
LABScon25 Replay | Hacktivism and War: A Clarifying Discussion
Jim Walter unpacks the hacktivist landscape and reveals how to distinguish different levels of threat based on persona characteristics.
Read More

Jim Walter unpacks the hacktivist landscape and reveals how to distinguish different levels of threat based on persona characteristics.

Learn how attackers exploit tokenization, embeddings and LLM attention mechanisms to bypass LLM security filters and hijack model behavior.

LLMs make competent ransomware crews faster and novices more dangerous. The risk is not superintelligent malware, but rather industrialized extortion.

Read how two Cisco Network Academy Cup winners went from students to operators behind Salt Typhoon, a global cyber espionage campaign targeting telecoms.

Mei Danowski & Eugenio Benincasa unpack how Chinese firms running attack-defense exercises fuel state-linked offensive cyber operations.

Accelerate adversary tracking and reveal hidden infrastructure with our open-source Synapse Rapid Power-Up for Validin.
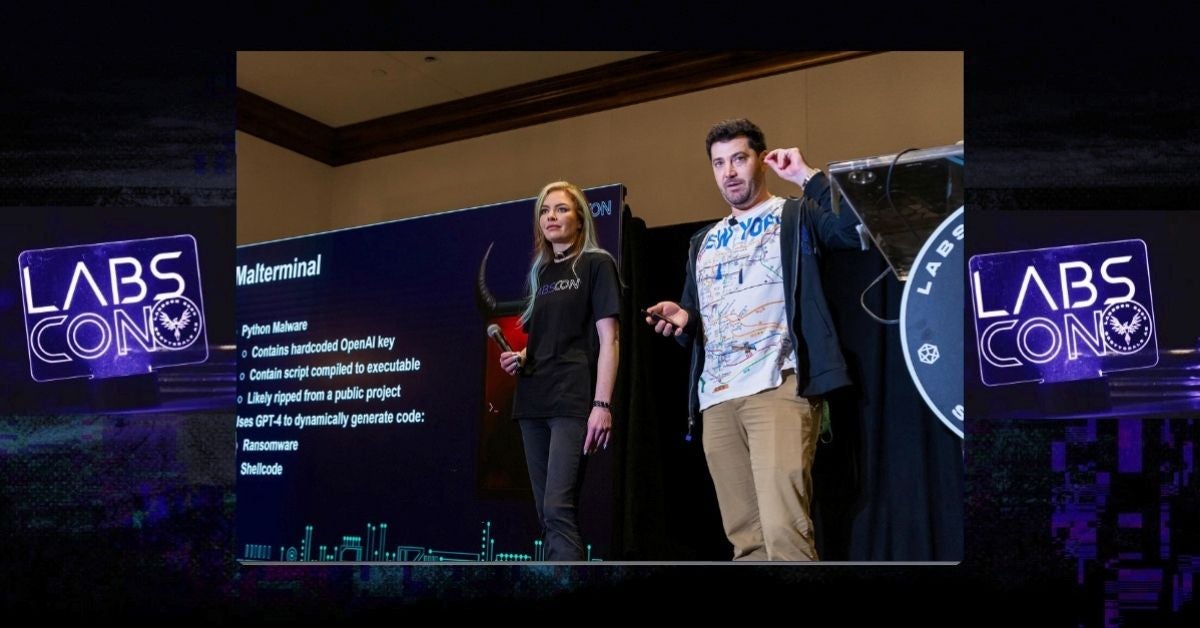
Learn how to detect malware that generates code at runtime. SentinelLABS reveals hunting techniques and how to uncover novel AI-enabled threats.

SentinelLABS uncovers a coordinated spearphishing campaign targeting organizations critical to Ukraine's war relief efforts.

AI agents promise speed, but at what cost to trust? Dreadnode’s Wendiggensen & Palm unpack this dilemma through a hands-on study of leaked Russian data.

LLM-enabled malware poses new challenges for detection. SentinelLABS presents groundbreaking research on how to hunt for this new class of threats.