
labs
Another Brick in the Wall: Uncovering SMM Vulnerabilities in HP Firmware
How we used Brick to discover six different vulnerabilities affecting HP laptops' firmware
Read More

How we used Brick to discover six different vulnerabilities affecting HP laptops' firmware

In Part 5 of our ongoing series on UEFI security research, we dive into the fascinating world of hunting and exploiting SMM vulnerabilities.
In Part 4 of our UEFI Internals and Exploitation series, we abandon VMs and dive into UEFI on a physical machine. The quest: recovery of the S3 Boot Script.
In Part 3 of our series on emulating, debugging and fuzzing UEFI modules, we provide a step-by-step guide to making a coverage-guided fuzzer for UEFI code.

Learn how to emulate, trace, debug, and Reverse Engineer UEFI modules in part 2 of our new blog series on Firmware Security

The first in a series of posts for researchers on how to emulate, debug and fuzz UEFI modules, we begin with a refresher on how to dump SPI flash memory.

In the 2nd research of SKREAM, our researchers suggest a generic way to mitigate pool overflow vulnerabilities, based on randomizing the pool allocation
This article presents a Windows kernel exploitation technique and suggests a method to mitigate the vulnerability that enables it
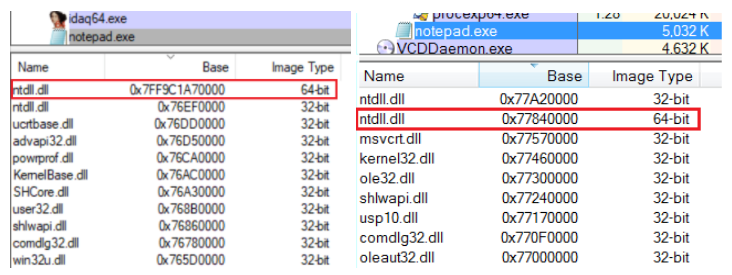
Introduction Last time (part 1, part 2) we demonstrated several different methods for injecting 64-bit modules into WoW64 processes. This post will pick up where we left off and describe how the ability to execute 64-bit code in such processes can be leveraged to hook native x64 APIs. To accomplish this task, the injected DLL […]
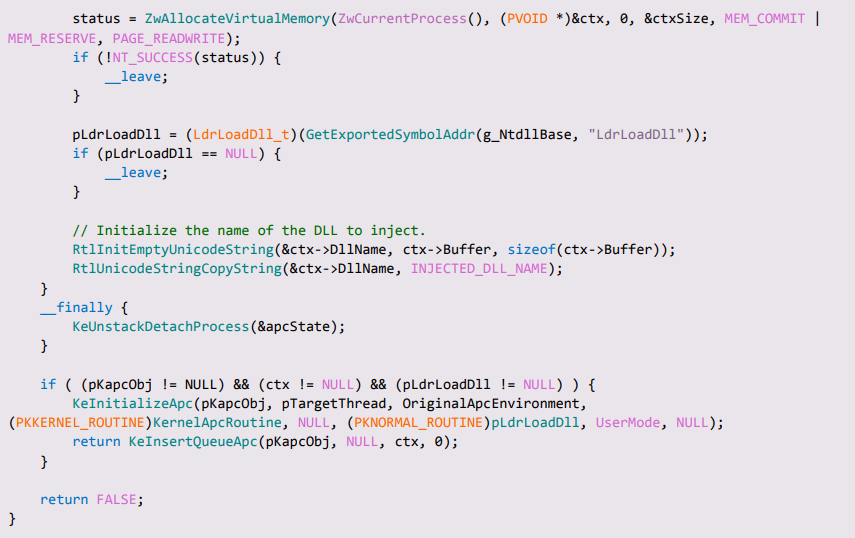
Where we left off In the first part of this series we presented several injection methods capable of injecting 64-bit DLLs into WoW64 processes, with the intention to eventually use this DLL to hook 64-bit API functions in the process. We finished the post by presenting injection via APC, and saw that, when tested to […]