labs
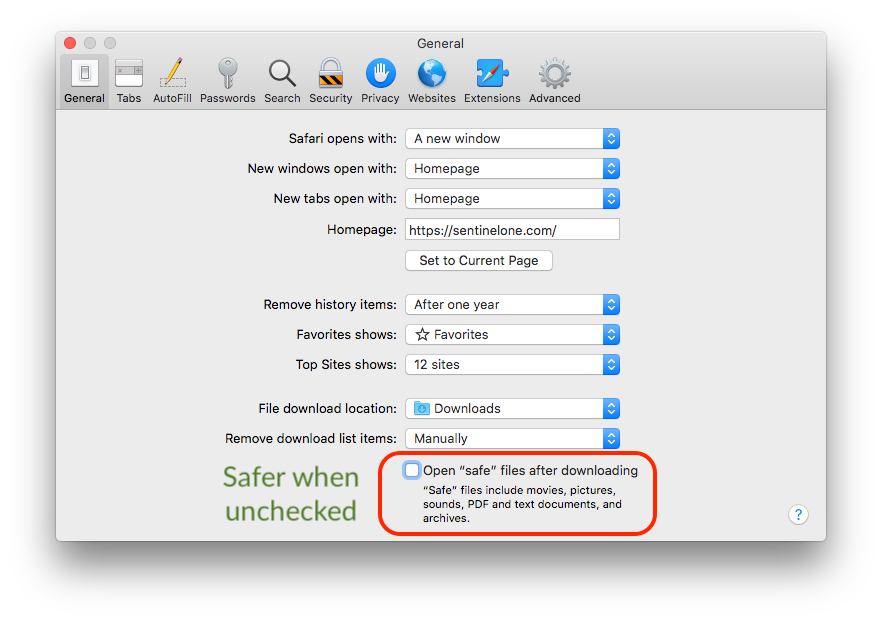
How to Reverse Malware on macOS Without Getting Infected | Part 1
Ever wanted to learn how to reverse malware on Apple macOS? This is the place to start! Join us in this 3-part series on macOS reverse engineering skills.
Read More