The Good | Law Enforcement Makes Swift Arrest After Attack on Airports
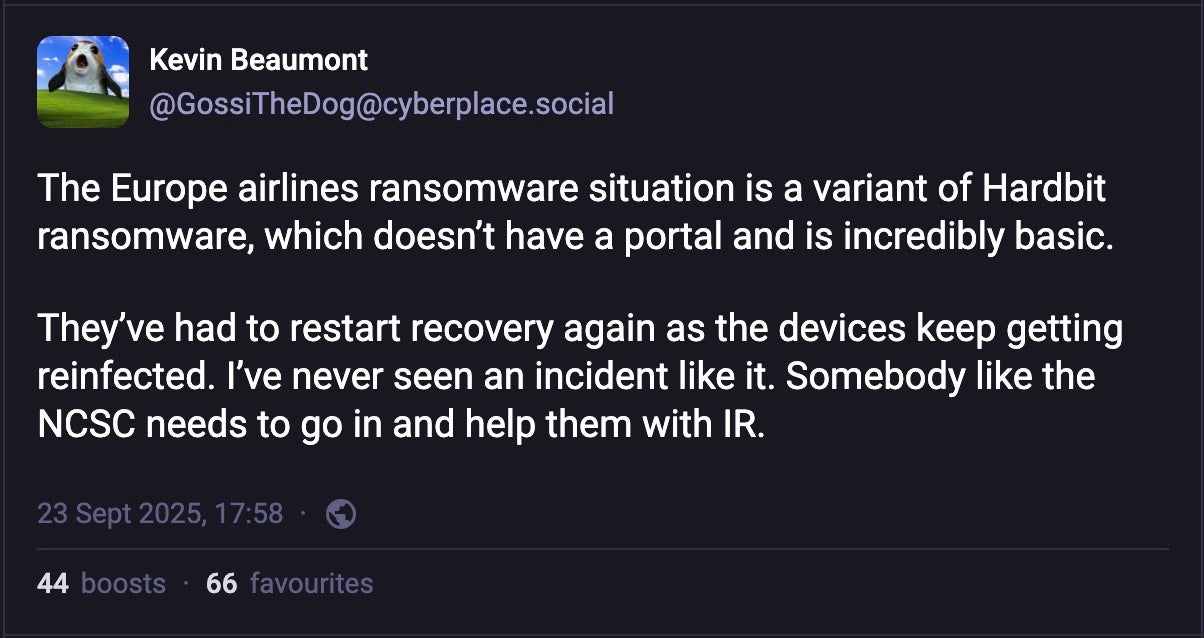
Authorities in the UK have been quick to arrest an individual in connection with the cyber attack on Collins Aerospace last Friday, which caused disruption at several European airports including Berlin, Brussels, Dublin, and Heathrow.
The attack on Collins’ MUSE (Multi User System Environment) software – responsible for processing activities like passenger check-in, boarding and bag drops – disrupted flight across the weekend, with carriers at Brussels airport being told to cancel some 140 of 276 scheduled flights for the following Monday.
Meanwhile, Heathrow is said to have had more than a thousand computers “corrupted”, indicating a likely ransomware attack.
In Berlin, airport authorities said that as of Wednesday morning check-in and boarding were still being handled manually and that passengers should expect delays and cancellations.
A spokesperson for Dublin airport said manual workarounds for check-in and bag drops were still in place as of Wednesday and there was as yet no timeline for when things would return to normal.
An unidentified male in his 40s was arrested in West Sussex, UK on Tuesday evening on suspicion of Computer Misuse Act offences. The UK’s National Crime Agency (NCA) says the investigation remains at an early stage and is ongoing. The man has been released on bail pending further enquiries.
The Bad | DPRK Threat Actor Groups Collaborate to Weaponize Developer Identities
Researchers at ESET have this week offered further evidence that distinct DPRK threat actor groups responsible for the Contagious Interview campaign and the DPRK Fraudulent IT Worker campaign are likely working in concert, using identities stolen from the former to feed the recruitment drive of the latter.
Detailing the activities of a threat actor they call DeceptiveDevelopment, broadly overlapping those of Contagious Interview, the researchers say they uncovered new links between the two campaigns. DeceptiveDevelopment operators use LinkedIn and other social media platforms to pose as recruiters, using fraudulent job offers to lure job seekers and compromise their computers.
Meanwhile, operators running IT worker scams use the information stolen by DeceptiveDevelopment operators to pose as job seekers with companies they wish to infiltrate. The researchers say the fake IT workers initially targeted jobs in the U.S. but have now shifted to European countries such as France, Poland, and Ukraine.
While DeceptiveDevelopment focuses on malware, OSINT shows ties to North Korean IT workers who use fake identities to secure remote jobs, thus surreptitiously funding North Korean state operations. 5/6
— ESET Research (@esetresearch.bsky.social) 25 September 2025 at 10:24
Through an analysis of OSINT data and other research, ESET says the fake IT workers are organized into teams with members working between 10-16 hours per day, pursuing job opportunities, completing tasks and undertaking studies in topics such as web programming, blockchain, AI and English language. The members also use prepared scripts to try and recruit proxies in target countries who would be willing to attend interviews or run laptop farms.
The scale of the DPRK’s activities to infect job seekers and their potential or current employers as well as to use stolen data to infiltrate companies as fraudulent workers has surprised security researchers. The threat presents a different challenge to simply detecting and preventing isolated campaigns and underscores the need for security teams and recruitment teams to develop workflows that can identify fraudulent applications. At the same time, enterprises are urged to ensure they lockdown their internal resources with a trusted security platform that can prevent both intrusions and insider threats.
