
LABScon25 Replay | Please Connect to the Foreign Entity to Enhance Your User Experience
Joe FitzPatrick reveals how consumer imports of networked devices pose a real security risk to small businesses and critical infrastructure alike.
Read More

Joe FitzPatrick reveals how consumer imports of networked devices pose a real security risk to small businesses and critical infrastructure alike.

Marc Rogers and Silas Cutler expose how cheap smart home devices conceal a shadow supply chain of shell companies, firmware flaws, and foreign data routing.

Andrew MacPherson exposes how crypto thieves exploit DeFi architecture, from the $1.5 billion Bybit heist to drainers-as-a-service and fund laundering.
Dan Tentler reveals how consumer hardware coupled with Home Assistant can monitor hotel rooms, detect occupants through walls, and trigger automated alerts.

Jim Walter unpacks the hacktivist landscape and reveals how to distinguish different levels of threat based on persona characteristics.

Mei Danowski & Eugenio Benincasa unpack how Chinese firms running attack-defense exercises fuel state-linked offensive cyber operations.
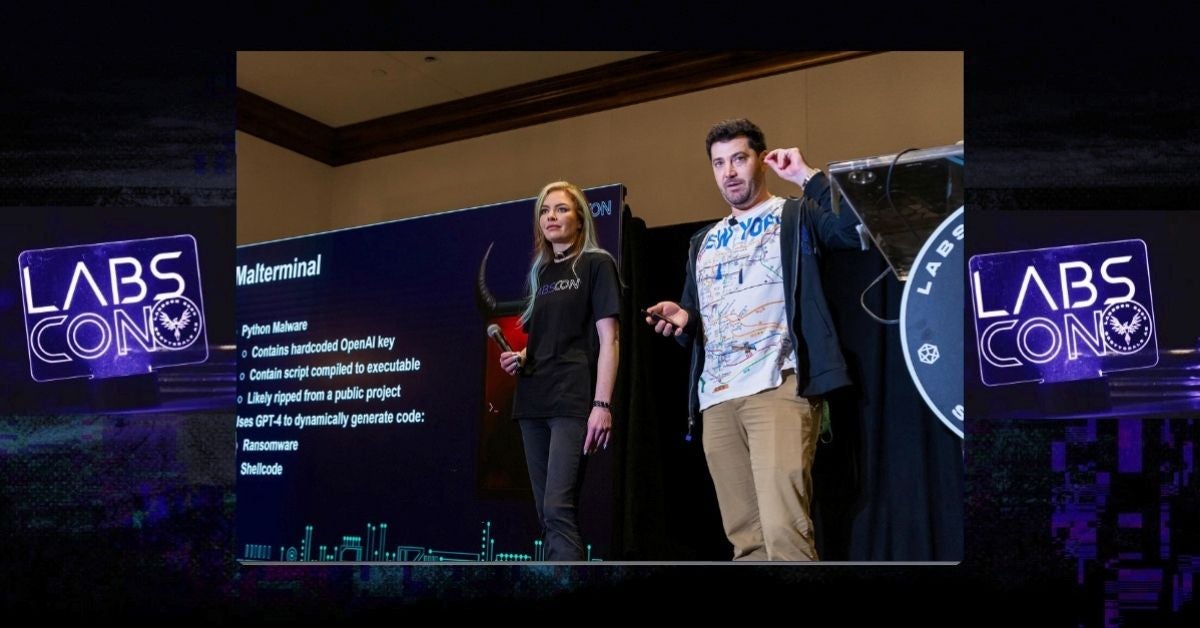
Learn how to detect malware that generates code at runtime. SentinelLABS reveals hunting techniques and how to uncover novel AI-enabled threats.

AI agents promise speed, but at what cost to trust? Dreadnode’s Wendiggensen & Palm unpack this dilemma through a hands-on study of leaked Russian data.

Dakota Cary and Eugenio Benincasa explore China's CTF ecosystem, highlighting competitions held by the Ministry of State Security and the PLA.
Jim Walter reveals how a recent leak provided insight into how Kryptina RaaS has been adapted for use in enterprise attacks.