
labs
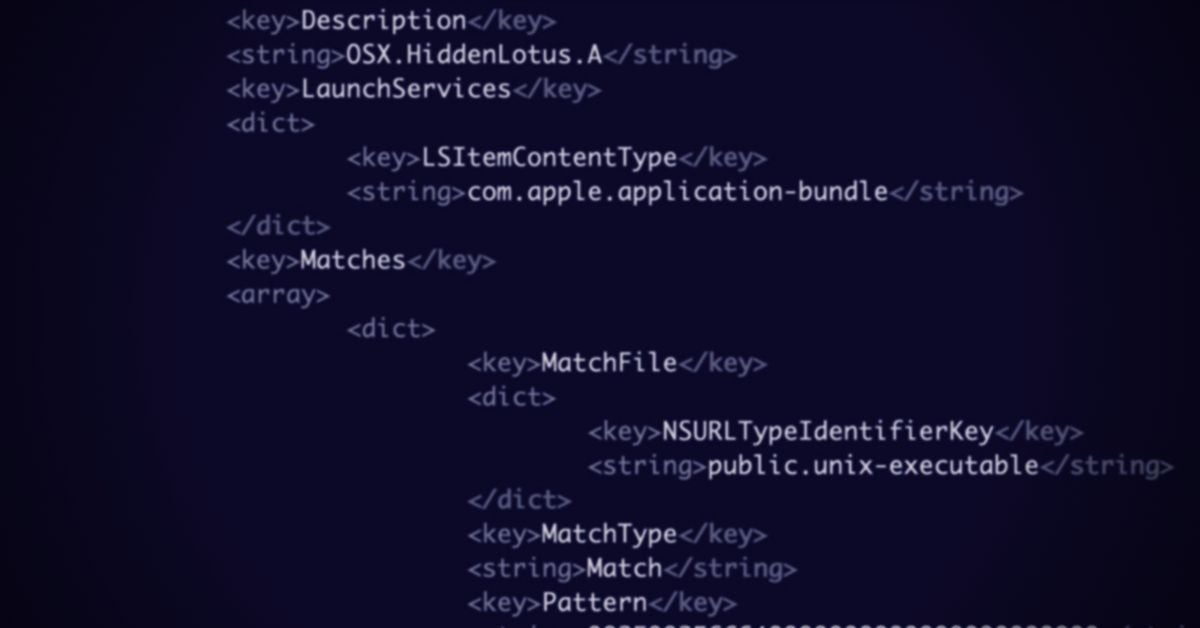
How To Bypass XProtect on macOS Catalina
macOS no longer offers an easy way to execute known malware, which hampers malware research and campaign tracking. Here's how we bypass those restrictions.
Read More

macOS no longer offers an easy way to execute known malware, which hampers malware research and campaign tracking. Here's how we bypass those restrictions.

Mozilla beefs up Firefox security, a new Wi-fi vuln hits a billion devices, and DoppelPaymer ransomware enrols stubborn victims into public 'Hall of Shame'.

Do Macs get viruses? Are Apple's built-in tools robust enough to prevent an attack? And how would you know if your Macs were compromised, anyway?

Microsoft and others go on a bug-fixing spree, Emotet worms its way into nearby Wifi networks, and the US breaks crypto to spy on allies and enemies alike.

Nintendo hacker gets taught a lesson by the FBI, IoT devices on Windows 7 hit by Lemon Duck malware and Huawei complain about "unconstitutional" FCC label.
Understanding macOS security tools is vital for researchers and defenders. With Apple's unique telemetry, they may hold the first clue to emerging threats.

Threat actors on macOS increasingly rely on shell scripts as an effective way to deliver malware installers that trick users and bypass security controls.

The cybersecurity skills shortage gets a much-needed boost, the NSA reveal a critical Windows Crypto bug, and researchers dump dangerous Citrix exploit code.

Fighting malware on macOS? It'd help if we knew what Apple knew. Here we offer a tool and process to help keep up with changes to Malware Removal Tool.

Facebook initiates a ban on deepfakes, Mozilla rush out a patch for in-the-wild exploit and a US government-funded phone comes with preinstalled malware.