What Is LDAP Injection?
LDAP injection is a server-side attack that exploits web applications constructing Lightweight Directory Access Protocol queries from unsanitized user input. When your application fails to properly neutralize special characters before incorporating them into LDAP queries, attackers can manipulate those queries to bypass authentication, extract sensitive directory data, or modify entries within the LDAP tree.
LDAP directories sit at the heart of enterprise identity infrastructure. They store user credentials, group memberships, access control lists, organizational structures, and service account details. A single successful LDAP injection attack can expose this repository, granting an attacker the keys to your authentication infrastructure.
MITRE classifies this vulnerability as MITRE CWE-90: Improper Neutralization of Special Elements used in an LDAP Query. OWASP lists it under OWASP Injection and the updated OWASP Injection category. The vulnerability shares its root cause with SQL injection, but targets a fundamentally different and often more consequential system: the directory service that governs who can access what across your entire organization.
Understanding how LDAP injection works requires knowing the query syntax attackers exploit.
How Does LDAP Injection Work?
LDAP search filters follow a specific grammar defined in LDAP syntax. Filters use Polish notation (prefix notation), where a simple authentication query looks like this:
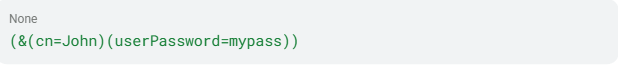
The & operator performs a Boolean AND. Parentheses group conditions. The * wildcard matches any value. These metacharacters, along with | (OR), ! (NOT), =, ~=, >=, <=, and () grouping operators, form the injection surface.
When a developer constructs a filter by concatenating user input directly into the query string, those metacharacters become weapons. If a login form inserts the username straight into a filter like (&(uid=INPUT)(userPassword=HASH)), an attacker who submits crafted metacharacters can change the filter's logic entirely: bypassing authentication, returning all directory entries, or extracting data one character at a time.
The specific technique an attacker uses depends on the type of LDAP injection.
Types of LDAP Injection
LDAP injection takes several distinct forms, each targeting a different aspect of how applications interact with the directory. The type an attacker uses depends on the application's behavior, the query context, and what the attacker can observe in the response.
| Type | Technique | Consequence |
| Search filter injection | Wildcard or OR-based filter manipulation | Full directory enumeration |
| Authentication bypass | Always-true filter injection | Unauthorized login as any user |
| Blind LDAP injection | Character-by-character differential analysis | Silent data extraction |
| DN manipulation | Wrong escaping context applied to DN fields | Injection in non-filter query components |
Search Filter Injection
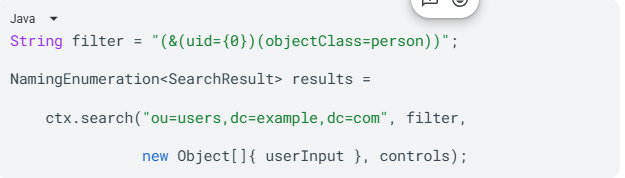
Consider this vulnerable Java code:

If an attacker submits user=*, the resulting filter becomes (cn=*), which matches every object in the directory with a cn attribute. Your application returns the entire user directory instead of a single record.
Authentication Bypass
LDAP authentication flows represent the highest-consequence injection target. A vulnerable login filter like this:
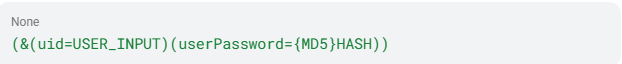
This filter can be bypassed by injecting )(uid=))(|(uid=* as the username. The resulting filter evaluates to always-true, granting the attacker authenticated status as the first user in the LDAP tree, often an administrator account. The testing guide documents this as the direct analog to SQL injection authentication bypass techniques.
Blind LDAP Injection
When applications do not surface query results directly, attackers use differential responses to extract data. By injecting filter conditions like (attribute=a*), (attribute=b*), and observing whether the application returns a result or an empty page, they extract attribute values character by character. Research presented in the Black Hat paper demonstrated that client-side filters limiting displayed information do not prevent blind injection techniques.
