By Aleksandar Milenkoski and Tom Hegel
Executive Summary
- Over the first quarter of 2023, SentinelLABS observed a campaign targeting users of Portuguese financial institutions conducted by a Brazilian threat group.
- The campaign is the latest iteration of a broader activity nexus dating back to 2021, now targeting the users of over 30 financial institutions.
- The attackers can steal credentials and exfiltrate users’ data and personal information, which can be leveraged for malicious activities beyond financial gain.
- The threat group simultaneously deploys two backdoor variants to maximize attack potency.
- To ensure uninterrupted operations, the threat actor has shifted its infrastructure hosting from IaaS providers implementing stricter anti-abuse measures, such as a major US-based cloud provider, to Timeweb, a Russian IaaS provider known for its more relaxed policies.
Overview
SentinelLABS has been tracking a campaign over the first quarter of 2023 targeting users of Portuguese financial institutions, including government, government-backed, and private institutions. Based on similarities in TTPs as well as overlaps in malware implementation and functionalities reported in previous work, we assess with high confidence that the campaign has been conducted by a Brazilian threat group. This conclusion is further supported by the presence of Brazilian-Portuguese language usage within the infrastructure configurations and malware implementations. We refer to the campaign conducted by this threat group as Operation Magalenha.
The threat actor deploys two backdoor variants on each infected machine, which we collectively dubbed PeepingTitle. Based on overlaps in code and functionalities, we assess that the PeepingTitle backdoors are part of the broader Brazilian financial malware ecosystem – specifically, of the Maxtrilha family (named by the then-used encryption key) first observed in 2021. We therefore assess that Operation Magalenha is the latest iteration of a long-standing activity nexus.
Operation Magalenha is characterized by changes in infrastructure design, and malware implementation and deployment. The threat actor behind the operation deploys two PeepingTitle variants simultaneously on infected machines, aiming to maximize the potency of their attacks. Further, to ensure uninterrupted operations, the threat actor has strategically transitioned its infrastructure hosting to Timeweb Cloud, a Russian IaaS provider known for its lenient anti-abuse policies, diverging from primarily relying on providers implementing stricter measures, such as DigitalOcean and Dropbox.
The PeepingTitle backdoors are implemented in the Delphi programming language and feature spyware capabilities giving the attackers full control over infected machines, allowing activities such as monitoring window interaction, taking unauthorized screenshots, terminating processes and deploying further malware.
Many of the TTPs we observed relate to those discussed in previous research attributing them to Brazilian threat actors that target users not only in Portugal but also in Spain as well as Central and Latin American countries. These TTPs include the use of Delphi-implemented backdoors, URL shorteners and public file hosting services for hosting malware, and archive files and VB scripts as part of the infection vectors.
Leveraging its malware arsenal, the threat group behind Operation Magalenha can steal credentials, exfiltrate users’ data and personal information, and achieve full control over infected machines. This opens up further possibilities for the targeting of individuals or organizations, or for the exploitation of that information and data by other cybercriminal or espionage groups.
Infection Vector
Brazilian threat actors are known to distribute malware using a variety of methods, such as phishing emails, social engineering, and malicious websites delivering fake installers of popular applications.
In the context of Operation Magalenha, the infection starts with the execution of a malicious VB script, which primarily serves to download and execute a malware loader and distract users while doing so. The malware loader subsequently downloads and executes the PeepingTitle backdoors.
The VB scripts are obfuscated such that the malicious code is scattered among large quantities of code comments, which is typically pasted content of publicly available code repositories. This is a simple, yet effective technique for evading static detection mechanisms – the scripts that are available on VirusTotal feature relatively low detection ratios.