The Ugly | China-Linked Threat Actor Drops Malware on Edge Devices That Sleeps for Over a Year
China-linked threat actors have been targeting U.S. firms in the tech and legal sectors with a stealthy backdoor known as BRICKSTORM, likely with the aim of infecting a broader range of downstream victims and feeding development of new zero days, Google’s Threat Intelligence Group (GTIG) has said this week.
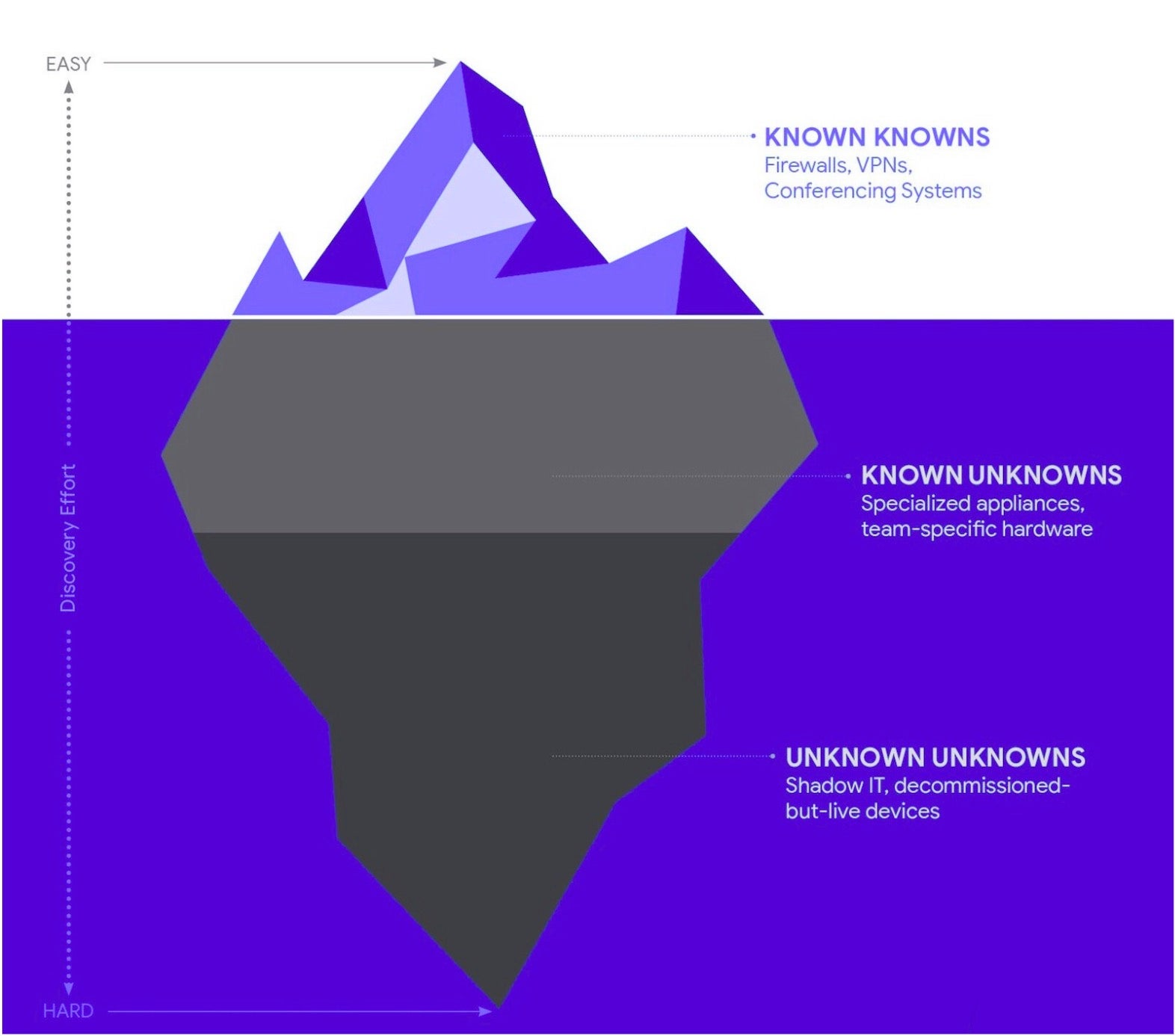
Attributing the activity to UNC5221, GTIG said the threat cluster was distinct from the widely-reported activities of Silk Typhoon, named as responsible for a number of attacks on U.S. interests earlier this year. UNC5221’s activities are specifically focused on obtaining and maintaining long-term access via backdoors on appliances and network edge devices that typically cannot support endpoint security software due to limited processor power, memory and storage space.
The researchers said initial access was difficult to determine due to the lengthy dwell time between infection and attack, on average 393 days, which often exceeded log retention periods. However, in one case, it was determined that the intrusion leveraged a security flaw in Ivanti Connect Secure devices to obtain initial access.
Having gained a foothold, UNC5221 deploy a Linux/BSD malware known as BRICKSTORM, a Go-based backdoor, to a network appliance before pivoting to VMware vCenter and ESXi hosts, using valid credentials captured from the network appliance.
GTIG said a common theme across incidents was the threat actor’s interest in emails of key individuals within the victim organization, in particular those of developers and system administrators. The attackers used Microsoft’s Entra ID Enterprise Applications with mail.read and full_access_as_app scopes to gain access to every mailbox.
Hunting for BRICKSTORM creates challenges for defenders as the malware typically resides on devices that lack EDR telemetry. Google has released a scanner tool to help search for known samples, along with comprehensive advice for threat hunting and hardening of devices.