The Traffic Light Protocol (TLP) is a framework for sharing sensitive information in cybersecurity. This guide explores the different TLP colors, their meanings, and how they facilitate secure communication.
Learn about the importance of TLP in incident response and threat intelligence sharing. Understanding TLP is crucial for organizations to enhance collaboration while protecting sensitive information.

What is Traffic Light Protocol (TLP)?
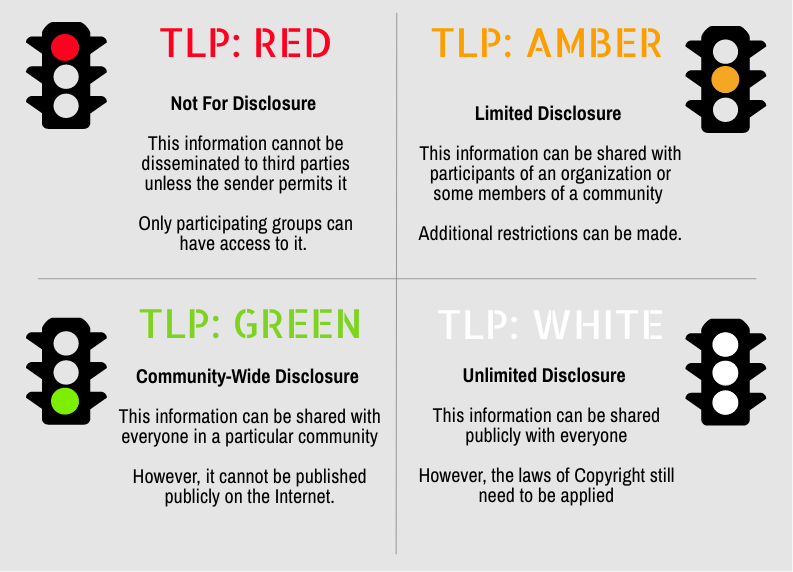
Traffic Light Protocol (TLP) is a standardized system for classifying and handling sensitive information. It is used by organizations to protect sensitive data and to ensure that information is only shared with those who need to know. TLP consists of four colors: red , amber , green , and white ⚪. Each color represents a different level of sensitivity and corresponding guidelines for how the information should be handled.
- Red is the most sensitive and should only be shared within the organization on a need-to-know basis.
- Amber is for information that should be shared within the organization and with trusted partners.
- Green is for information that can be shared more widely
- White ⚪ is for information that can be publicly shared.
The TLP system helps organizations to safeguard sensitive information and to ensure that it is handled responsibly.
How Does TLP Work to Improve Cybersecurity?
TLP helps to improve cybersecurity by providing a standardized system for classifying and handling sensitive information. By using TLP, organizations can ensure that sensitive data is only shared with those who need to know, reducing the risk of accidental or unauthorized disclosure. This is especially important in cybersecurity, as sensitive information such as security vulnerabilities or incident reports can be precious to cyber criminals. By using TLP, organizations can better protect this type of information and reduce the risk of it falling into the wrong hands. In addition, TLP can help organizations identify and respond to cyber threats more effectively, as it provides clear guidelines for handling and sharing information about potential threats. Using TLP, organizations can improve their cybersecurity posture and better protect themselves and their customers from cyber-attacks.
TLP provides several benefits to businesses and organizations. Some of the key benefits include:
- Improved information security: By using TLP, businesses and organizations can better protect sensitive information from being disclosed too widely or falling into the wrong hands. This can help to reduce the risk of data breaches and other security incidents, which can have serious consequences for the organization and its customers.
- Enhanced compliance: Many businesses and organizations are subject to various regulations and standards that require them to handle sensitive information in a particular way. By using TLP, organizations can ensure that they are compliant with these requirements and avoid costly fines and other penalties.
- Better collaboration: TLP can help organizations collaborate more effectively with other organizations, as it provides clear guidelines for handling and sharing sensitive information. This can be especially useful when multiple organizations work together on a project or respond to a crisis.
- Enhanced reputation: By using TLP, businesses and organizations can demonstrate to customers, partners, and other stakeholders that they are taking appropriate steps to protect sensitive information. This can help to enhance the organization’s reputation and build trust with its stakeholders.
TLP is a valuable tool for businesses and organizations that want to improve their information security and protect sensitive information from being mishandled or disclosed.
What are the Seven Layers Of Cybersecurity
The Seven Layers of Cybersecurity is a framework used to understand and analyze the various components of cybersecurity. It is based on the OSI (Open Systems Interconnection) model, a standardized framework for understanding how different networking protocols and technologies interact. The Seven Layers of Cybersecurity consists of the following layers:
- The physical layer refers to the physical infrastructure used to support cybersecurity, such as servers, firewalls, and other hardware.
- Network layer: This layer includes the network infrastructure, such as switches and routers, that connect devices and facilitate communication between them.
- Transport layer: This layer ensures that data is transmitted securely and reliably between devices.
- The session layer establishes, maintains, and terminates communication between devices.
