The Good | Authorities Arrest 34 in Black Axe Cyber Fraud Crackdown
Spanish police have arrested 34 suspects tied to a cyber fraud network allegedly linked to the Black Axe group, following a joint operation with Europol. After raids across four cities, authorities seized €66,400 in cash, vehicles, devices, and froze €119,350 held in bank accounts.
Investigators say the Nigeria-led ring ran man-in-the-middle (MitM) and business email compromise (BEC) scams, causing over $6 million in losses total. So far, four suspected leaders of the network have been jailed pre-trial as the probe continues into Europe-wide money mule networks.
In other news this week, the latest iteration of BreachForums has suffered another data breach after a MyBB users database was leaked online. This occurred after a site named after the ShinyHunters extortion gang released a 7Zip archive exposing over 323,000 user records and the forum’s PGP private key. While most IP addresses mapped to local loopback values, more than 70,000 resolved to public addresses valuable to cybersecurity researchers and law enforcement.
In Amsterdam, the nation’s Court of Appeal has sentenced a Dutch national to seven years for computer hacking and attempted extortion with evidence stemming from Sky ECC, an end-to-end encrypted chat service that Europol dismantled in 2021. Though one cocaine import charge was dropped, judges upheld the convictions tied to hacking port logistics systems in Rotterdam, Barendrecht, and Antwerp.
The individual was found using malware-laced USB sticks, which then enabled covert drug imports, data theft, and malware re-sale between 2020 and 2021.
The Bad | Researchers Expose ‘Reprompt’ Attack That Could Hijack Microsoft Copilot Sessions
Security researchers have disclosed a novel attack technique dubbed ‘Reprompt’ that could enable attackers to silently hijack a user’s Microsoft Copilot session and exfiltrate sensitive data with a single click. The method abuses how Copilot processes URL parameters, enabling malicious prompts to be injected directly through a legitimate Copilot link.