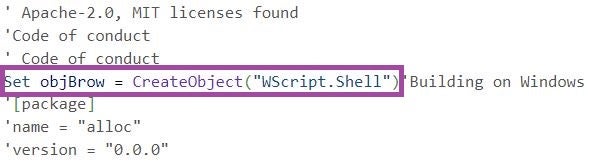
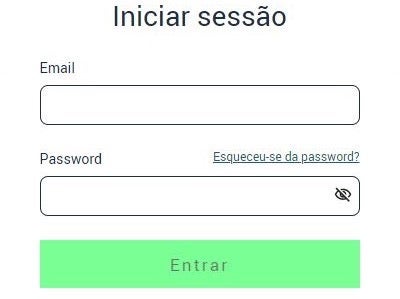
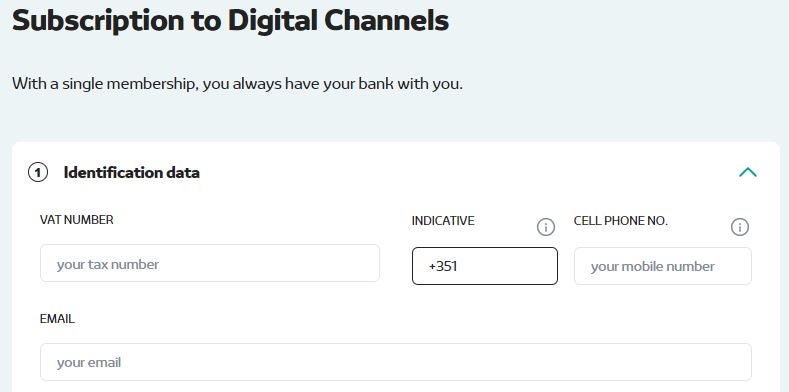
When executed, the VB scripts first open a TinyURL to user login sites of Energias de Portugal (EDP) and the Portuguese Tax and Customs Authority (AT – Autoridade Tributária e Aduaneira). Based on this script behavior, we suspect that the threat group behind Operation Magalenha has been delivering the scripts through EDP- and AT-themed phishing emails, aligning with a known tactic observed among threat actors targeting Portuguese citizens.
The VB scripts serve a twofold purpose for the threat actors:
- Act as a smoke screen distracting users while the scripts continue to download and execute the malware loader.
- Enable the theft of EDP and AT credentials if the users enter the credentials after the malware loader has executed the PeepingTitle backdoors. This may provide the threat actor with users’ personal information. We note that users may login to the Portuguese Tax and Customs Authority in several ways, including using government-issued credentials for citizens to access not only the online services of the Authority, but also other services provided by the Portuguese state.

The scripts then download to the %PUBLIC% folder an archive file that contains a malware loader. They subsequently extract the loader and delete the archive. Finally, the scripts execute the malware loader after a time interval of, for example, 5 seconds. The malware loader downloads and executes two PeepingTitle backdoor variants.
PeepingTitle
The PeepingTitle sample pairs we analyzed are Delphi executables and have compilation timestamps in April 2023. The samples share some code segments indicating that they have been developed as part of a single development effort. For example, both malware strains implement similar initialization routines, which involve evaluating the presence of the wine_get_version function in the ntdll.dll library file and establishing persistence by editing the HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run registry key.
Similar to other malware used by Brazilian threat actors, the PeepingTitle backdoors contain string artifacts in Brazilian-Portuguese language.
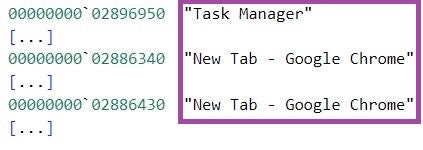
After initialization, at one second intervals the first PeepingTitle variant monitors the titles of application windows that have captured the mouse cursor. The malware first transforms a window title into a lowercase string stripped of any whitespace characters. It then checks if the transformed title contains any of the strings from a predefined set of strings related to targeted institutions. The figure below depicts PeepingTitle monitoring window titles, when a user interacts with a new Google Chrome tab and the Task Manager application, and comparing them against predefined strings.
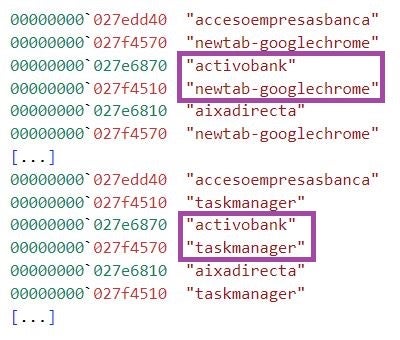
The predefined strings are defined such that they are part of the browser window titles when a user visits the online resources (i.e., sites or specific online services) of predominantly Portuguese financial institutions or institutions with a presence in Portugal. These include government, government-backed, and private institutions.
The targeted sites and online services encompass a broad set of activities that users may conduct when interacting with them providing a wealth of personal user information to the threat actor, such as account registration, document overview, and credential input.
The table below lists some of the targeted institutions and services.