- Presentation layer: This layer is responsible for formatting and encoding data in a way understandable by different devices and systems.
- Application layer: This layer provides the interface between the user and the underlying network infrastructure.
- Cybersecurity layer: This layer protects the other layers from cyber threats, such as malware, phishing attacks, and other cyber attacks.
By understanding and addressing each of these layers, organizations can build a comprehensive cybersecurity strategy that helps to protect against a wide range of cyber threats.
How Can You Implement TLP in Your Enterprises’ Cybersecurity Strategy?
To implement TLP in your own business or organization’s cybersecurity strategy, you can follow these steps:
- Determine which information is sensitive and requires protection: The first step in implementing TLP is identifying which information is sensitive and requires protection. This may include information about the organization’s operations, customers, employees, or proprietary technologies and potential security vulnerabilities or incidents.
- Classify the information using TLP colors: Once you have identified the sensitive information, you can classify it using the TLP colors. Red is the most sensitive and should only be shared within the organization on a need-to-know basis. Amber is for information that should be shared within the organization and with trusted partners. Green is for information that can be shared more widely, and white is for information that can be publicly shared.
- ️ Develop guidelines and procedures for handling the information: Once you have classified the sensitive data using TLP colors, you can develop policies and procedures for handling the report by the TLP guidelines. This may include establishing protocols for sharing the information with authorized individuals and methods for storing, accessing, and disposing of the data.
- Train employees and stakeholders: To ensure that TLP is implemented effectively, it is essential to train employees and stakeholders on handling sensitive information following the TLP guidelines. This may include providing training on the different TLP colors and the corresponding handling guidelines, as well as training on how to identify and report potential breaches of TLP guidelines.
Following these steps allows you to effectively implement TLP in your business or organization’s cybersecurity strategy and better protect sensitive information from mishandling or disclosure.
Unleash AI-Powered Cybersecurity
Elevate your security posture with real-time detection, machine-speed response, and total visibility of your entire digital environment.
Get a DemoConclusion
TLP is a system for classifying and handling sensitive information in cybersecurity. It consists of four colors representing different sensitivity levels, with guidelines for handling the information. TLP helps organizations protect sensitive information and reduce the risk of data breaches and other security incidents.
SentinelOne provides AI-powered prevention, detection, and response across endpoints, cloud workloads, and IoT devices to stop and prevent incident responses. When corrective action needs to occur, SentinelOne can kill, quarantine, remediate or roll back any potential effects from the threat.
And this all happens at an enterprise scale with precise, context-driven decisions autonomously, at machine speed — without human intervention.
Traffic Light Protocol FAQs
The Traffic Light Protocol is a simple classification scheme that labels shared information with four—RED, AMBER, GREEN, and CLEAR—to signal how widely recipients may circulate it. Originally created by the UK’s National Infrastructure Security Co-ordination Centre in the early 2000s, TLP helps organizations coordinate secure information exchange without rigid formal classification systems.
TLP guides recipients on handling and onward sharing of sensitive cybersecurity data. By marking threat intelligence or incident details with a TLP color, the information source sets clear boundaries. RED restricts it to named individuals, AMBER allows sharing within an organization (and its clients), GREEN extends to a wider community, and CLEAR permits public release. This prevents accidental over-sharing and preserves trust among partners.
TLP ensures that only the right audience sees sensitive threat data. When analysts, incident responders, and external partners share information marked with TLP, they avoid leaking operational details to unauthorized parties.
This controlled sharing builds confidence, speeds coordinated responses, and reduces the risk that threat indicators fall into attackers’ hands. Proper use of TLP safeguards privacy and reputation while enabling swift, targeted collaboration.
- TLP:RED – For named recipients only; no further disclosure beyond the specific exchange.
- TLP:AMBER – Limited to the recipient’s organization and its clients on a need-to-know basis; AMBER+STRICT confines it to the organization alone.
- TLP:GREEN – Shareable within the community or peer organizations but not publicly.
- TLP:CLEAR – Unrestricted public release; no sharing limits.
Use TLP:RED when details pose high risk if widely circulated—leaked vulnerability reports or active investigation data belong here. Only directly involved participants see RED information.
Choose TLP:AMBER when you need to involve your wider organization or trusted clients to act on data but still prevent public exposure. AMBER balances action needs against risk by restricting sharing to a broader internal audience.
Embed TLP marking in incident playbooks and reporting templates so every alert, advisory, or intelligence brief carries a color label. Train staff to assign the correct TLP before sharing and enforce handling rules in communications, document headers, and collaboration platforms.
Integrate TLP into security-orchestration tools and ticketing systems to flag sharing boundaries automatically. Regularly audit compliance and refresh training to keep everyone aligned on TLP practices.
By clearly indicating sharing limits, TLP removes guesswork about who may see or act on threat information. Responders and partners know at a glance what they can forward and to whom, reducing delays and preventing accidental over-sharing.
This clarity builds trust, fosters faster coordination across teams and organizations, and ensures sensitive details reach only those equipped to respond, accelerating containment and recovery efforts.



