The Good | Authorities Crack Down on Ransomware, Crypto Fraud & DPRK Laundering Ops
Three ex-employees of cybersecurity firms DigitalMint and Sygnia have been indicted for participating in BlackCat (aka ALPHV) ransomware attacks on five U.S. companies between May and November 2023.
The defendants allegedly acted as BlackCat affiliates, breaching networks, stealing data, deploying encryption malware, and demanding cryptocurrency ransoms. Victims included medical, pharmaceutical, and engineering firms. Prosecutors say the ransom demands ranged from $300,000 to $10 million, with one company paying out $1.27 million. The trio faces up to 50 years each in prison if convicted.
Also this week, the U.S. Treasury sanctioned two North Korean financial institutions and eight individuals for laundering cryptocurrency stolen via fraudulent IT worker schemes. The designated include Ryujong Credit Bank and Korea Mangyongdae Computer Technology Company (KMCTC), along with executives and bankers responsible for managing funds linked to ransomware attacks and UN sanctions violations.
OFAC says that over the last 3 years DPRK-affiliated cybercriminals have stolen more than $3 billion in cryptocurrency using malware and social engineering. The sanctions freeze U.S. assets and warn that transactions with these entities risk secondary penalties.
In Europe, authorities have arrested nine suspects involved in a cryptocurrency fraud network responsible for stealing over €600 million ($689 million) across multiple countries. The criminals allegedly created fake crypto investment platforms that promised high returns and recruited victims through social media, cold calls, and fake endorsements from celebrity investors. Victims lost their funds while the suspects laundered the stolen assets using blockchain tools. In operations coordinated by Eurojust in Cyprus, Spain, and Germany, law enforcement seized cash, crypto, and bank accounts.
The Bad | SleepyDuck Trojan Exploits Ethereum Smart Contracts to Evade Takedown
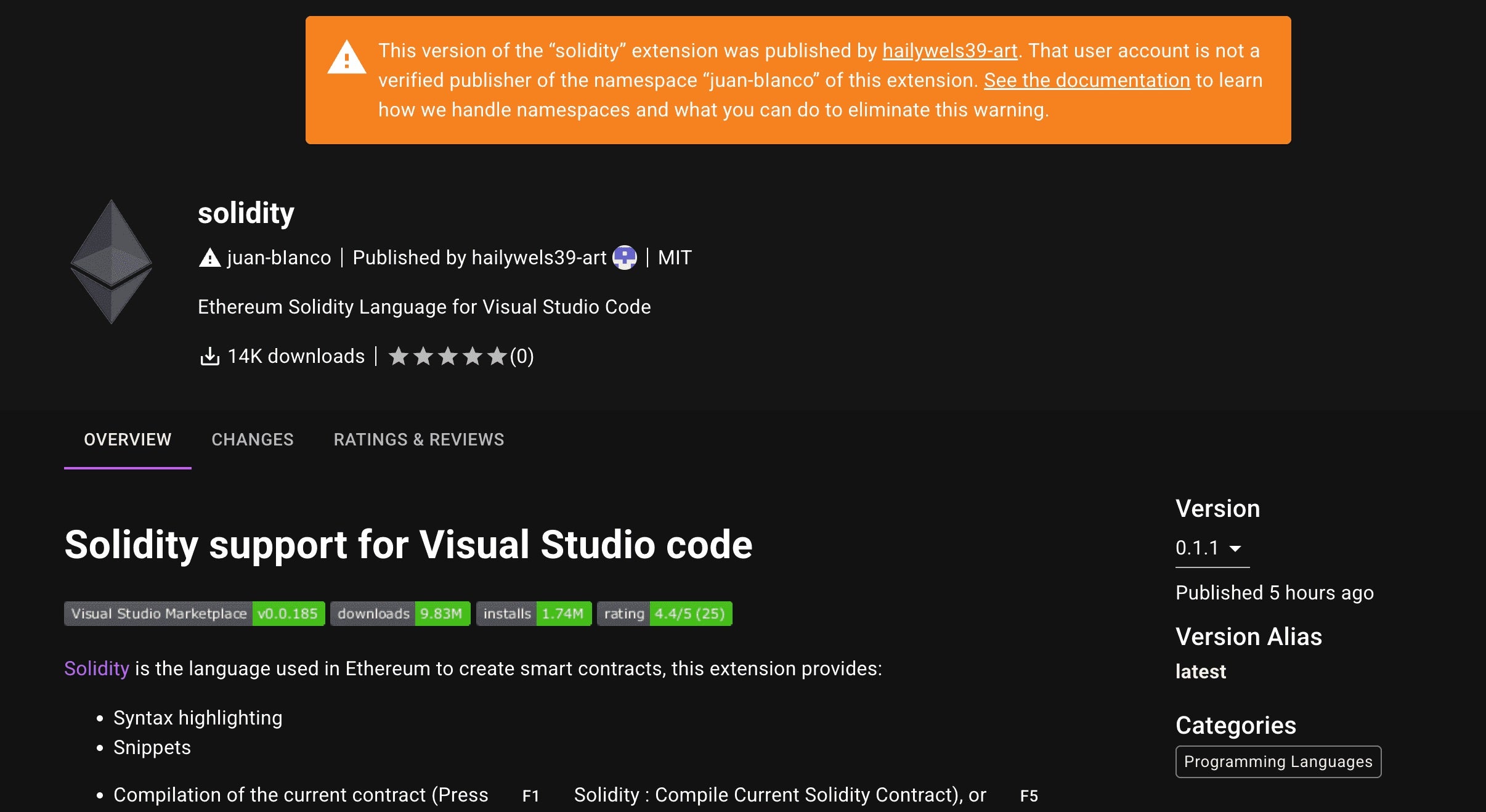