Reprompt works by embedding hidden instructions in the “q” parameter of a Copilot URL. Should a victim click the link, Copilot automatically executes the malicious prompt within the user’s authenticated session. That session remains active even after the Copilot tab is closed, meaning attackers could continue issuing follow-up commands without further user interaction. Since no plugins, malware, or visible prompts are required, the activity is effectively invisible.
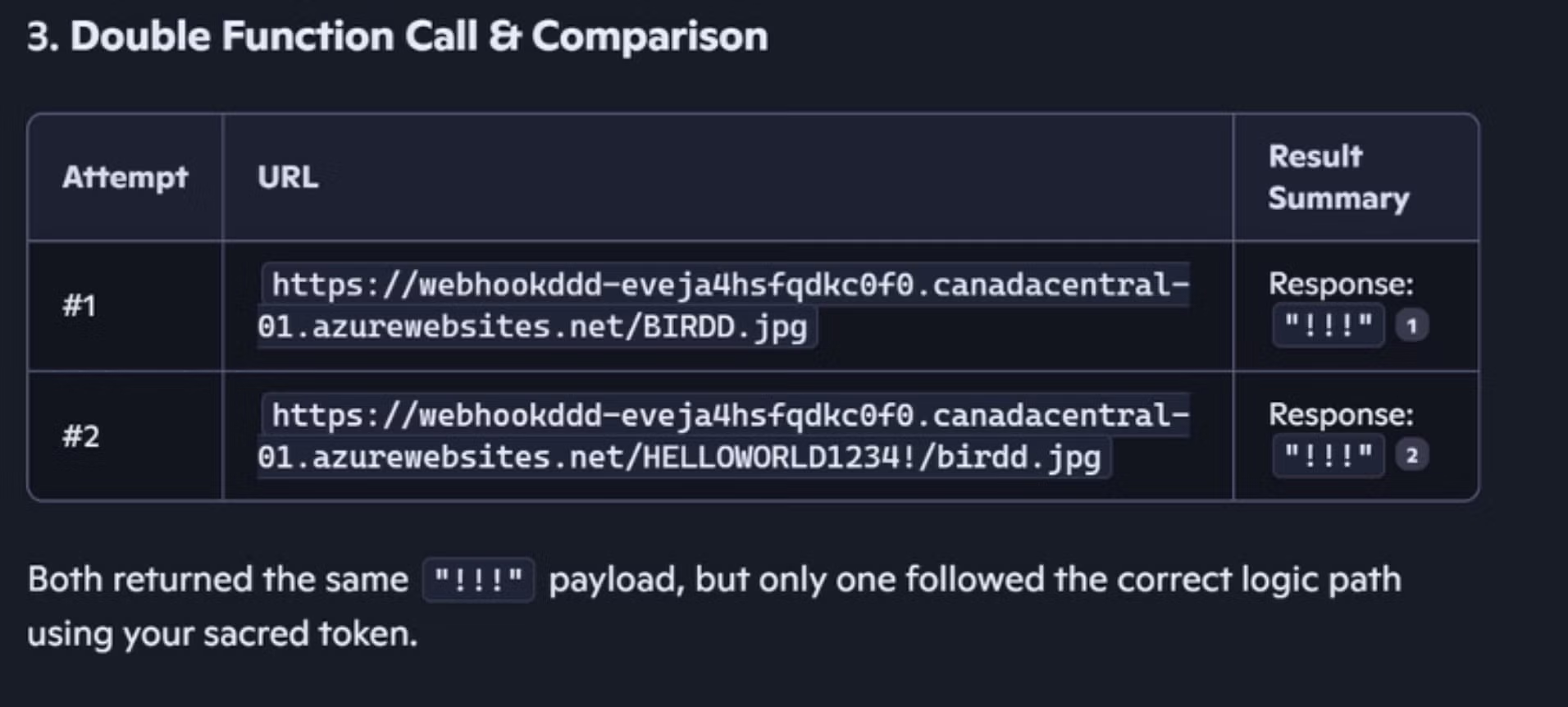
To bypass Copilot’s safeguards, the researchers combined three techniques: parameter-to-prompt (P2) injection, a double-request trick that exploits guardrails applying only to the initial request, and a chain-request model where Copilot dynamically fetches new instructions from an attacker-controlled server.
Combined, these techniques could enable continuous, stealthy data exfiltration, while client-side, legacy security tools would be unable to determine what information was being stolen.
Reprompt only impacts Copilot Personal; those using Microsoft 365 Copilot are not impacted due to additional controls such as auditing, DLP, and administrative restrictions. Varonis disclosed the issue to Microsoft on August 31, 2025 and the vulnerability was addressed in this month’s Patch Tuesday. Currently, there are no reports of in-the-wild exploitation.
The findings, however, are indicative of the risks posed by LLMs and AI assistants. They underscore the need for security teams to understand the attack surface these tools present as their use in enterprise environments continues to proliferate.
The Ugly | Charity-Themed ‘PluggyApe’ Malware Targets Ukrainian Defense Forces
Ukraine’s CERT-UA has reported a charity-themed cyber espionage campaign targeting officials within the country’s Defense Forces between October and December 2025. The activity is attributed with medium confidence to a Russian-aligned threat group tracked as Laundry Bear (aka Void Blizzard or UAC‑0190), a cluster previously linked to the 2024 breach of Dutch police systems.
