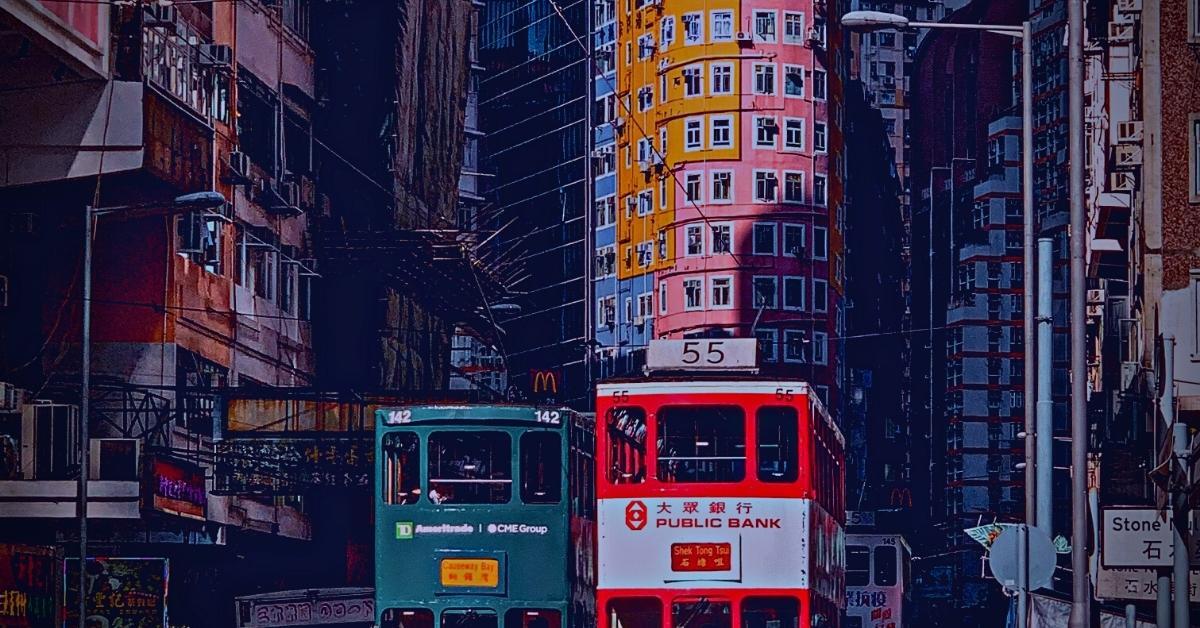
Infect If Needed | A Deeper Dive Into Targeted Backdoor macOS.Macma
SentinelLabs reveals further IoCs, behavior and analysis around suspected APT attack targeting macOS users and Hong Kong pro-democracy activists.
Read More
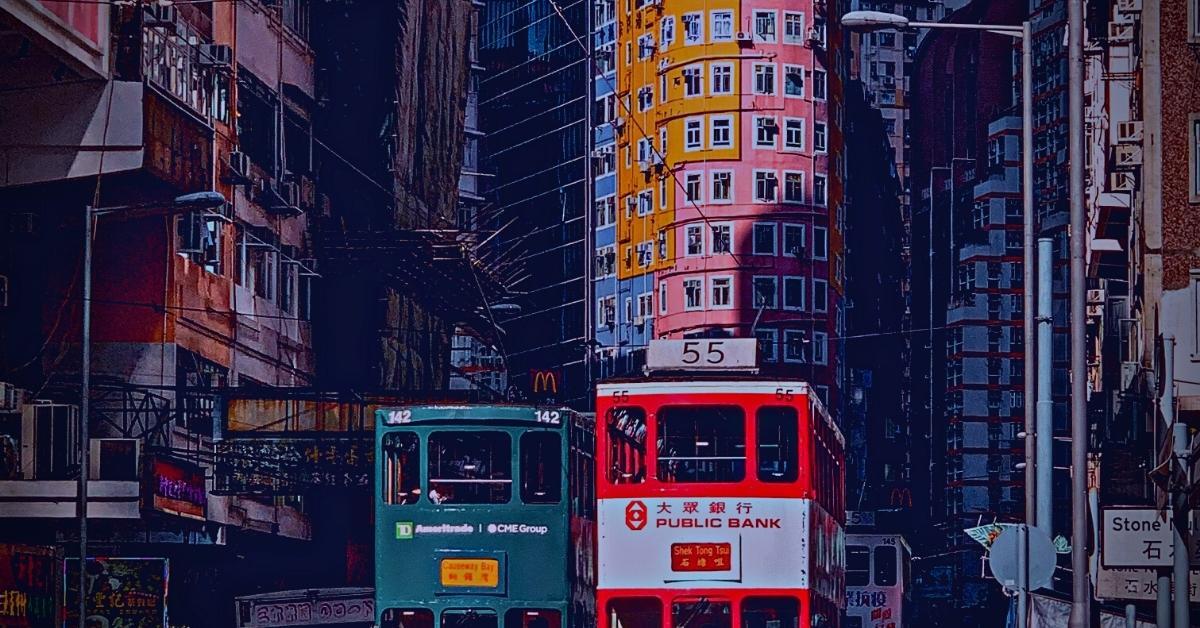
SentinelLabs reveals further IoCs, behavior and analysis around suspected APT attack targeting macOS users and Hong Kong pro-democracy activists.

SentinelLabs has discovered a heap overflow vulnerability in the TIPC module of the Linux Kernel, which can allow attackers to compromise an entire system.

New ransomware operator publishes victim details even if they pay. Our technical analysis shows how Spook is connected to other well-known malware families.

SentinelLabs sets off to dispel the myth that Go malware is hard to reverse engineer. This suite of IDApython scripts will set you well on your way

Exploring the links between Karma and other well-known malware families such as NEMTY and JSWorm, we find further IoCs and an evolving threat.

In Part 3 of our macOS reversing series, we look at three different macOS malware samples and walk you through how to decipher encrypted strings.

Agrius has continued to evolve its toolkit from wiper to ransomware operations, including a recent attack on a higher education facility.

Learn how to beat malware authors' control flow and avoid executing unwanted parts of their code to analyze macOS malware in radare2.

A high severity flaw in HP's OMEN Gaming Hub software allows any user to escalate privileges to kernel-level mode.

A new ZLoader campaign abuses Google Ads to target European banking institutions with signed MSI payloads and more than 300 domains.