Executive Summary
- Alert (AA20-302A) talks about Ransomware Activity Targeting the Healthcare and Public Health Sector stating “As part of the new Anchor toolset, Trickbot developers created Anchor_DNS, a tool for sending and receiving data from victim machines using Domain Name System (DNS) tunneling”.
- The team behind Trickbot has been aggressively updating and deploying various modules including Anchor and Bazar Loader. These evolutionary changes to Trickbot are furthering their reach into high-value targets, including healthcare entities.
- Development continues on TrickBots Anchor project, with the addition of using ICMP for command and control communication.
Background
TrickBot is the successor of Dyre[1,2] which at first was primarily focused on banking fraud in the same manner that Dyre utilized injection systems. TrickBot has shifted focus to enterprise environments over the years to incorporate everything from network profiling, mass data collection and lateral traversal exploits. This focus shift is prevalent in their inclusion of malware and techniques in their tertiary deliveries that target enterprise environments. Much like a company whose target will shift depending on what generates the best revenue.
Previous Anchor reporting:
- Anchor[3,4] projects connection of CyberCrime and APT
- Anchor includes DNS variant and POS variant using DNS[4,6]
- PowerTrick[5] custom powershell framework for high profile victims
- Anchor project, linux version[7]
Research Insight
While tracking Anchor we came across a sample with a few additions.
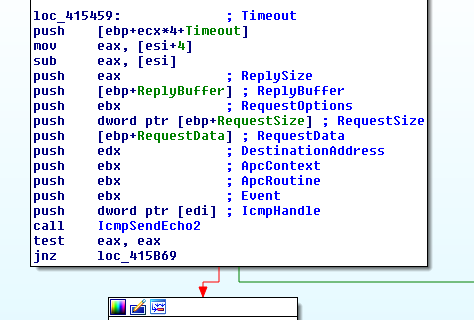
hIcmpFile error:
IcmpCreateFile
IcmpCloseHandle
IcmpSendEcho2
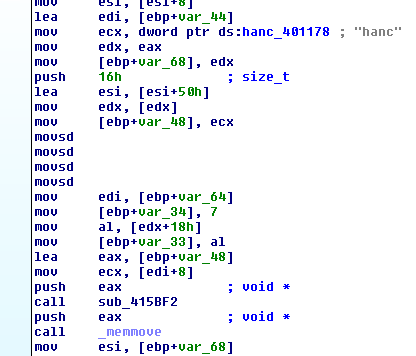
Pivoting on these additions shows an earlier sample was uploaded to VirusTotal with debugging symbols.
C:simsimanchorDNS.v5Binx64ReleaseanchorDNS_x64.pdb
Ultimately the ICMP portion appears to be ran in sequence along with the DNS traffic, while the DNS traffic will be initiated by performing DNS queries which will be routed to the malicious nameservers[6]. There’s plenty of good reports out there on Anchor DNS already including recently discovered linux version[3,4,6,7].
For the ICMP counterpart the traffic will be sent to the resolved IP of the domain name in question, this gives actors multiple avenues to maintain their infections while utilizing their other tools for pivoting around the environment[9].
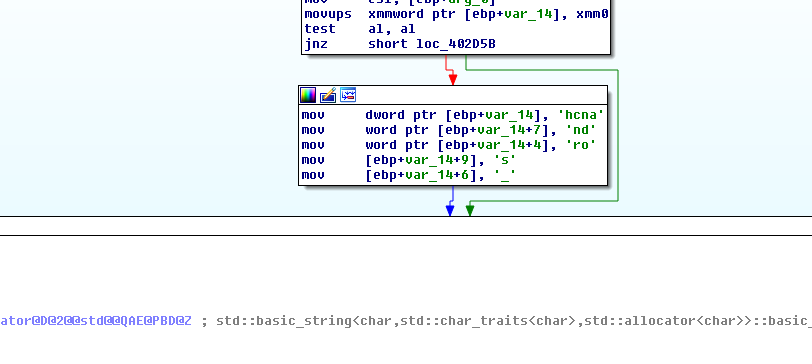
All of the samples so far recovered use a hardcoded string for the traffic constructed.
Below we can see the traffic from a sandbox detonation showing this[8].
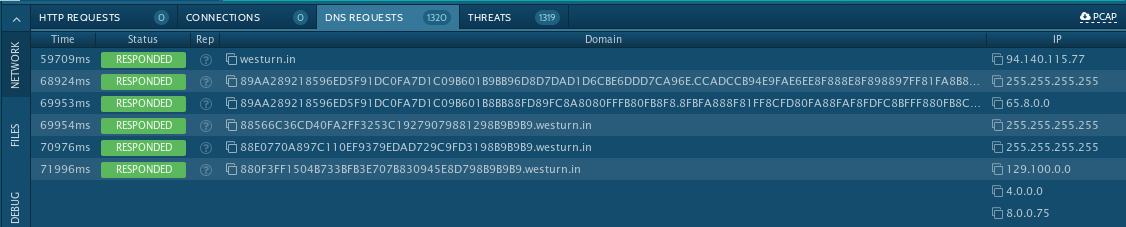
Above you can the DNS query for the C2 domain before it begins to perform DNS questions for exfiltration, what you can’t see in the sandbox run screen is the ICMP traffic. To see that you need to actually pull down the PCAP.