| PeepingTitle string | Targeted institution or service |
| activobank | ActivoBank |
| aixadirecta | Caixadirecta (an online service of Caixa Geral de Depósitos, an institution owned by the Portuguese government) |
| articulares | Online banking sites for private users of various institutions |
| bancanet | Citibanamex (online banking site) |
| bancobest | Banco Best |
| bancoctt | Banco CTT |
| bancomer | BBVA |
| bankia | Bankia (currently merged with CaixaBank) |
| bankinter | Bankinter |
| bpi | Banco BPI |
| caempresas | Crédito Agrícola (services for corporate users) |
| caixaagricola | Various Mutual Agricultural Credit Banks |
| caixabank | CaixaBank |
| caixadirectaonline | Caixadirecta (a service of Caixa Geral de Depósitos) |
| canaisdigitais | Novobanco (online services) |
| caonline | Crédito Agrícola (online services) |
| citibanamex | Citibanamex |
| digitalbanking | Online banking services of various institutions |
| empresas | Online banking services for corporate users of various institutions |
| eurobic | EuroBic |
| homebank | Online banking pages of various institutions, such as Banco CTT and Cetelem |
| ingaccesoclientes | ING (login page for online banking) |
| internetbanking | Online banking sites of various institutions, such as the Portuguese Treasury and Public Debt Management Agency |
| itoagricola | Crédito Agrícola |
| loginmillenniumbcp | Millennium BCP (Portuguese Commercial Bank) |
| logintoonlinebanking | Online banking services of various institutions |
| montepio | Banco Montepio |
| netbancoempresas | Santander (online banking for corporate users) |
| netbancoparticulares | Santander (online banking for private users) |
| novobanco | Novobanco |
| openbank | Openbank |
| santander | Santander |
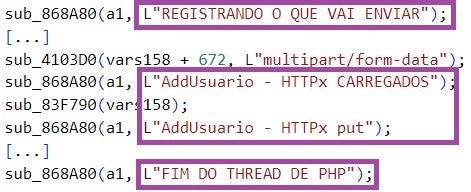
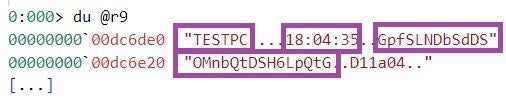
When a user visits a targeted online resource, PeepingTitle sets the window title monitoring interval to 5 seconds, connects to a C2 server, and exfiltrates data in an encrypted form. The data includes a timestamp, the name of the infected machine, and the captured window title, also in an encrypted form. This registers the infected machine at the C2 server.
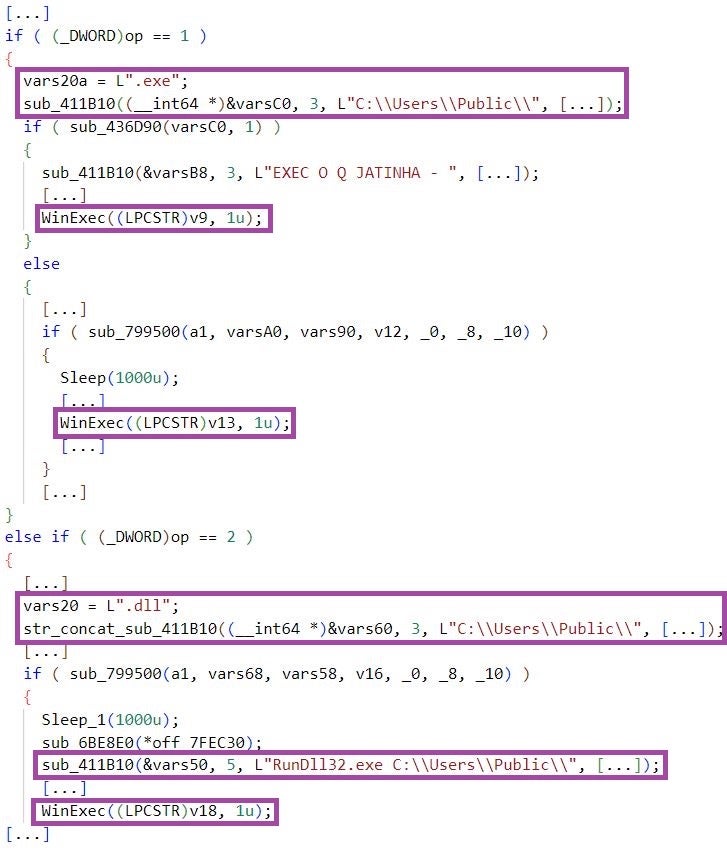
PeepingTitle implements backdoor capabilities that allow for full control over the compromised machines, some of which are:
- Process termination and screenshot capture: PeepingTitle can take screenshots of the entire screen.
- Staging of further malware: This involves executing malware placed in the
%PUBLIC%directory, or first downloading malware executables from attacker-controlled locations to this directory, and subsequent execution. The staged malware could implement any capabilities the threat actor may need in a given situation, such as further data exfiltration, or interaction and overlay screen capabilities to bypass multi-factor authentication. PeepingTitle supports the execution of Windows PE images and DLL files using therundll32Windows utility. - Reconfiguration: This includes restarting the PeepingTitle process, reconfiguring the window title monitoring interval to 1 second, and configuring the image scale of the screenshots that PeepingTitle takes.