Distinguished Name Manipulation
LDAP has distinct escaping contexts, and confusing them creates injection vectors. Search filters require escaping per RFC 4515 (*→\2a, (→\28, )→\29). Distinguished Names (DNs) require escaping per RFC 2253 (\, #, +, <, >, ,, ;, ", =). Applying the wrong escaping context to the wrong field leaves your application vulnerable even when you think you have addressed the issue.
These attack types share common root causes that go deeper than syntax.
Causes of LDAP Injection
LDAP injection vulnerabilities stem from a combination of coding practices, library limitations, and infrastructure misconfigurations. Each root cause creates an independent path to exploitation.
- Direct string concatenation. The proximate cause in nearly every LDAP injection vulnerability is user-controlled data concatenated directly into LDAP filter strings at the application layer. LDAP libraries have historically lacked built-in parameterized query support, requiring developers to follow manual guidance for safe query construction. Parameterized interfaces exist but require deliberate adoption.
- Special character mismanagement. Applications that attempt input validation often implement incomplete denylists that miss dangerous characters. A denylist blocking * and ( but missing ) or NUL bytes still leaves an exploitable gap. MITRE CWE-90 identifies LDAP injection as resultant to this failure, meaning the injection vulnerability arises directly from the underlying mismanagement of special characters.
- Escaping context confusion. The LDAP cheat sheet documents that applying search filter escaping to DN fields, or DN escaping to search filter fields, creates injection vectors through incorrect context selection. If your developers know they need to escape but choose the wrong function, your application remains vulnerable.
- Anonymous and unauthenticated bind configurations. LDAP servers configured to allow anonymous bind let attackers bypass bind authentication entirely.
- Widespread use of LDAP for authentication. LDAP's role as the authentication backbone for enterprise environments means injection against login flows yields the highest-consequence outcome: authenticated access to enterprise-wide resources. The attack surface is enterprise-wide by architectural design.
These causes combine to create risks that extend far beyond a single compromised query.
Impact and Risk of LDAP Injection
LDAP injection attacks can produce several categories of business impact, each escalating in severity.
Authentication Bypass
An always-true filter injection grants immediate authenticated access. CVE-2023-4501 in OpenText Enterprise Server allowed authentication to succeed with any valid username regardless of whether the password was correct, and may also succeed with an invalid username and any password. This affected enterprise COBOL development and runtime environments deployed in financial services, insurance, and government.
Sensitive Data Exfiltration
LDAP directories contain user credentials, password hashes, email addresses, organizational hierarchies, group memberships, ACLs, computer accounts, and security identifiers. A CISA advisory documented a single LDAP query retrieving information about users, computers, groups, ACLs, OUs, and GPOs from an enterprise directory.
Privilege Escalation
Successful injection can grant permissions to unauthorized queries and enable content modification inside the LDAP tree. CVE-2026-31828 in Parse Server allowed authenticated low-privilege users to escalate to any restricted group through LDAP filter injection.
Denial of Service
CVE-2025-12764 (pgAdmin) demonstrated LDAP injection weaponized to force the DC/LDAP server and client to process an unusual amount of data, causing a denial of service against directory infrastructure with cascading authentication failures.
Lateral Movement Enablement
LDAP enumeration feeds Active Directory reconnaissance. The CISA red team advisory documented that LDAP data enabled mapping of users, computers, groups, ACLs, OUs, and GPOs, all of which serve as inputs for lateral movement planning. The assessed enterprise had zero visibility for this activity.
OWASP rates injection exploitability at 3 (Easy) and technical impact at 3 (Severe) in its OWASP framework. LDAP injection also carries direct compliance consequences: PCI DSS 6.5.1 names LDAP injection explicitly alongside SQL and XPath injection as a required assessment target.
Understanding the impact helps you prioritize defenses, but you also need to know exactly how attackers find and weaponize these flaws.
