Extended Detection and Response (XDR) has emerged as a hot topic among security vendors and analysts in recent months. The promise of enhanced threat detection across a vast array of interconnected hardware and software solutions echoes the early days of SIEM, which expanded beyond simple log management capabilities. Like most legacy SIEM deployments, early XDR customers struggled to balance their investment in the tool with positive business outcomes. In fact, most enterprises haven’t yet fully considered the cost and complexity associated with the data collection and analysis required by some vendor XDR solutions. Let’s delve deeper into these challenges and see how SentinelOne is transforming the XDR landscape by addressing one of the largest and most complex obstacles to successful XDR adoption: managing large-scale data .
Exponentially increasing data
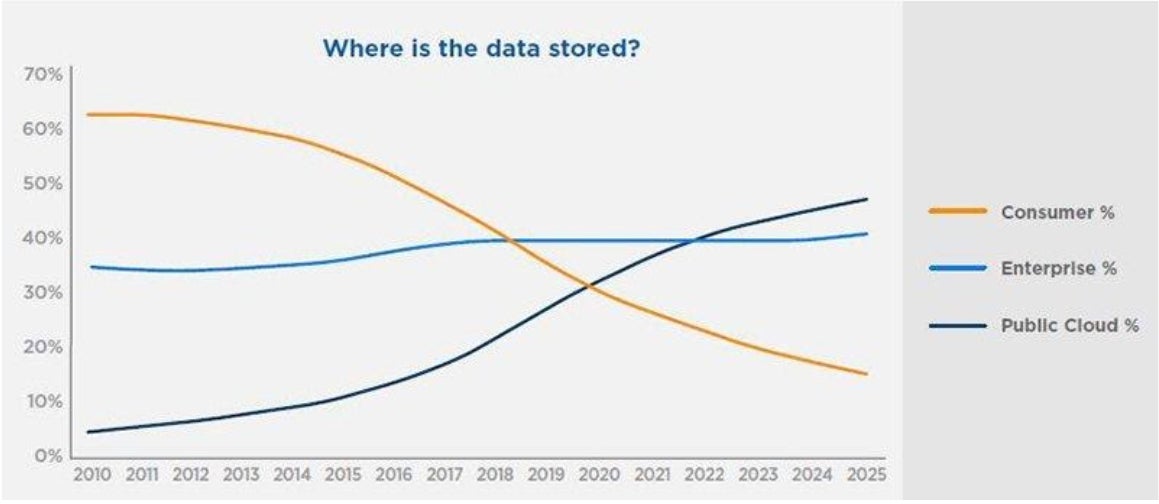
IDC predicts that by 2025, the total amount of data stored globally will reach 175 zettabytes (ZB), a staggering fivefold increase from the 33 ZB projected in 2018. For those who no longer calculate in gigabytes, a zettabyte is equal to one trillion gigabytes. If stored on DVD media, that’s enough disk space to travel 12 round trips to the moon. But how is this data broken down, and how much of it can be used to make smart security decisions to protect your business from targeted attacks? Let’s delve deeper into the data.
Of the projected 175 ZB of data, roughly 85% is stored in enterprise and/or public clouds. More importantly, IDC predicts that by 2025, 30% of this data will be classified as “real-time, sensorized” telemetry from endpoints and IoT devices. This presents both a significant challenge and an opportunity for enterprises seeking to leverage this wealth of data to improve their security posture.
R
Remember, data alone cannot guarantee usefulness, and increasing data volume doesn’t magically increase its usefulness. Data must be contextualized and analyzed to become information. Similarly, we know that information becomes knowledge only when meaningful connections are made between multiple points of information and contextual data is combined to transform it into actionable results. Therefore, data without context tends to be redundant, and the human brain quickly tends to eliminate such insignificant data.
The Need for Context for Effective Data Management
Most businesses today generate massive amounts of telemetry data across all their entities, including activity logs from users, devices, applications, and sensors. In this “age of observability,” we can be confident that no significant change can be made without corresponding records. These records typically take the form of logs or events—transactional messages that describe entities, actions, properties, and response conditions. Additional forms of telemetry can include simple metrics containing sampled or summarized measurements.
Information security has taught us that even the most innocuous and mundane data sets can be linked to some level of investigation or malicious detection. Often, we don’t realize what we’re missing until long after a successful security breach by a stealthy attacker . While most attacks can be stopped with effective endpoint detection and prevention platforms before they impact the enterprise , analyzing the trails left behind can be the only effective means of fully identifying the attacker’s tactics, techniques, and procedures (TTPs), as well as their motivations and scope.
Singularity ActiveEDR/XDR leverages the unique capabilities of SentinelOne’s patented Storyline technology to connect disparate security events into a single timeline, perform attack visualizations, and provide a complete picture, including threat actor details as well as MITRE ATT&CK technique attribution where available.
Faulty devices and shadow IT that create information blind spots
There’s much to learn from factors not found in enterprise sensor data. Attackers are opportunistic and target all exposed devices, not just those known to security operations teams. As the enterprise attack surface expands with IoT, cloud transformation, containerized workloads, and BYOD, the need to expand telemetry sources to minimize or eliminate inevitable blind spots also grows.