In contrast to the first variant, the second PeepingTitle variant registers the infected machine at the C2 server upon execution: The malware exfiltrates data in an encrypted form, which includes the name of the infected machine and volume serial numbers. The malware then continues to monitor for changes of the top-level window and takes a screenshot of this window whenever the user changes it.
PeepingTitle sends the screenshot to a different C2 server than the one used for registering the infected machine. The figure below depicts PeepingTitle monitoring for changes of the top-level window, when this window is first of the Task Manager application and then twice of a new Google Chrome tab – the backdoor will take a screenshot of the Google Chrome window only once.
With the first PeepingTitle variant capturing the entire screen, and the second capturing each window a user interacts with, this malware duo provides the threat actor with a detailed insight into user activity. The second PeepingTitle variant implements further features, such as downloading and executing malware in the form of Windows PE images, process termination, and malware reconfiguration.
Infrastructure Analysis
Analysis of all infrastructure associated with the threat group behind Operation Magalenha revealed noteworthy changes in design for the operation. First, it is useful to understand the threat actors’ infrastructure design prior to the latest 2023 activity.
Early to mid 2022 associated activity centered primarily around abusing DigitalOcean Spaces, the S3 compatible cloud storage service, for hosting the malware used at the time – acting as download locations for target malware delivery. Specifically, bucket name and example URL originally used include:
| Bucket Name | Example URL |
| Audaction | https[://]audaction.fra1.digitaloceanspaces[.]com/pass/alma32.cdr |
| Azuredatabrickstrainne | https[://]azuredatabrickstrainne.sfo3.digitaloceanspaces[.]com/Workspace.zip |
| Believeonline | https[://]believeonline.ams3.digitaloceanspaces[.]com/acoustic/p0.cdr |
| Cleannertools | https[://]cleannertools.fra1.cdn.digitaloceanspaces[.]com/word.ppt |
| Dssmithcheck | https[://]dssmithcheck.fra1.digitaloceanspaces[.]com/track01.sql |
| Fintecgroup | https[://]fintecgroup.ams3.digitaloceanspaces[.]com/louse.msf |
| Ingretationcompatible | http[://]ingretationcompatible.sgp1.digitaloceanspaces[.]com/board.zip |
| Jackfrostgo | http[://]jackfrostgo.fra1.digitaloceanspaces[.]com/thems%20(4).cdr |
| Marthmusicclub | https[://]marthmusicclub.sfo3.digitaloceanspaces[.]com/betunios.cdr |
| Munich | https[://]munich.ams3.digitaloceanspaces[.]com/Minimize.jpeg |
| Partyprogames | https[://]partyprogames.ams3.digitaloceanspaces[.]com/bets.cdr |
| Pexelsfiles | http[://]pexelsfiles.ams3.digitaloceanspaces[.]com/pexels.ppt |
| Pratoonecooltool | https[://]pratoonecooltool.sfo3.digitaloceanspaces[.]com/national.ppt |
| Ryzemamd | https[://]ryzemamd.ams3.digitaloceanspaces[.]com/amd.cdr |
| Ryzenbootsector | http[://]ryzenbootsector.fra1.digitaloceanspaces[.]com/ryzen%20(3).zip |
| Starbuckplaylist | https[://]starbuckplaylist.ams3.digitaloceanspaces[.]com/fiis.cdr |
| Wekkword | https[://]wekkword.ams3.digitaloceanspaces[.]com/alphabet32.cdr |
| Wordcupnewsrocket | https[://]wordcupnewsrocket.ams3.digitaloceanspaces[.]com/INT64.cdr |
| Wordmusic | https[://]wordmusic.ams3.digitaloceanspaces[.]com/bestmusic.cdr |
| Workingprofstatus | https[://]ams3.digitaloceanspaces[.]com/workingprofstatus/anime.cdr |
In mid 2022, the threat group experimented with using lesser known file hosting providers, and in one case Dropbox. One provider that became increasingly popular was Timeweb, the Russian IaaS provider.
Moving into 2023, the threat group shifted from primarily using DigitalOcean Spaces to Timeweb for malware hosting and C2. Today, the actor continues to use Timeweb Cloud S3 object storage similar to how DigitalOcean was abused. Note that limited Timeweb use overlapped with DigitalOcean use since mid 2022; however, the change appears more strategic since the start of 2023. The shift away from DigitalOcean was due to increased difficulty in hosting the malware without campaign disruption.
Following this design change, a new cluster of activity can be built and linked to the same actor. The cluster makes use of new C2 servers, Timeweb Cloud malware hosting locations, and of course malware samples.
