
labs
The Good, the Bad and the Ugly in Cybersecurity – Week 2
Cops bust crimeware gang in Kyiv, Texas firm bankrupt after paying ransom but getting no data returned, and MS Defender has simple bypass known for 8 years.
Read More

Cops bust crimeware gang in Kyiv, Texas firm bankrupt after paying ransom but getting no data returned, and MS Defender has simple bypass known for 8 years.

Mac adware is hidden, persistent, and evasive, fingerprinting devices and delivering custom payloads. Learn how to hunt it on macOS.

51 individuals arrested for trading stolen data, the internet explodes with fears over Java logging vuln, and NSO's iMessage exploit is a monster to behold.

Learn about all the new malware targeting macOS in 2021, and the changing tactics, techniques and procedures being employed by threat actors.

Cyber cops nab 1000 fraudsters in 20 countries, critical printer bug allows for remote attacks, and new phishing lures exploit Omicron fears.

UK's NCSC wages war on phishing, "move over SquirrelWaffle", Emotet is back, and Iranian APTs exploit Microsoft bugs to drop ransomware.

Novel macOS malware installs a keylogger and AV capture components on activists' devices. How can Mac users detect such behavior before it's too late?
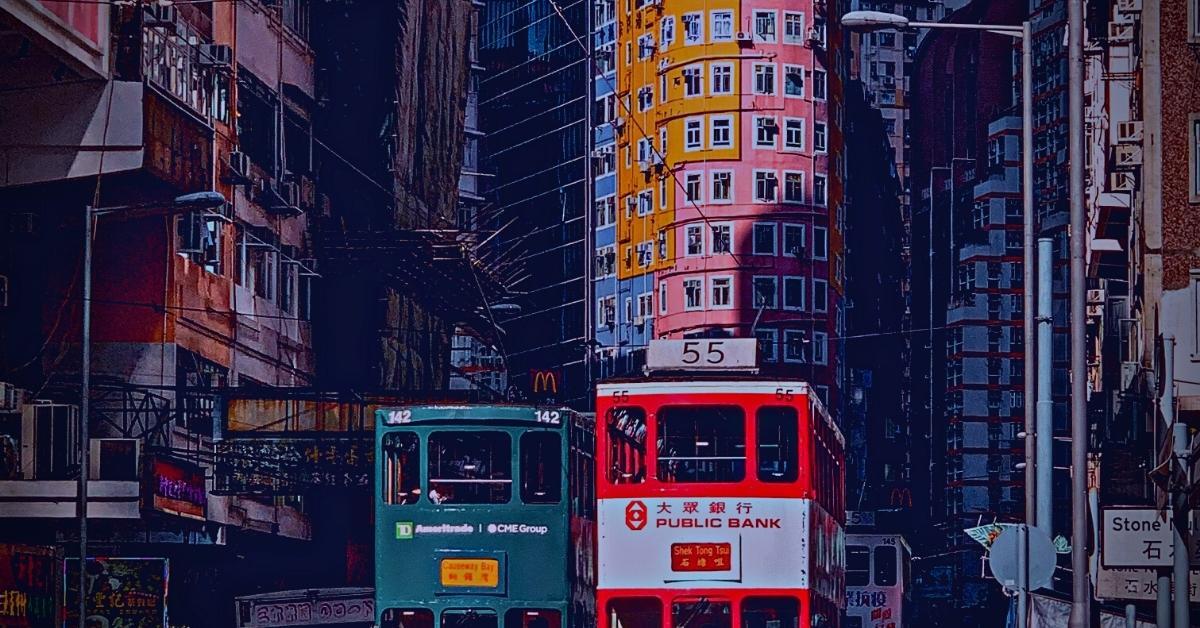
SentinelLabs reveals further IoCs, behavior and analysis around suspected APT attack targeting macOS users and Hong Kong pro-democracy activists.

It's armageddon for Gamaredon after SSU outing, ransomware gang may have snagged cancer patients' PII, and medical students face fraud risk after data leak.
Apple's annual macOS upgrade is here, fully supported by SentinelOne, and with a few changes since the early betas. Are you ready for macOS Monterey?