be spread through malicious links embedded in emails, social media posts, and on websites. These links prompt the user to download an executable file that contains the ransomware payload. The ransomware is then installed on the computer, encrypting the user’s data.
In addition, Sugar Ransomware can be spread through malicious advertisements, drive-by downloads, malicious software bundlers, and exploit kits. These methods allow the ransomware to be installed on a target system without the user’s knowledge or consent.
Sugar RaaS Ransomware Technical Details
Sugar (aka Encoded01) Ransomware-as-a-Service (RaaS) is written in Delphi and attempts to masquerade as a part of much larger ransomware families, like REvil. Sugar payloads are obfuscated using a modified version of the RC4 algorithm. It attempts to encrypt all files on a victim’s device but does not remove any of their recovery options or backup services, like Volume Shadow Copy Service (VSS).
Indicators of Compromise (IoC)
4585f8f353da6b50c094e6c01be588ce90961e8b Starpoint ransomware
73e74f9ab0a027b97cfe46e1926d21528a88cf89 Starpoint ransomware
chat5sqrnzqewampznybomgn4hf2m53tybkarxk4sfaktwt7oqpkcvyd[.]onion
cdn2546713[.]cdnmegafiles[.]com
179[.]43.160.195
How to Detect Sugar RaaS Ransomware
- The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to Sugar RaaS.
In case you do not have SentinelOne deployed, detecting this ransomware requires a combination of technical and operational measures, which are designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
- Use antimalware software, or other security tools, which are capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic, and look for indicators of compromise, such as unusual network traffic patterns, or communication with known command-and-control servers.
- Conduct regular security audits and assessments, to identify vulnerabilities in the network and the system, and to ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including how to identify and report suspicious emails, or other threats.
- Implement a robust backup and recovery plan, to ensure that the organization has a copy of its data, and can restore it in case of an attack.
How to Mitigate Sugar RaaS Ransomware
- The SentinelOne Singularity XDR Platform can return systems to their original state using either the Repair or Rollback feature.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
Sugar Ransomware FAQs
What is Sugar Ransomware?
Think of Sugar Ransomware like a sneaky digital lock that scrambles your files. Attackers use it to grab control of your data so they can demand money. It acts silently, often slipping into computers through suspicious links or harmful email attachments. Once it’s in, it can spread and hold your information hostage. You can stay safe by keeping your systems patched and being wary of unknown downloads or messages.
What types of files does Sugar Ransomware encrypt?
Sugar Ransomware usually scrambles a wide range of files, including photos, documents, spreadsheets, and even database archives. It doesn’t care if you’re storing personal memories or important business data—everything becomes locked and unusable. The attackers then ask for payment, hoping victims will pay to unlock their files. You can help prevent this nightmare by keeping backups and staying cautious around suspicious links or emails.
Does Sugar Ransomware steal data before encryption?
Researchers believe some versions of Sugar Ransomware may grab files before locking them, but this isn’t always guaranteed. It depends on how the malware is programmed or what features the hackers include. The risk is that stolen information could be sold or leaked, adding extra pressure for victims to pay. You can lessen the chance of data theft by restricting network access and monitoring any unusual activity.
What security best practices help prevent Sugar Ransomware infections?
Use layered protection by installing reputable antivirus programs and firewalls, then keep everything patched against known flaws. Make it a habit to create regular backups and store them offline. Train everyone who uses the network to identify risky links or messages, and ensure passwords are strong and unique. You can also limit who can access important data and watch for odd activity on your systems.
Can endpoint detection and response (EDR) solutions stop Sugar Ransomware?
EDR tools can catch suspicious behavior early, giving you a heads-up before Sugar Ransomware can lock your files. They keep track of unexpected changes, block harmful software, and record what’s happening on each device. While they’re not perfect, they do make life harder for criminals trying to slip in unnoticed. You can boost your defenses even more by combining EDR with frequent backups and other security layers.
Can Sugar Ransomware spread laterally across a network?
Sugar Ransomware can move from one computer to another if it finds weak passwords, open file shares, or vulnerable settings on a network. Once it gains a foothold, it may jump between connected devices and lock even more files. You can limit this spread by segmenting your network, reviewing user permissions, and monitoring logs for weird activity. The fewer open doors you have, the harder it is to hop around.