A new remote access trojan (RAT) dubbed ‘SleepyDuck’ has been masquerading as a well-used Solidity extension on the Open VSX open-source registry, researchers say. The malware uses Ethereum smart contracts to manage its command and control (C2) communications, helping it to maintain persistence even if its main server is taken down.
Initially benign when published on October 31, the infected extension, juan-bianco.solidity-vlang, became malicious after an update made the following day, by which time it had already been downloaded 14,000 times. For now, the extension remains available on Open VSX with a public warning. In total, it has been downloaded over 53,000 times.
Security researchers report that SleepyDuck activates when the code editor starts, a Solidity file opens, or when a compile command runs. It disguises its malicious activity through a fake webpack.init() function from extension.js, while secretly executing payloads that collect system information such as hostnames, usernames, MAC addresses, and timezones.
After it is triggered, the trojan queries the Ethereum blockchain to find the fastest RPC provider, read its C2 details, and enter a polling loop for new instructions. This blockchain-based C2 redundancy means that even if the main C2 domain (sleepyduck[.]xyz) is disabled, the malware can still fetch updated addresses or commands from the blockchain, making takedown efforts much more difficult.
In response, Open VSX has introduced new security measures, including shorter token lifetimes, automated scans, revoking any leaked credentials, and working in coordination with VS Code to block emerging threats. Best practices for developers include verifying extension publishers and installing software only from trusted repositories to avoid supply-chain compromises.
The Ugly | Iran-Based Actors Target U.S. Policy Experts in New Espionage Campaign
Between June and August, a newly identified threat cluster dubbed ‘UNK_SmudgedSerpent’ launched a series of targeted cyberattacks against U.S.-based academics and foreign policy experts focused on the Middle East. The campaign, coinciding with rising Iran-Israel tensions, uses politically-themed lures related to Iranian domestic affairs and the militarization of the Islamic Revolutionary Guard Corps (IRGC).
