The Good | Operation Synergia III Disrupts Malicious Networks & the EU Sanctions State-Sponsored Attackers
Operation Synergia III, an Interpol-led crackdown spanning July 2025 to January 2026, has disrupted global cybercrime infrastructure across the globe. Authorities across 72 countries sinkholed 45,000 malicious IP addresses and seized 212 devices and servers, resulting in 94 arrests and 110 ongoing investigations.
The operation focused on taking down servers used in connection to extensive phishing, ransomware, malware, and fraud networks. Regional actions highlighted the breadth of the cyber activity: Bangladesh police arrested 40 suspects tied to scams and identity theft, while law enforcement in Togo dismantled a fraud ring engaged in social engineering, including romance scams and sextortion.
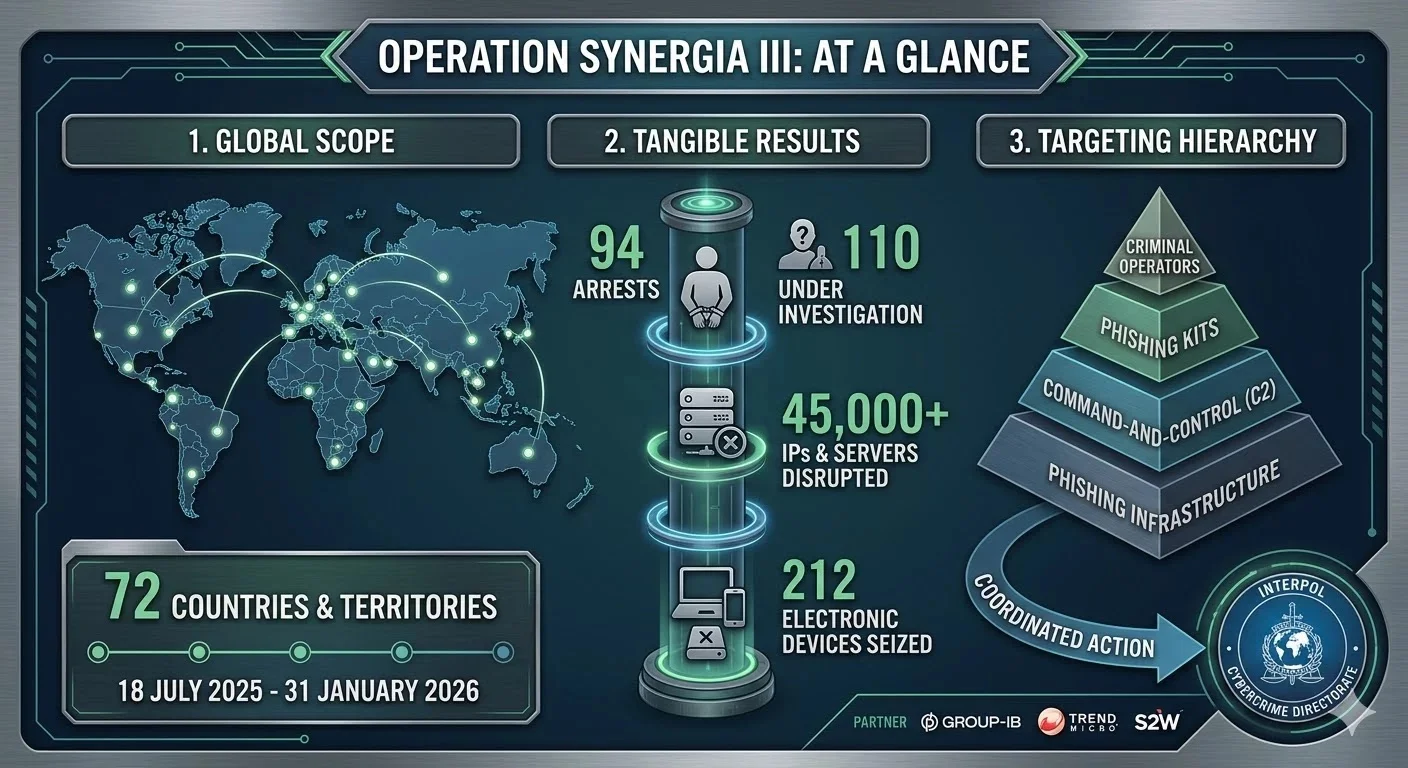
In Macau, investigators uncovered over 33,000 phishing sites impersonating casinos, banks, and government services all posed to steal financial data. Building on earlier phases of the operation and complementary operations like Red Card 2.0, Serengeti, and Africa Cyber Surge, these joint efforts point to the growing sophistication of cybercrime and the critical role that coordinated international actions plays in stemming its reach.