How Attackers Exploit LDAP Injection
Attackers follow a structured methodology to find and exploit LDAP injection vulnerabilities, progressing from reconnaissance through full credential extraction.
Step 1: Identify LDAP-Integrated Entry Points
The attacker identifies application features that likely query an LDAP backend. Per SANS LDAP blog, LDAP can be used for management, authentication, and querying objects from a directory database. Login forms, user search pages, password reset flows, corporate directory lookups, and VPN gateway portals are all candidate surfaces.
Step 2: Probe for Injection Points
The OWASP LDAP testing instructs testers to insert characters (, |, &, * to check for differential responses. Error messages, empty result sets, or changed application behavior confirm a vulnerable parameter.
Step 3: Infer Filter Structure
Without source code, attackers infer LDAP filter structure through fuzzing. SANS notes: "It is unlikely during a penetration test that you will have the source code to see these statements. In these situations, fuzzing and reconnaissance may have to be employed."
Step 4: Craft Injection Payloads
Common payloads include:
- Wildcard injection
(*)to retrieve all directory entries - Always-true filters
()(uid=))(|(uid=*)to bypass authentication - OR-based attribute injection ()(department=it)(|(cn=) to harvest credentials across multiple attributes
- Null object class termination
(*)(objectClass=*))(& (objectClass=void)to establish a reliable boolean oracle for blind extraction
The specific payload depends on the filter structure the attacker has inferred during reconnaissance.
Step 5: Escalate through attack chains
A typical attack chain documented across OWASP and MITRE ATT&CK sources follows this progression:
- Bypass login using an always-true filter
- Extract domain credentials via OR-based injection
- Create domain accounts via ldapmodify (ATT&CK T1136.002)
- Dump NTDS.dit for offline credential cracking (ATT&CK T1003.003)
Blind LDAP injection enables a parallel chain where attackers enumerate schema attributes using (attribute=*) probes, then extract values character by character, including password hashes, group memberships, and security identifiers.
These exploitation patterns affect a broad range of organizations and application types.
Who Is Affected by LDAP Injection?
Any organization relying on LDAP-backed authentication faces structural exposure to this vulnerability. OWASP notes injection vulnerabilities are "very prevalent particularly in legacy code."
Application types with highest exposure include:
- Web applications with LDAP-backed authentication (login portals, SSO systems)
- Legacy enterprise applications using string-concatenated LDAP queries
- Self-service password reset and employee directory portals
- VPN gateways and remote access portals
- Industrial control system management platforms
- Desktop applications (OWASP Desktop App Security Top 10 lists LDAP injection under DA1 Injections)
Industries with concentrated risk include:
- Healthcare: LDAP-backed EHR and clinical systems face HIPAA enforcement for unpatched vulnerabilities, with HHS documenting HHS breach data in large breaches between 2018 and 2022.
- Financial Services: Injection remains a relevant attack surface for identity-linked enterprise systems in this sector.
- Government and Critical Infrastructure: CISA has documented active exploitation in government environments and ICS energy sector platforms.
- Software and Technology: Open-source backends, database tools, and development platforms continue producing new LDAP injection CVEs.
LDAP injection affects a wide range of software, spanning enterprise COBOL environments, database administration tools, energy sector platforms, and open-source backends. These are not hypothetical risks; recent incidents confirm them.
Real-World Examples of LDAP Injection
The following cases illustrate how LDAP injection plays out across government networks, enterprise platforms, and open-source tools.
CISA Red Team: Enterprise with zero LDAP visibility (2024)
A CISA assessment found that the assessed enterprise "did not have monitoring for anomalous LDAP traffic." The team queried LDAPS to collect information about users, computers, groups, ACLs, OUs, and GPOs. CISA explicitly stated that a non-privileged user querying LDAP from a Linux domain host "should have alerted network defenders."
OpenText Enterprise Server: Complete Authentication Bypass (CVE-2023-4501)
This vulnerability allowed authentication to succeed with any valid username regardless of password, and could also succeed with an invalid username. It affected enterprise COBOL development and runtime environments deployed in financial services, insurance, and government mainframe integration.