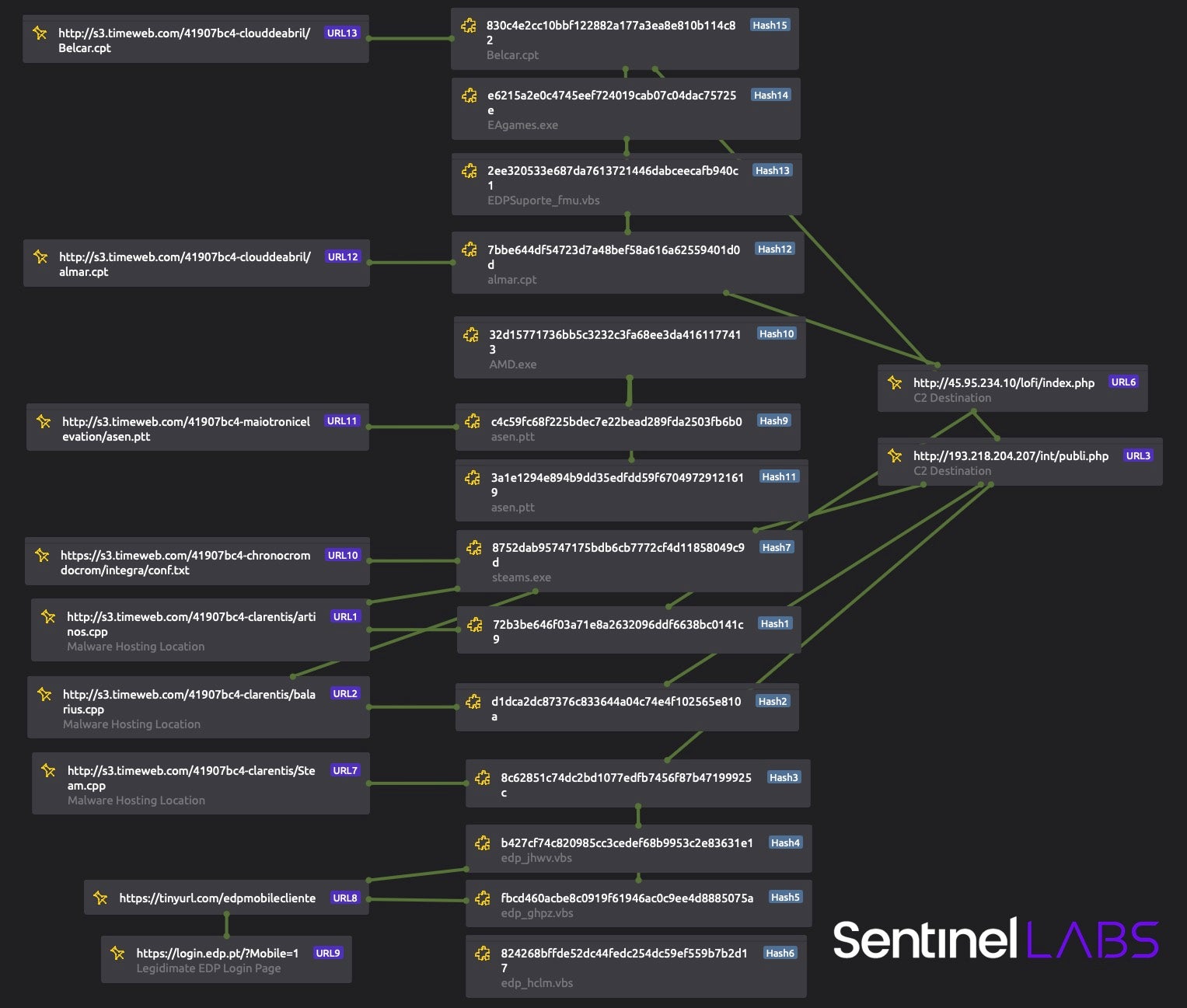
One associated server stuck out as unique – 193.218.204[.]207, which is on AS211180 for OKLAKO. Of note, the server has open directories showing a file structure and provides us some insight into backend server design and a small number of victim hosts.
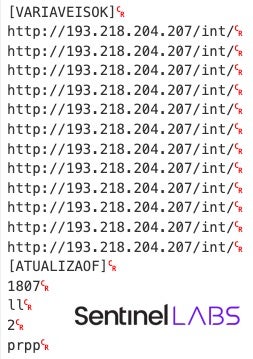
Further clues point to Brazilian-Portuguese-speaking threat actors, such as mdfiles.php returning ARQUIVO ENVIADO! (FILE SENT!) to beaconing hosts. Additionally, the publicly available file (SHA1: dff84020be1f4691bed628d300df8a8b12a4de7e) contains Base64 data, which can be decoded to show the configuration file set to beacon to 193.218.204[.]207 while also containing Brazilian-Portuguese text for VARIABLE IS OK and UPDATE.
