labs
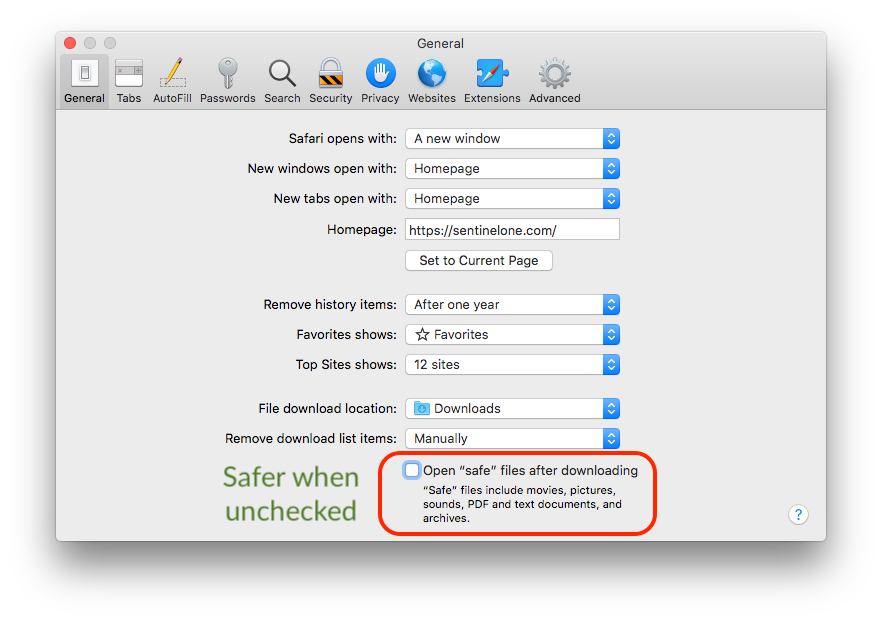
How to Reverse Malware on macOS Without Getting Infected | Part 3
Join us in the final part of our introduction to macOS malware reverse engineering as we explore LLDB, dynamic binary analysis, reading registers and more.
Read More