Ivanti EPMM: Threat actors dump LDAP Credentials (2025)
Following publication of a proof of concept in May 2025, threat actors gained access to an Ivanti EPMM server and dumped LDAP credentials. CISA added the underlying vulnerabilities to the KEV catalog on May 19, 2025.
Redash: LDAP Injection enabling Password Spraying (CVE-2020-36144)
GitHub Security Lab documented that the email field in Redash LDAP authentication formatted an LDAP filter query string without escaping, enabling an unauthenticated attacker to brute-force all users' passwords with a single request.
These incidents span decades of LDAP security challenges.
LDAP Injection Timeline and History
LDAP injection has been a known vulnerability class for over two decades, with formal classification and continued CVE disclosures spanning from the late 1990s to the present.
- Protocol Origins. X.500 Directory Access Protocol (DAP) was developed by ITU-T. LDAP v1 appeared in RFC 1487, v2 in RFC 1777, and v3 in RFC 2251, which remains the version in enterprise use today.
- First Documented Issue. CVE-1999-0895 documented an early LDAP authentication security issue in Checkpoint FireWall-1 V4.0.
- Formal Classification. OWASP formally documented LDAP injection as a distinct attack class. The 2007 OWASP Top 10 mapped it under A2, Injection Flaws.
- Blind Injection Research. Alonso et al. presented systematic blind LDAP research at Black Hat Europe, demonstrating character-by-character data extraction.
- Peak OWASP Priority. OWASP Top 10 2017 ranked Injection as A1, the number one web application risk, explicitly naming LDAP injection.
- ICS Targeting. CVE-2018-14805 (ABB eSOMS) brought LDAP injection to the energy sector ICS space.
- Enterprise Platform Targeting. ForgeRock OpenAM, OpenLDAP, and OpenText Enterprise Server demonstrated continued enterprise impact.
- Recent Disclosure. New CVEs in recent years affect Apache Druid, WatchGuard Fireware, WeKan, Parse Server, Dell PowerMax, and pgAdmin.
New CVEs continue to appear, which makes ongoing monitoring a practical requirement.
How to Detect LDAP Injection
You need layered monitoring across application, directory, and network tiers.
Application-Layer Indicators
Monitor user input fields for LDAP metacharacters: *, (, ), \, and NUL bytes in authentication and search parameters. Watch for abnormally large LDAP result sets that suggest wildcard injection returning all directory entries. Authentication success immediately following a malformed query signals an authentication bypass pattern.
LDAP Server-Layer Indicators
Look for filter structures containing )( or |( sequences, which indicate filter group manipulation. Queries returning all entries via (objectClass=*) or (cn=*) suggest wildcard enumeration. Anonymous bind followed by broad search operations indicates unauthenticated reconnaissance attempts.
SIEM and Event Log Monitoring
For Active Directory environments, two Windows Event IDs are critical:
- Event ID 4662: Operations performed on AD objects. Monitor for Write Property, Control Access, DELETE, WRITE_DAC, and WRITE_OWNER actions.
- Event ID 1644: Expensive or inefficient LDAP queries, which injection attempts often produce.
Per NCC Group guide: "Look for unusual search filters in the logs. Attackers often use specific filters to enumerate users, groups, and computers."
Behavioral Correlation Patterns
Correlate across data sources to find injection campaigns:
- High LDAP query volume from a single source IP (injection tooling)
- Sequential attribute enumeration:
uid=a*, uid=b*(blind injection extraction) - Failed password followed by immediate login success (authentication bypass confirmation)
- Non-privileged Linux domain host performing bulk LDAP queries (the exact pattern CISA documented as undetected)
Correlating these signals across sources gives you a clearer picture of active injection campaigns than any single indicator alone.