Conclusion
Operation Magalenha indicates the persistent nature of the Brazilian threat actors. These groups represent an evolving threat to organizations and individuals in their target countries and have demonstrated a consistent capacity to update their malware arsenal and tactics, allowing them to remain effective in their campaigns.
Their capacity to orchestrate attacks in Portuguese- and Spanish-speaking countries in Europe, Central, and Latin America suggests an understanding of the local financial landscape and a willingness to invest time and resources in developing targeted campaigns. As such, it is important for organizations and individuals to remain vigilant and take proactive measures to protect themselves from this threat.
Indicators of Compromise
Below is a list of shortened URLs, SHA1 hashes (of scripts, archive files, and malware samples), and URLs (malware hosting and C2 server locations) associated with Operation Magalenha and related activities conducted by the threat group behind the operation dating back to 2022.
Shortened URLs
https[://]tinyurl.com/edpmobilecliente
https[://]tinyurl.com/dashboaraudicaofastaccoun
https[://]tinyurl.com/edpareaparticulares
https[://]tinyurl.com/miareapersonal
SHA1 Hashes
001334b045e0d1e28c260380f24c1fa072cb12eb
0131862cd70303d560d47333cce4d2b58505222e
045d5be69b5ba4ffb4253b029cc01d827706c75a
0716415bc910e4a9501d43ac03410288a4e860d4
071c53099decea6d9117e4ee519470140c68c7e9
0a202ca568087eabeb741648be4255d834ab14b1
13b370f368c1df2d30bb8fdf96d84e66e07c8a79
17fe9cdd20a64fec5d471f6878a462a2ef0af212
1a5ad2fb1d4fc4971286bdd5abf669722d7e4c19
1e65c104c765e6e46887f7de04cc14f52dbdfe98
208572a9f44d5349382c58d51d2d14532bc87bb3
266a1c4b8bd95595dcdd46bcb409ee773bd2f407
268d93bfd3f0a8a5cd76eea6311eb2a0b754a4e2
26be17aef483d553c0e5678e35611b019acd28a3
280999b0490bbe06665d35f2cda373fa32bfc59c
2ee320533e687da7613721446dabceecafb940c1
3079bba1a2372282f6bb4a35706144d5b9800953
32d15771736bb5c3232c3fa68ee3da4161177413
35597059ae1f14f50d7fe8b1858525552f62da19
3a1e1294e894b9dd35edfdd59f67049729121619
3be8f26dbc49b8a2504c58de247b838888e15a17
418fabf734c0803f2686a41665f06525cfa3adbb
41ab10d5e057e714d8caad5855c115f5bef76097
42ee272c6bc93c5c0c47024f631350c23edc06fe
43a55a5954d56c4e9fe63cfdd6ab0c97766c9642
44da6f99de08e5193a64a89ce696d775248314d9
45304d8ae20e0fcaf975be64b7844c361ae61537
470e52d04a89318a868402617b2edd16e1a20613
483a4a7e4650502e36dacde33652bf6b62718822
48e77c8ab75d042d1526fe3cd40beeea5fff7794
494d166f7b052c7feaf5666062dcf54525873ac2
4fc26b033677b6a6dc77ae3c4451d3d4421bcc04
51be9fb55ff9606b0f4e887d332608f41533215e
52d06e3b0e3b91165bdba769a94710bbdad8d8d7
542b320b77bb3f826ee17009564613352e5a4911
5c9fc5902ced06f7068f95dfa7c25c1939be3f51
5e38e6a927309aac4679a6d63c1e01b3830ca7c7
5ee9c3e8ff35bc0435d0691112d7f101856d9a51
603ac1e61a39c74d5053ccedd6964ce5f9f365f3
62a1fd987b051586132b1d1752d78821139efb7f
62b1ef509f0f9dffa611f3addface8f91089b0c3
69beb59e75f70487edbbf997aba83b926674a355
6a43e8c05194e066b85845e454d41bf86e1ab376
6a977ae1ad3466f20f50e101b5a561ad3ffc3aa7
6c3d57a7b6631adbe3b6a2c2d88eef6593c51900
6e00ef494a5955df4802c078ae3ffc6c6abdcbd7
72b3be646f03a71e8a2632096ddf6638bc0141c9
7339585c17aaa96e93f971b64548666a3b09d1f9
738aff3e88f498c3607eeadd37b95791acf40196
