
labs
15 macOS Power Tricks for Security Pros
No matter how long you use macOS, there's always some new trick to learn, some undiscovered tool, or some better way to accomplish a routine task.
Read More

No matter how long you use macOS, there's always some new trick to learn, some undiscovered tool, or some better way to accomplish a routine task.

Cops take down ransomware gang targeting hospitals, Winnti hacker group takes aim at game developers and new ShinyHunters data broker emerges on the darknet.
New to macOS and wondering what tools are available for security researchers and infosec practitioners? Here's our guide to some of the best tools and apps.

It's not only by downloading cracked sofware that unwary Apple Mac users end up with a dose of malware. Let's explore how bad actors target macOS in the wild.

Shade ransomware appears to bow out, critical vulns found in MS Teams and Sophos firewall products, and the Maze crew threaten to leak 11m credit card creds.

A university transitions 22,000 to full remote in a week, a new IoT botnet kills rivals and prevents reboots, and scammers target ethical hacker wannabes.

A recent update to a notorious macOS browser hijacker exfiltrates data about the device environment and installed apps. Now what could they want that for?

Police arrest two gangs of SIM Swappers, ransomware vendors take note of COVID-19, and 5 billion data breach records are found on an unsecured repository.
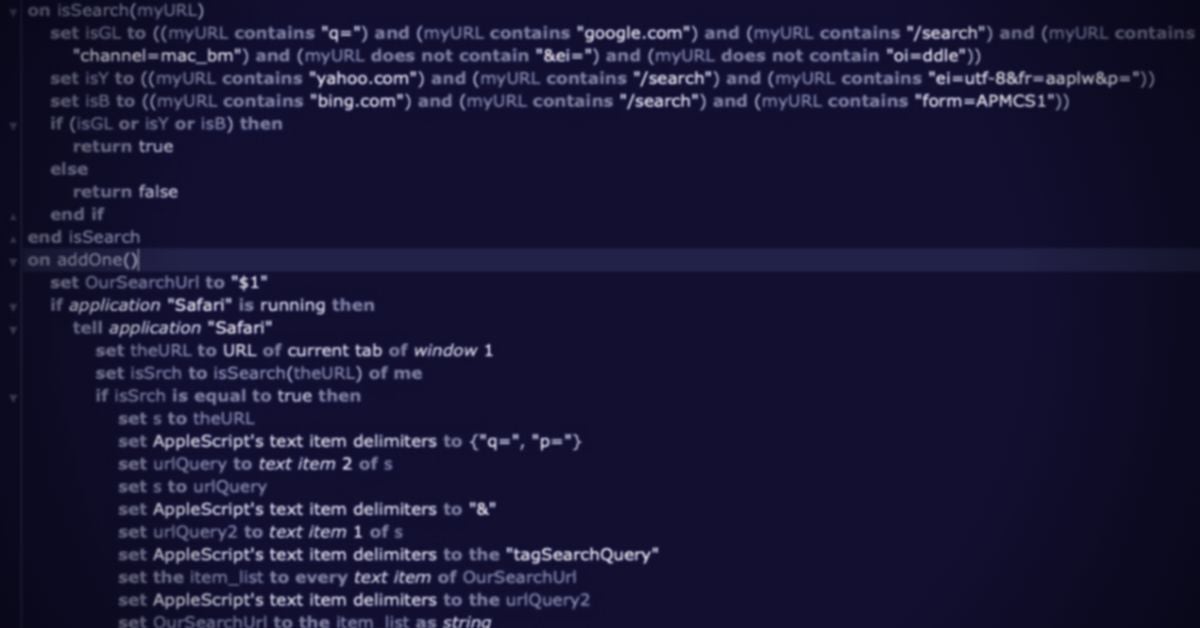
AppleScript is widely used by threat actors and yet widely ignored by security researchers. Here's why we need to rethink our attitude to this unique tool.

macOS no longer offers an easy way to execute known malware, which hampers malware research and campaign tracking. Here's how we bypass those restrictions.