WAF-Level Monitoring
OWASP ModSecurity Core Rule Set includes Rule ID 921200 in REQUEST-921-PROTOCOL-ATTACK.conf, which targets LDAP injection at severity CRITICAL and Paranoia Level 1 (enabled by default). The rule inspects request cookies, argument names, argument values, and XML bodies for LDAP filter metacharacter patterns.
Finding suspicious activity is insufficient without proper prevention controls.
How to Prevent LDAP Injection
Prevention requires a defense-in-depth approach spanning code, configuration, and infrastructure layers.
Code-Level Defenses
- Use parameterized LDAP queries. The most effective defense is passing user input as parameters rather than concatenating it into filter strings:
- Apply context-appropriate escaping. Use the correct escaping function for the correct LDAP context. For search filters (RFC 4515), escape *→
\2a, (→\28, )→\29, \→\5c, NUL→\00. For Distinguished Names (RFC 2253), escape\, #, +, <, >, ,, ;, ", =, and leading/trailing spaces.
Language-specific implementations include:
| Language | Search Filter Escaping | DN Escaping |
| Java | OWASP ESAPI encodeForLDAP() | OWASP ESAPI encodeForDN() |
| .NET | Encoder.LdapFilterEncode() | Encoder.LdapDistinguishedNameEncode() |
| Perl | Net::LDAP::Util::escape_filter_value() | Manual per RFC 2253 |
- Implement allowlist validation. Validate input against expected patterns before any LDAP operation. Reject inputs containing metacharacters not expected in the field. Normalize input (Unicode canonicalization) before validation per the OWASP cheat sheet.
Infrastructure Hardening
- Disable anonymous and unauthenticated bind. This single action eliminates the root cause behind multiple critical vulnerabilities.
- Use LDAPS (port 636). Disable plaintext LDAP (port 389) per NIST SP 1800-16.
- Apply least-privilege ACLs to LDAP binding service accounts. Restrict them to only the operations and directory subtrees required.
- Segment LDAP infrastructure from general network access per NIST SP 1800-18B.
These controls reduce the attack surface available to an attacker who reaches your LDAP infrastructure.
CI/CD Pipeline Integration
Integrate static analysis (SAST) and dynamic analysis (DAST) into your development pipeline. The OWASP Top 10 recommends including SAST, DAST, and IAST tools to identify injection flaws before production deployment. Semgrep's taint analysis mode can track untrusted input from sources through sinks without sanitization using custom rules targeting LDAP query construction.
These prevention measures work best when supported by the right tooling.
Tools for Detection and Prevention
Effective LDAP injection defense requires a combination of scanning, monitoring, and runtime protection tools.
- OWASP ZAP provides active scanning for LDAP injection through ZAP Alert 40015 (CWE-90, WASC-29). Install via the ZAP Marketplace's Alpha scan rules and configure technology targeting to include Protocol / LDAP for applications with LDAP integration.
- OWASP ModSecurity CRS delivers WAF-level protection through CRS Rule 921200, which runs at Paranoia Level 1 by default. The rule inspects cookies, arguments, and XML payloads for LDAP filter manipulation signatures. CRS regression test payloads from CRS Issue 276 provide a ready-made fuzzing wordlist for WAF validation.
- Semgrep supports static taint analysis through mode: taint rules that trace untrusted data from input sources to LDAP query sinks, flagging injection paths before code reaches production.
- SIEM platforms with custom identification rules can monitor Windows Event IDs 4662 and 1644, correlate anomalous LDAP query patterns, and alert on behavioral indicators like sequential attribute enumeration or bulk queries from non-privileged hosts.
These tools address individual layers of the problem. A platform approach ties them together.
Reduce Identity Risk Across Your Organization
Detect and respond to attacks in real-time with holistic solutions for Active Directory and Entra ID.
Get a DemoRelated Vulnerabilities
Several vulnerability classes share this pattern with LDAP injection:
- SQL Injection (CWE-89): The closest analog. Both exploit unsanitized input in query languages, and authentication bypass is achievable through similar techniques. Syntax and target systems differ significantly.