76b1bb307e1489999da725c2c9fac5b4581cb448
7992e075bc9de98e944930372f1768ccc08e429f
79ce7defeed60bba523bc3779cb9379435157f93
7bbe644df54723d7a48bef58a616a62559401d0d
7e82f8608c199eb32230dd2706c11b2e70ba13d8
7f3c5142f60cd36073b54eda77b38be754a5f7d5
824268bffde52dc44fedc254dc59ef559b7b2d17
830c4e2cc10bbf122882a177a3ea8e810b114c82
8752dab95747175bdb6cb7772cf4d11858049c9d
87ff9f5f3f4853d0c218ac36182fa18bc5e206d0
890c8ab68be8990deb26dab6f5c82f0a812b9fcb
8c62851c74dc2bd1077edfb7456f87b47199925c
8cc16c418764d26b15d41f713551a7d0f214ab4c
97bab3df5acbd1e4ad8b9a38cbbd80c297971490
9ab7bc8a9b4ccbc75903e78d96357e11dfd97535
9c997e9ee92209be186de2a4f9696122bdfbc46d
9eaa52e9f72f0b43648699a3a511d0a7c6ffcdd5
a0721a76cc8a0e44bf734206638ba013da809325
a28db721736fe5d6281c08b4f2f396da480eb170
a53b9e14f316a62e8c6c7a53a7c98158fda29533
a7c7233274e34b69b6c62caceebb19135f9034b2
acc753a084b8172981b3086122929eb4abde131a
afd5ccd6effb4eed6aec656a25ed869b954ee213
affcb29e3e8b510cab6b836672511bc738f2d328
b0253186f56662ecfbebf95cc91a887e161e32d3
b427cf74c820985cc3cedef68b9953c2e83631e1
b50ced2769e74050b130fbcb28c6d80880cfe612
b7ce5ab969a2088a7d6c401c72eeff63173ce491
bed147a98e6bff36cf3bccfc7640d444040e1f0c
c3aa8423bba6f01528f822eddb692ae56aa1be6b
c43f60bf6c24dd6c290b40afb26ea60094688a73
c4c59fc68f225bdec7e22bead289fda2503fb6b0
c5239a9994ca54ac08e45ce7443d9226151d0b36
cd5892ca5b21999799a04d72fb93dc815f7227aa
cdd2f94c542bf369702271cd83c6aa9ff2e595ea
d1dca2dc87376c833644a04c74e4f102565e810a
d2e078450e479a6cd3b1d95597fd2204fd370c42
d86aabf4713b18718421b5c0fd4084143d4f7f08
db9521169aaad154e31d4e573414459e26b57900
dc04ad9e1d8022a06a28d0522b2a1988c8ed4bab
dcdf79b172f340dc173d038d05c7eb826c55c3dc
dd46a9c61ad4aee2c865a4144733d1daf7d6bc79
dec59a76e8f1703d15fcb7f7532c759aaf717165
df0a90c8890f83f760e41c853d9033d3971194e9
df99c6fabdf6fc664e9c466af8a2986af0bfbfb8
dff84020be1f4691bed628d300df8a8b12a4de7e
dff84020be1f4691bed628d300df8a8b12a4de7e
e6215a2e0c4745eef724019cab07c04dac75725e
e9f9a5f559366a8e66f81d43ecc05d051b6e3853
eaa2c945b22f5c1b8bfbd6d8692826d841fc9185
f00493ea6b1a2cb50c74feb3af65bfaabf327a07
f534e0a04ceb6f3e1a10209f416675e9df127afc
f5a99ecd7847cc79210d5df505e222828ad63199
f66d71e1ab5c85ed43d21ff567ee3369fe97b6ed
f72ade72050a6ce63224aad2c7699160705b414c
f9db9f525f2bf09f2b85c91ea09f6251e00e2a95
fbcd460acbe8c0919f61946ac0c9ee4d8885075a
fff1b8681eadf590034f61ddd69ba035c6980e12
URLs
http[://]128.199.228.142/int/publi.php
http[://]128.199.228.142/itest/envd.php
http[://]128.199.228.142/lgimp/envd.php
http[://]128.199.228.142/vcpu/
http[://]128.199.68.249/libex/track01.wma
http[://]128.199.68.249/libex/track02.wma
http[://]157.245.44.246/cliente/IRS.php
http[://]157.245.44.246/fex/basf.msf
http[://]157.245.44.246/fex/coldplay.msf
http[://]176.57.221.92/cdd/
http[://]178.128.174.182/board/alf.cdr
http[://]178.128.174.182/board/bets.cdr
http[://]185.104.114.253/alp/
http[://]193.218.204.207/int/publi.php
http[://]2.59.41.206/fork/Material.psd
http[://]213.226.124.48/dboard/Material.psd
http[://]45.95.234.10/lofi/index.php
http[://]81.200.152.38:9000/arquivos
http[://]85.193.80.19/rpt/bdb.jpeg
http[://]85.193.83.224/dash/support.psd
http[://]85.193.95.154/odc/
http[://]85.217.170.140/may/
http[://]87.249.44.177/partic/Material.ppt
http[://]89.223.68.22/sonic/movie.wma