Most organizations strive to maintain an accurate inventory of their connected devices, but few have the ability to identify when rogue or orphaned devices appear on their network, posing a potential security risk.
By leveraging existing sensor grids and the data collected from them, enterprises can more quickly identify gaps in security coverage and protect a wider attack surface. Security operations can be alerted when event volumes from existing sensors change without appropriate policy modifications, ensuring that configuration changes, whether malicious or benign, haven’t disabled or reduced logging on devices.
Singularity Ranger provides enterprises with visibility across their entire device assets, enabling security operations teams to quickly identify unmanaged/risky devices, fingerprint their characteristics, and highlight those without protection. Ranger Deploy then performs remote agent installation and policy enforcement on supported systems, reducing the enterprise attack surface and improving the organization’s security posture.
Learn more
A critical challenge facing enterprises today isn’t just the sheer volume of sensor data. More importantly, the location of individual data silos and their accessibility across platforms. In cybersecurity use cases, these factors have for years been the purview of Security Information Event Management (SIEM) platforms, where logs and events are collected and stored from the most common telemetry sources: firewalls, intrusion detection platforms, legacy antivirus solutions, and critical server assets—a short list.
The advent of Endpoint Detection and Response (EDR) gives enterprises access to vast amounts of high-quality, high-value, real-time event data from protected endpoints. However, this data is typically stored in a completely separate data store from the SIEM. As more enterprise workloads migrate to PaaS/IaaS solutions , we’re seeing yet another disconnected data silo emerge from a new set of sensors.
Combining these disparate and highly unique endpoint, cloud, network, and security data sets in one location is often costly and difficult, if not impossible, to demonstrate realized value. As enterprise security architectures become more diverse, securing cross-vendor data analytics models as part of effective detection and protection measures is more crucial than ever.
The Singularity Marketplace allows you to easily integrate the growing list of partners in the SentinelOne security ecosystem into both your data collection pipeline and the response and remediation options of various enterprises.
The sheer volume of telemetry sources, combined with the unique characteristics of each data source (different formats, content, contexts, and cardinality), presents today’s enterprises with a daunting data challenge. Efficiently consuming, parsing, enriching, normalizing, storing, and analyzing these massive data sets is not a cost-effective proposition for most organizations. Consequently, most enterprises are burdened with the task of selectively selecting which data sources to process based on their perceived value in improving business processes or enhancing security effectiveness.
All data has different values from a security operations perspective. Sometimes, the most readily available data (e.g., Windows WMI logs) may be the least useful for threat detection and security incident triage. While the most voluminous logs within an enterprise, such as network flow data, email transaction logs, DNS request/response events, and authentication alerts, offer greater value, their low signal-to-noise ratio makes collecting and processing this data a tedious task without an efficient, high-performance, and scalable data management platform.
Data Retention: A Key Element for Effective Threat Hunting
Another challenge enterprise security teams must overcome is the cost implications of long-term retention and retrieval of collected telemetry. Consuming high-value, high-volume data, but forcing it to “roll over” after 30 days, creates a failed SecOps record-hunting use case.
In fact, most vendors tend to limit retention periods to 7 to 30 days! As demonstrated by the recent SolarWinds supply chain attack, the security community was already aware of malicious artifacts and adversarial TTPs months ago. This meant many organizations were unable to conduct record hunting across the relevant timeframe, as the logs were already aging on the platform or moved to offline archives, making it difficult to categorize the scope of the attack.
Customers of the SentinelOne Singularity platform can perform real-time threat hunting across a 365-day retention period, providing SOC analysts with full artifact and adversarial TTP visibility throughout the event collection period.
Automated hunting and alerting rules can be created using SentinelOne’s patented Storyline Active Response (STAR™) feature, which triggers real-time and historical EDR and third-party telemetry data stored in the Deep Visibility data repository. Content packs containing relevant IoCs (indicators of threat) are published for automatic detection of known threat actor campaigns. To further extend retention, SentinelOne will offer a feature called HindSight , which provides the facility to retain data for an extended period of time for unlimited retrospective threat hunting across the full scope and timeframe of collected data.
Main contents
The solution to the problem of managing large-scale data is a data management strategy that democratizes the data that enterprises create, collect, and analyze.
The general rule is:
- No application should hold your data hostage.
- Replicating data across multiple repositories is expensive and difficult to manage.
- Maintaining disparate data silos leads to missed threat detection and blind spots in security incident triage and scoping efforts.
- Companies should not feel compelled to reduce the volume of relevant sensor data they collect and store to rationalize the cost-to-value equation.
In the next post in this blog series on XDR, we’ll delve into some of the unique capabilities available through the SentinelOne Data Platform (formerly Scalyr Event Data Cloud). Learn more about how SentinelOne is transforming the XDR landscape through unparalleled sensor collection and processing capabilities, enhanced signal-to-noise ratio reduction, meaningful threat detection from multiple sources, and prescriptive and actionable response integration .
If you would like to learn more about how the SentinelOne Singularity Platform can protect your organization and business, please contact us anytime to request a free demo.