- OS Command Injection (CWE-78): Shares the same Software Fault Pattern (SFP24, "Tainted input to command") with CWE-90 per MITRE. Targets the host operating system rather than directory services.
- XPath Injection (CWE-643): The OWASP LDAP testing explicitly groups XPath injection alongside LDAP injection as analogous authentication bypass techniques targeting XML-based data stores.
- Improper Neutralization of Special Elements (CWE-77): The parent weakness of CWE-90 in MITRE's hierarchy. All injection types descend from this generalized failure to neutralize interpreter-significant characters.
- Improper Encoding or Escaping of Output (CWE-116): Documents the direct chain from escaping failure to injection. CVE-2021-41232 demonstrates the CWE-116 → CWE-90 chain where an escaping failure in a Go application directly enabled LDAP injection.
- Improper Input Validation (CWE-20): The root cause when applications fail to validate input format before constructing LDAP queries.
Reviewing these related weakness types helps you apply the same defensive principles across your codebase, not just in LDAP-specific code paths.
Related CVEs
| CVE ID | Description | Severity | Affected Product | Year |
| LDAP injection in SuiteCRM allows unauthenticated attackers to manipulate search filters, enabling authentication bypass or information disclosure | Critical (9.8) | SalesAgility SuiteCRM <7.15.1 / 8.0.0–8.9.2 | 2026 | |
| WeKan incorporates unsanitized usernames into LDAP search filters and DN values, allowing unauthenticated remote attackers to manipulate LDAP queries during authentication | Critical (9.8) | WeKan Project WeKan <8.19 | 2026 | |
| Parse Server interpolates user-supplied authData.id directly into LDAP Distinguished Names and group search filters, enabling privilege escalation | High (8.8) | Parse Platform parse-server <8.6.26 | 2026 | |
| LDAP injection in WatchGuard Fireware OS allows unauthenticated remote attackers to retrieve sensitive information from a connected LDAP server | High (7.0) | WatchGuard Technologies Fireware OS 12.0–12.11.6 / 12.5–12.5.15 | 2026 | |
| Kanboard substitutes unsanitized user input directly into LDAP search filters, allowing unauthenticated attackers to enumerate LDAP users and discover sensitive attributes | Medium (5.3) | Kanboard Kanboard ≤1.2.48 | 2026 | |
| Teedy's LDAP-enabled login form allows unauthenticated LDAP injection via the username field, permitting arbitrary account creation and password spraying | Critical (9.8) | Sismics Teedy 1.9–1.12 | 2025 | |
| LDAP injection in Apache HertzBeat allows an authenticated attacker to craft commands resulting in arbitrary script execution | High (8.8) | Apache Software Foundation Apache HertzBeat ≤1.7.2 | 2025 | |
| Injecting special LDAP characters into pgAdmin 4's username field causes the LDAP server and client to process excessive data, resulting in denial of service | High (7.5) | PostgreSQL Global Development Group pgAdmin 4 <9.10 | 2025 | |
| GLPI's LDAP authentication form can be used to perform LDAP injection by unauthenticated attackers, fixed in version 10.0.12 | High (8.1) | GLPI Project GLPI 0.70–<10.0.12 | 2024 | |
| Privileged users can inject LDAP filter strings into OX App Suite's optional LDAP contacts provider, accessing directory content outside the intended hierarchy | High (~8.0) | Open-Xchange OX App Suite <7.10.6 | 2024 | |
| NVIDIA DGX A100 BMC contains an LDAP user injection vulnerability exploitable by adjacent-network unauthenticated attackers, leading to information disclosure | Medium (~6.5) | NVIDIA DGX A100 BMC | 2024 | |
| Mastodon's LDAP login query is insecure, allowing authenticated attackers to leak arbitrary attributes from the LDAP directory | High (7.7) | Mastodon Mastodon 2.5.0–4.1.1 | 2023 | |
| A crafted username bypasses LDAP authentication in Apache Derby, potentially allowing disk exhaustion, malware execution, and unauthorized database access | Critical (9.8) | Apache Software Foundation Apache Derby ≤10.16.1.1 | 2022 | |
| SSSD's libsss_certmap fails to sanitize certificate data used in LDAP filters, allowing an authenticated attacker to inject LDAP query elements and gain unauthorized access | High (8.8) | Red Hat / SSSD Project SSSD | 2022 | |
