
labs
The Good, the Bad and the Ugly in Cybersecurity – Week 8
Ring rolls out extra security with mandatory MFA, ransomware hits U.S natural gas plant and Russian APT gets called out for attacks on Georgian TV stations.
Read More

Ring rolls out extra security with mandatory MFA, ransomware hits U.S natural gas plant and Russian APT gets called out for attacks on Georgian TV stations.

Magecart e-commerce malware gets disrupted by Interpol, Emotet trojan exploits coronavirus health scare and AV Vendor sells users' data to Google and others.

The ransomware crime spree continues with threat actors increasingly turning to Golang as their language of choice. New entrant Snake is just the latest.

Sophisticated hackers compromise MSPs and other businesses, then sell access to low-level criminals. Take a look inside the trade and learn how to stay safe

GozNym malware authors get jail time, a critical flaw puts 80,000+ Citrix servers at risk and Chinese-backed APT20 hackers find their way past 2FA.

A look inside the alarming rise of RaaS projects offering "No Coding Skill Required" ransomware and using slick marketing tricks to tempt would-be criminals.
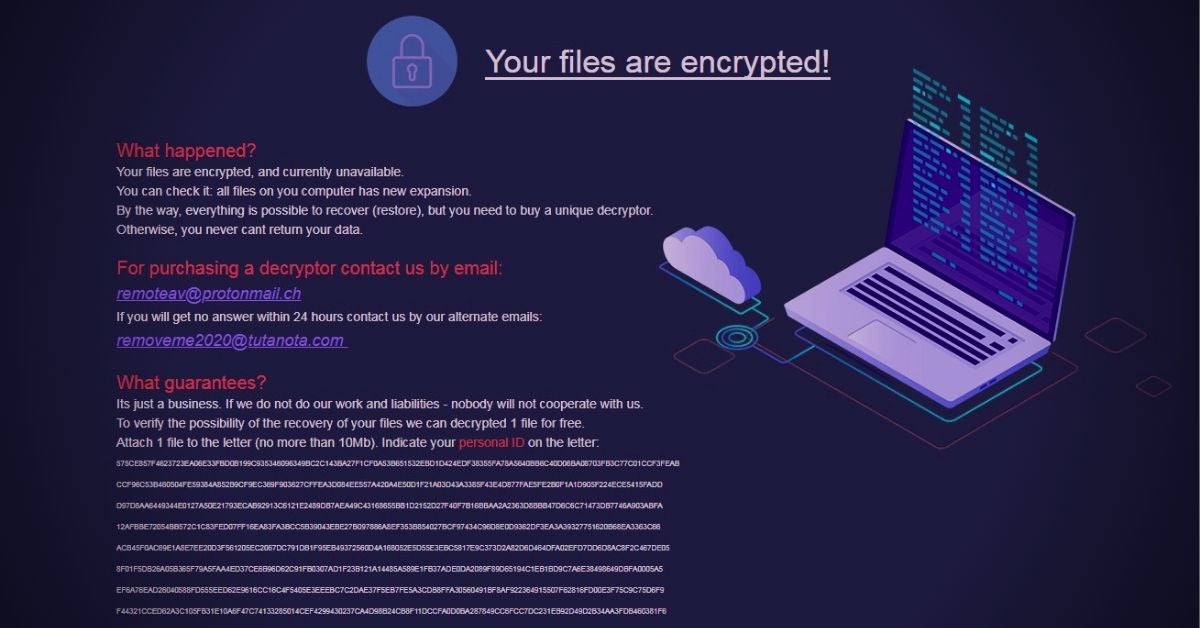
MedusaLocker aggressively scans remote drives, keeps searching for new files to encrypt. What's behind the latest strain of malware to bypass legacy AV?

Louisiana State gets one over on Ryuk ransomware, cryptocurrency users get served malware and a video sharing site exposes its users' naked secrets.
In Part 2 of our Ransomware As A Service (RaaS) series, we look at Project Root's offline builder & how threat actors can easily customize the source code.

Google Play Store gets new security checks, ransomware keeps on rolling and scammers target Trend Micro customers with perfect storm tech support scam.