
labs
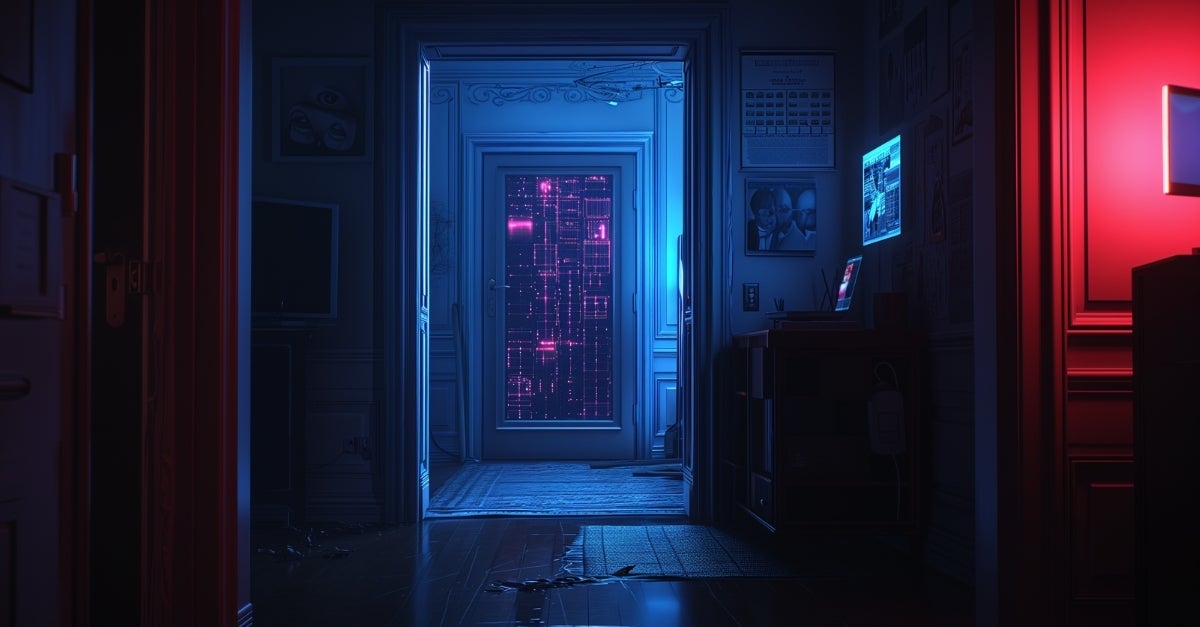
macOS NotLockBit | Evolving Ransomware Samples Suggest a Threat Actor Sharpening Its Tools
An unknown threat actor is developing ransomware to lock files and steal data on macOS, and it's not LockBit.
Read More

An unknown threat actor is developing ransomware to lock files and steal data on macOS, and it's not LockBit.

Monday September 16th saw Apple release the newest version of its Mac operating system, macOS 15 Sequoia, and SentinelOne was delighted to announce support for this version of macOS on the day of release.

Keeping track of the many variants of Atomic Stealer can be a challenge for SOC teams. Our guide breaks down the latest versions.

We teamed up with VirusTotal to take a deep dive into the platform's extensive query capabilities through both the web and API interfaces.

Learn about the mechanics of macOS Cuckoo Stealer, discover extended indicators and ensure your organization remains protected.

Learn about the latest Adload adware variants, written in Go and intended to bypass Apple's recent XProtect updates.
A new campaign is spreading macOS malware through infected copies of popular applications and productivity tools.

Learn about the latest threats to macOS as Infostealers continue to rapidly adapt to evade static signatures.

The rise of macOS infostealers continues with the latest entrant aiming to compromise business environments with targeted social engineering lures.

What can defenders learn from last year's bumper crop of macOS malware? Bolster your defenses with these insights into the latest attacker trends.