To further hinder threat actors, the Council of the European Union has sanctioned three companies and two individuals tied to major cyberattacks on critical infrastructure.
China-linked Integrity Technology Group supported operations that compromised over 65,000 devices across six EU countries, while Anxun Information Technology (aka i-SOON) provided hacker-for-hire services targeting governments. Two of its co-founders have also been sanctioned for their part in executing the cyberattacks.
Iran-based company Emennet Pasargad has also been sanctioned for multiple influence campaigns and breaches, including phishing and disinformation efforts.
The Bad | Researchers Uncover ‘DarkSword’ iOS Exploit Stealing Sensitive Personal Data
A new iOS exploit chain and payload dubbed ‘DarkSword’ is stealing sensitive personal information from iPhones running iOS 18.4 to 18.7. The toolkit is linked to multiple threat actors, including Russian-aligned UNC6353, who previously leveraged a similar exploit chain called Coruna. DarkSword was subsequently uncovered while various researchers analyzed Coruna’s infrastructure.
In early November 2025, NC6748 used DarkSword against Saudi Arabian users via a Snapchat-themed website. Subsequently, other attackers linked to PARS Defense, a Turkish commercial surveillance firm, started running the exploit kit on Apple devices. Early this year, cases involving DarkSword were spotted across Malaysia and, most recently, it has been leveraged to target Ukrainian users.
DarkSword exploits six documented vulnerabilities (CVE-2025-31277, CVE-2025-43529, CVE-2026-20700, CVE-2025-14174, CVE-2025-43510, CVE-2025-43520), which Apple has since patched. Threat actors have used them to deliver at least three malware families: GHOSTBLADE (a data miner collecting crypto, messages, photos, and locations), GHOSTKNIFE (a backdoor exfiltrating accounts and communications), and GHOSTSABER (a JavaScript backdoor enumerating devices and executing code).
The delivery chain begins via Safari exploits, gaining kernel access and executing a main orchestrator (pe_main.js) that injects modules into privileged iOS services, including App Access, Wi-Fi, Keychain, and iCloud. Collected data spans passwords, messages, contacts, call history, location, browser history, Apple Health, and cryptocurrency wallets. The malware removes traces after exfiltration, indicating a focus on rapid theft rather than persistent surveillance.
Experts note that both DarkSword and Coruna exhibit signs of large language model (LLM)-assisted code expansion, showing professional design with maintainability and modularity in mind. Users are advised to update to iOS 26.3.1 and enable Lockdown Mode if at high risk.
The Ugly | Interlock Ransomware Exploits Cisco FMC Zero-Day to Breach Enterprise Firewalls
The Interlock ransomware group has been actively exploiting a critical remote code execution (RCE) zero-day in Cisco’s Secure Firewall Management Center (FMC) software since late January 2026. The vulnerability, tracked as CVE-2026-20131 (CVSS: 10.0), allows unauthenticated attackers to execute arbitrary code with root privileges on unpatched devices due to a case of insecure deserialization of user-supplied Java byte stream. Cisco has since issued a patch, urging customers to update immediately.
Interlock ransomware group is now exploiting a Cisco firewall bug patched on March 4
The bug is a CVSSv3 10/10 RCE in the Cisco Secure Firewall Management Center (FMC) Software: sec.cloudapps.cisco.com/security/cen…
— Catalin Cimpanu (@campuscodi.risky.biz) 19 March 2026 at 10:42
Interlock, first seen in September 2024, has a history of high-profile attacks, including deploying the NodeSnake remote access trojan (RAT) against U.K. universities. The group has claimed responsibility for incidents affecting organizations such as DaVita, Kettering Health, the Texas Tech University System, and the city of Saint Paul, Minnesota. IBM X-Force researchers recently noted Interlock’s deployment of a new AI-assisted malware strain called Slopoly, highlighting the group’s evolving capabilities.
Latest reports explain that Interlock exploited the FMC flaw 36 days before its public disclosure, beginning on January 26, giving operators a head start to compromise firewalls before defenders were aware. This early access allowed attackers to operate undetected, underlining the danger of zero-day vulnerabilities.
Cisco has faced a series of zero-day exploits in 2026 so far. Earlier this year, maximum-severity flaws in Cisco AsyncOS email appliances, Unified Communications, and Catalyst SD-WAN were patched after being actively exploited, allowing attackers to bypass authentication, compromise controllers, and insert malicious peers.
The most recent incidents affecting FMC demonstrate both Interlock’s aggressive targeting of enterprise networks and the importance of rapid patching management and coordinated vulnerability disclosure. Organizations using Cisco FMC are strongly urged to apply the latest updates to mitigate ongoing risk.