| Apache ManifoldCF passes usernames and domain strings to LDAP search queries without validation in its ActiveDirectory authority connectors | Medium (5.3) | Apache Software Foundation Apache ManifoldCF 0–2.23 | 2022 | |
| Thunderdome Planning Poker does not escape usernames before LDAP queries when LDAP authentication is enabled, allowing unauthenticated LDAP injection | Critical (9.8) | Thunderdome Planning Poker <1.16.3 | 2021 | |
| IBM Open Liberty's ldapRegistry-3.0 feature contains an LDAP injection vulnerability | High (7.5) | IBM Open Liberty ldapRegistry-3.0 (v17.0.0.3–22.0.0.1) | 2021 | |
| ForgeRock OpenAM allows LDAP injection via the Webfinger protocol, enabling unauthenticated character-by-character retrieval of password hashes or session tokens | High (est.) | ForgeRock OpenAM <13.5.1 | 2021 |
Conclusion
LDAP injection gives attackers a way to turn untrusted input into control over the directory systems your environment depends on for authentication and access. For you, that means the risk is rarely limited to one query or one application.
If you build queries safely, escape values in the right context, restrict bind permissions, and watch LDAP activity closely, you reduce both exposure and the room attackers have to move.
FAQs
LDAP injection is an input-handling flaw in software that builds LDAP queries from untrusted data. An attacker can change how the directory interprets a query, turning a login check into an always-true condition, expanding a narrow lookup into full directory enumeration, or abusing add and modify operations inside the LDAP tree.
Yes. LDAP injection falls under OWASP's broader Injection category rather than standing alone as its own Top 10 entry. In practice, that means you should review LDAP-backed code with the same rigor you apply to SQL injection because both flaws come from untrusted input reaching an interpreter.
Yes. If your web-facing login form, search page, portal, or management interface passes user input to an LDAP backend, an attacker can start exploitation over the network.
In many cases, they do not need valid credentials to begin probing for filter manipulation.
The highest-risk applications are those that use LDAP for identity decisions: login portals and SSO systems, password reset and directory search tools, VPN gateways and remote access portals, and legacy enterprise apps that build LDAP queries by string concatenation.
Attackers usually begin with simple probes. They submit LDAP metacharacters such as (, |, &, and *, then watch for changed responses, errors, or unusual result counts.
Once they infer the filter structure, they move to wildcard, OR-based, or blind extraction payloads.
Early signs often include metacharacters in authentication or search fields, unusually broad LDAP result sets, )( or |( patterns in filters, a failed login immediately followed by success, and bulk LDAP queries from a non-privileged host.
It is severe because LDAP often controls authentication and authorization beyond a single app. A successful injection can expose directory data, bypass login controls, or feed lateral movement planning across the environment.
That reach makes the business impact broader than many application-only flaws.
Yes, especially as an opening step in a larger identity attack chain. An attacker can move from login bypass or directory enumeration to credential harvesting, account creation, NTDS.dit dumping, and persistent access using valid accounts.
The injection is often the entry point, not the final objective.
Tools help, but they do not solve the problem alone. Scanners and WAF rules can find obvious cases, while blind injection and weak LDAP logging remain harder to spot.
If you lack visibility into LDAP traffic and query behavior, you can miss the activity even when exploitation is already underway.
Industries with centralized identity dependence carry the highest concentration of risk. The article highlights healthcare, financial services, government, critical infrastructure, and software platforms.
What ties them together is reliance on LDAP-backed authentication for high-value users, systems, and administrative workflows.