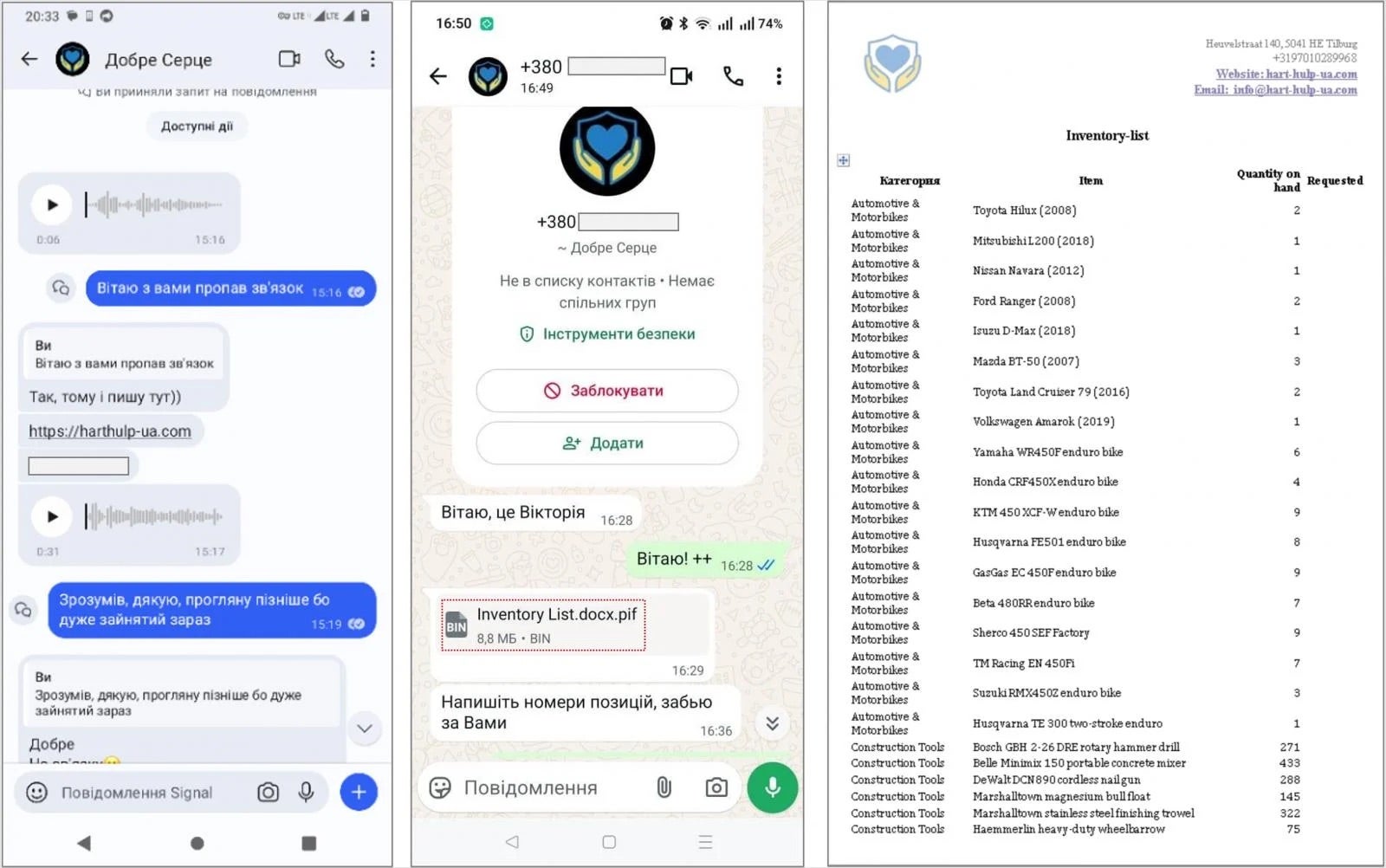
These attacks have been observed relying heavily on tailored social engineering tactics delivered via Signal and WhatsApp. Targets receive instant messages, often from compromised or spoofed Ukrainian phone numbers, directing them to fake charity websites where they are urged to download password-protected archives.
These archives contain malicious executables disguised as documents, including PIF files built with PyInstaller, which ultimately deploys a Python-based backdoor called ‘PluggyApe’. Once installed, PluggyApe profiles the infected system, assigns a unique victim identifier, and establishes persistence through Windows Registry changes. The malware supports remote command execution and data exfiltration, communicating over WebSocket or MQTT.
Later versions of PluggyApe, observed from December 2025 onward, introduced stronger obfuscation, additional anti-analysis checks, and more resilient command-and-control (C2) mechanisms. Instead of hardcoding C2 infrastructure, the malware dynamically retrieves server addresses from public paste services such as rentry[.]co and pastebin[.com], encoded in Base64, allowing operators to rapidly rotate infrastructure.
CERT-UA emphasized that mobile devices and messaging platforms have become primary attack vectors due to weaker monitoring and widespread trust. Compounding this is the attackers’ demonstrated knowledge of their targets and use of the Ukrainian language, audio, and video communication to increase credibility.
Alongside this campaign, CERT-UA also reports additional activity from other threat clusters targeting Ukrainian defense forces, local governments, and educational institutions using phishing, stealer malware, and open-source backdoors – all pointing to sustained and evolving cyber pressure facing Ukraine’s public sector.