http[://]92.255.76.181/mag.psd
http[://]92.53.107.216/shv/
http[://]94.156.35.182/jn/
http[://]94.228.121.36/suport/
http[://]ingretationcompatible.sgp1.digitaloceanspaces.com/board.zip
http[://]jackfrostgo.fra1.digitaloceanspaces.com/thems%20(4).cdr
http[://]pexelsfiles.ams3.digitaloceanspaces.com/pexels.ppt
http[://]ryzenbootsector.fra1.digitaloceanspaces.com/ryzen%20(3).zip
http[://]s3.timeweb.com/41907bc4-clarentis/Steam.cpp
http[://]s3.timeweb.com/41907bc4-clarentis/artinos.cpp
http[://]s3.timeweb.com/41907bc4-clarentis/balarius.cpp
http[://]s3.timeweb.com/41907bc4-clouddeabril/Belcar.cpt
http[://]s3.timeweb.com/41907bc4-clouddeabril/almar.cpt
http[://]s3.timeweb.com/41907bc4-maiotronicelevation/asen.ptt
https[://]ams3.digitaloceanspaces.com/bucket2023/andorra.ppt
https[://]ams3.digitaloceanspaces.com/bucket2023/belize.ppt
https[://]ams3.digitaloceanspaces.com/workingprofstatus/anime.cdr
https[://]ams3.digitaloceanspaces.com/workingprofstatus/brigth.cdr
https[://]audaction.fra1.digitaloceanspaces.com/pass/alma32.cdr
https[://]audaction.fra1.digitaloceanspaces.com/pass/alma64.cdr
https[://]audaction.fra1.digitaloceanspaces.com/pass/best32.cdr
https[://]azuredatabrickstrainne.sfo3.digitaloceanspaces.com/Workspace.zip
https[://]believeonline.ams3.digitaloceanspaces.com/acoustic/p0.cdr
https[://]bucket2023.ams3.digitaloceanspaces.com/belize.ppt
https[://]cartezyan.fra1.digitaloceanspaces.com/Player.wav
https[://]cleannertools.fra1.cdn.digitaloceanspaces.com/word.ppt
https[://]digitalsurfareago.ams3.digitaloceanspaces.com/basf.msf
https[://]dssmithcheck.fra1.digitaloceanspaces.com/track01.sql
https[://]dssmithcheck.fra1.digitaloceanspaces.com/track02.sql
https[://]fintecgroup.ams3.digitaloceanspaces.com/louse.msf
https[://]fra1.digitaloceanspaces.com/dssmithcheck/track01.sql
https[://]joiasdofuturo.webcindario.com/hs/config.php
https[://]marthmusicclub.sfo3.digitaloceanspaces.com/alamis.cdr
https[://]marthmusicclub.sfo3.digitaloceanspaces.com/betunios.cdr
https[://]munich.ams3.digitaloceanspaces.com/Minimize.jpeg
https[://]partyprogames.ams3.digitaloceanspaces.com/alf.cdr
https[://]partyprogames.ams3.digitaloceanspaces.com/bets.cdr
https[://]pratoonecooltool.sfo3.digitaloceanspaces.com/inter.ppt
https[://]pratoonecooltool.sfo3.digitaloceanspaces.com/national.ppt
https[://]ryzemamd.ams3.digitaloceanspaces.com/amd.cdr
https[://]s3.timeweb.com/41907bc4-chronocromdocrom/integra/conf.txt
https[://]s3.timeweb.com/41907bc4-secapril/brexit.ppt
https[://]starbuckplaylist.ams3.digitaloceanspaces.com/fiis.cdr
https[://]starbuckplaylist.ams3.digitaloceanspaces.com/vieww.cdr
https[://]superchat.fra1.digitaloceanspaces.com/ATX.cdr
https[://]superchat.fra1.digitaloceanspaces.com/Brave.cdr
https[://]superchat.fra1.digitaloceanspaces.com/DuckDuck.cdr
https[://]superchat.fra1.digitaloceanspaces.com/pse.cdr
https[://]wekkword.ams3.digitaloceanspaces.com/alphabet32.cdr
https[://]wekkword.ams3.digitaloceanspaces.com/boston32.cdr
https[://]wordcupnewsrocket.ams3.digitaloceanspaces.com/INT64.cdr
https[://]wordcupnewsrocket.ams3.digitaloceanspaces.com/rzFMX64.cdr
https[://]wordmusic.ams3.digitaloceanspaces.com/bestmusic.cdr
https[://]www.dropbox.com/s/dl/p2qd53cultjyw6y/Dividas.zip
https[://]www.dropbox.com/s/p2qd53cultjyw6y/Dividas.zip?dl=1