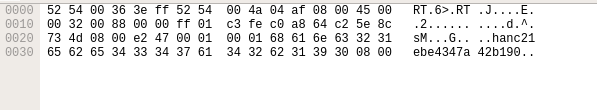
The ping contains 22 bytes of data of ‘hanc21ebe4347a42b190x08x00’.
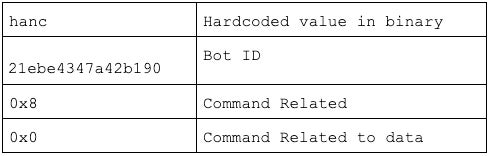
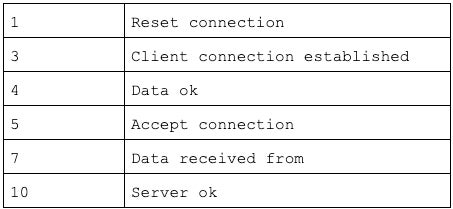
The bot then checks the response data of the 20th byte, which is listed as Command Related, using a switch statement.
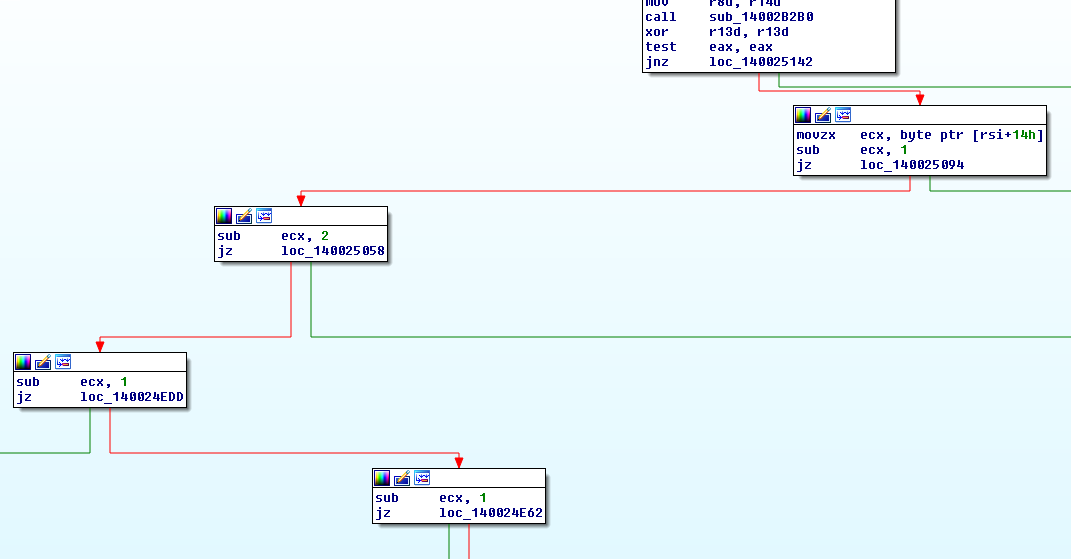
Thanks to the sample with the debugging messages we can quickly map out some of the response byte possible meanings.
Conclusion
Trickbot has proven to be highly resilient and very nimble. They continue to evolve their platform and infrastructure. The addition of ICMP as a potential C2 channel only strengthens the module, and improves the ability for Trickbot to stay both persistent and stealth. Even recent attempts to disrupt Trickbot have proven only slightly effective, and for a limited time at that. It cannot be stressed enough that the actors behind these campaigns are very well resourced, very well staffed, and they will focus on targets with dangerous abandon. Defense against these threats requires similarly nimble controls, ala a layered defense that can evolve with the adversary.
Indicators of Compromise
546bf4fc684c5d1e17b204a28c795a414124335b6ef7cbadf52ae8fbadcb2a4a
911077400d172dc1ad24f615e0061b06e2c3f9f9116c64365393e3e2a7637a92
westurn[.]in
Network signature on the hardcoded 4 byte string in the ICMP data[10].
References
1:https://blog.malwarebytes.com/threat-analysis/2016/10/trick-bot-dyrezas-successor/
2:https://www.fidelissecurity.com/threatgeek/archive/trickbot-we-missed-you-dyre/
6:https://hello.global.ntt/zh-cn/insights/blog/trickbot-variant-communicating-over-dns
7:https://medium.com/stage-2-security/anchor-dns-malware-family-goes-cross-platform-d807ba13ca30
8:https://app.any.run/tasks/433d0ef1-1a0d-4dbb-9837-553125c0db42/
9:https://www.sentinelone.com/labs/inside-a-trickbot-cobaltstrike-attack-server/