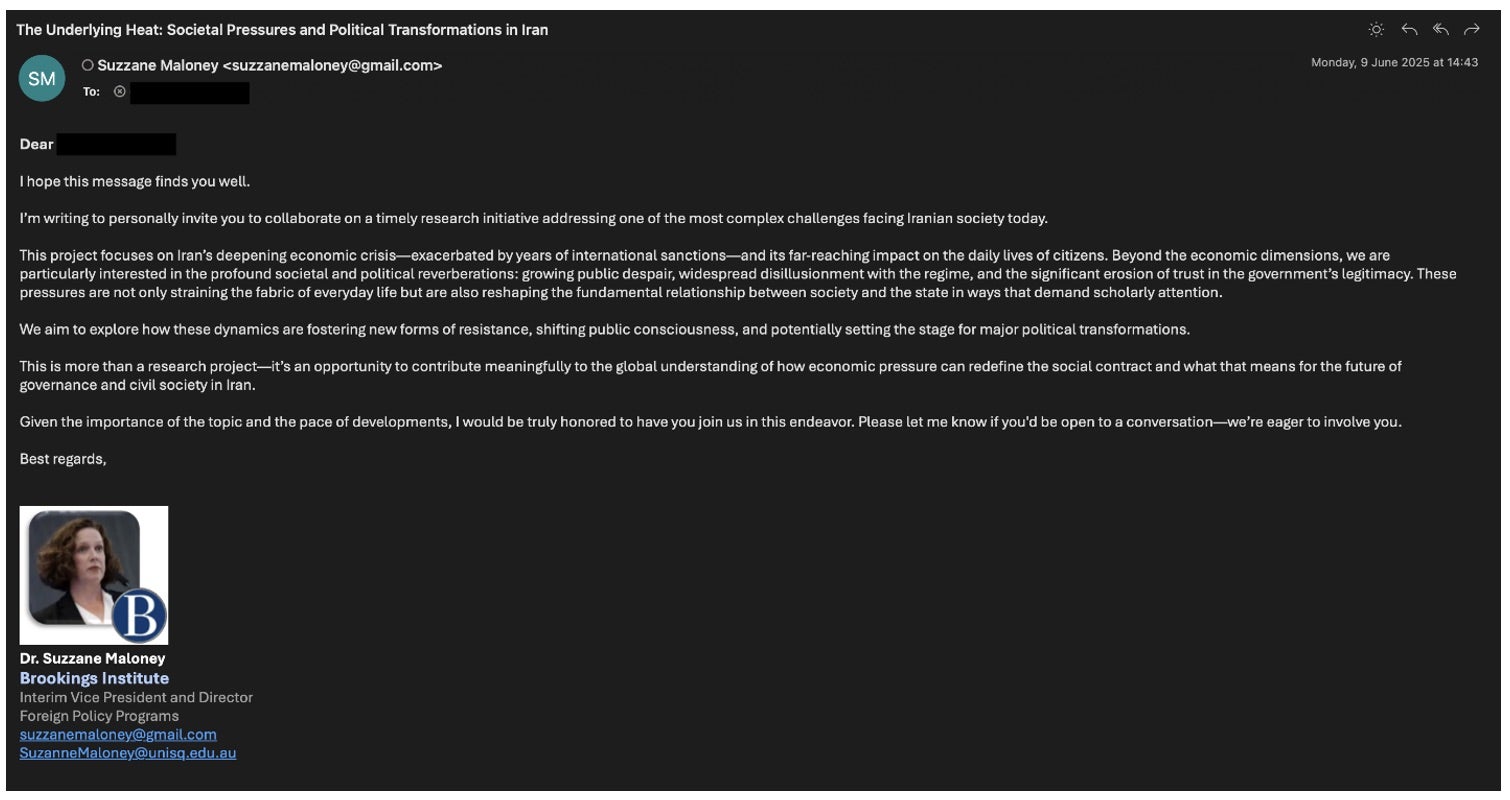
Researchers say the threat actors behind the campaign initiated attacks with benign email exchanges before introducing phishing links impersonating prominent U.S. foreign policy figures and think tank institutions like the Brookings Institution and Washington Institute.
The targeted victims, over 20 U.S.-based experts on Iran-related policy, were enticed to open malicious meeting documents and login pages designed to harvest their Microsoft account credentials. In some attacks, the attackers sent URLs leading to fake MS Teams login pages but pivoted to spoofed OnlyOffice sites if the victim grew suspicious.
Clicking the links led to the download of malicious MSI installers disguised as Microsoft Teams, which then deployed legitimate remote monitoring and management (RMM) software like PDQ Connect. Subsequent activity suggests attackers manually installed additional tools such as ISL Online, indicating possible hands-on-keyboard intrusion.
Researchers note that the operation’s tactics mirror those of known Iranian cyberespionage groups such as TA455 (aka UNC1549, Smoke Sandstorm), TA453 (aka TunnelVision, APT 35, UNC788), and TA450 (aka TEMP.Zagros).
The researchers believe UNK_SmudgedSerpent’s campaigns are part of a broader collection effort by Iranian intelligence aimed at gathering insights from Western experts on regional policy, academic analyses, and strategic technologies.